Meltdown and Spectre exploits impact Intel, ARM, and AMD processors
After initial reports suggested a new security flaw was confined to Intel systems, researchers have now disclosed that nearly all modern processors are affected via a second exploit.
Security researchers have disclosed two new exploits that can be executed against modern processors. Dubbed Meltdown and Spectre, the exploits use similar methods to impact processors from Intel, AMD, and ARM across PCs, mobile devices, and in the cloud. The researchers explain:
Meltdown and Spectre exploit critical vulnerabilities in modern processors. These hardware bugs allow programs to steal data which is currently processed on the computer. While programs are typically not permitted to read data from other programs, a malicious program can exploit Meltdown and Spectre to get hold of secrets stored in the memory of other running programs. This might include your passwords stored in a password manager or browser, your personal photos, emails, instant messages and even business-critical documents.
Meltdown and Spectre are both distinct attacks, but they both allow attackers to break isolation between applications to access information.
Perhaps the most distinct difference, however, is the specific processors affected by each attack.


Meltdown, the researchers say, has only been assessed to impact Intel processors. However, the range of potentially affected processors is vast.
More technically, every Intel processor which implements out-of-order execution is potentially affected, which is effectively every processor since 1995 (except Intel Itanium and Intel Atom before 2013). We successfully tested Meltdown on Intel processor generations released as early as 2011. Currently, we have only verified Meltdown on Intel processors. At the moment, it is unclear whether ARM and AMD processors are also affected by Meltdown.
Spectre, on the other hand, appears to have a much wider reach. According to researchers, nearly every type of device is affected by Spectre; it has been verified to work across Intel, AMD, and ARM processors. Spectre is harder to exploit than Meltdown, but researchers caution that it is also harder to guard against.
The attacks also work against cloud servers, which could leave customer data vulnerable.
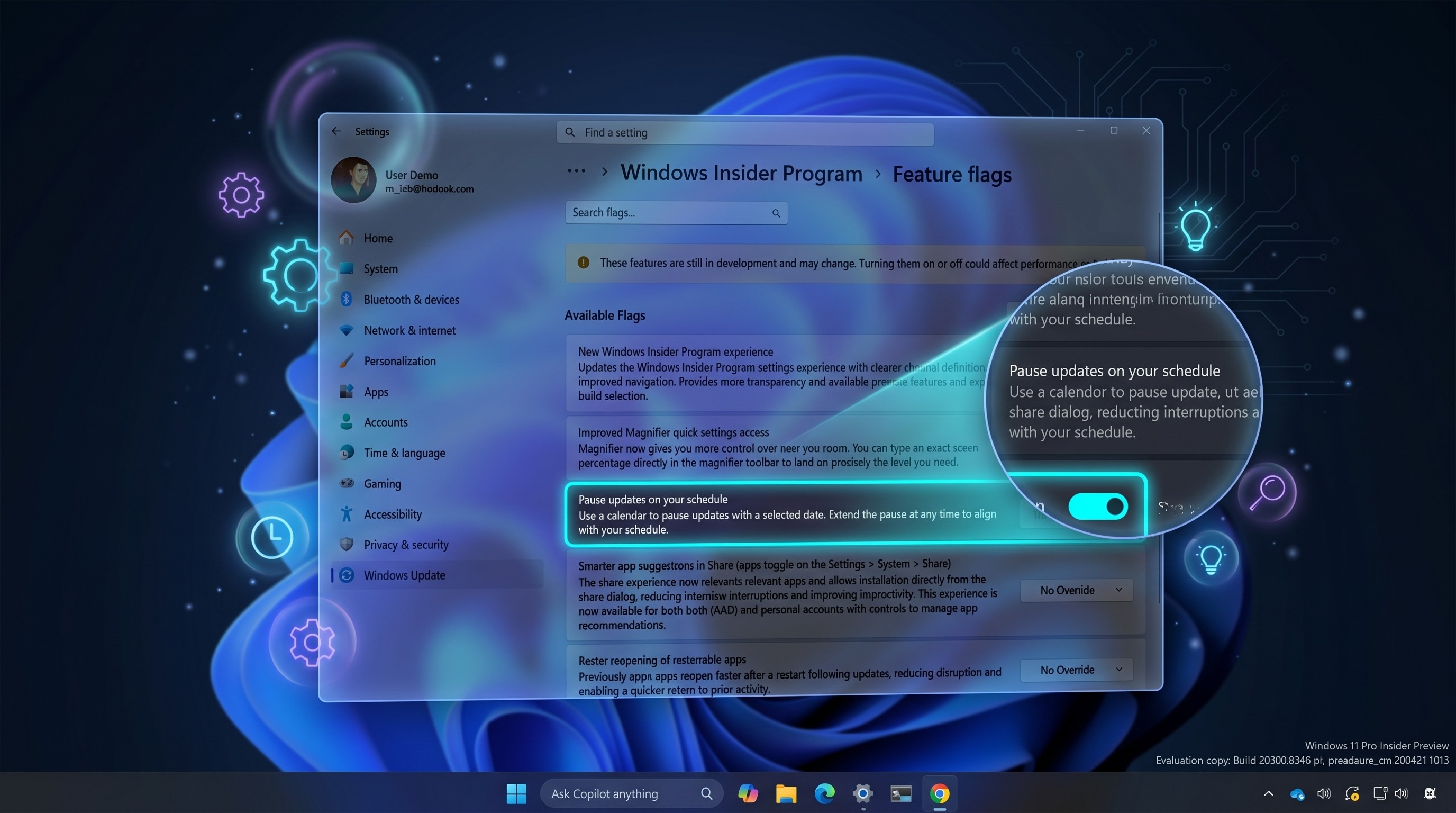
Fortunately, at least some fixes are on the way. There are patches against Meltdown for Linux, Windows, and macOS, and Microsoft is currently rolling out an emergency patch for the issue. Spectre is not an easy fix, it seems, and the researchers say that there is ongoing work to "harden software against future exploitation of Spectre, respectively to patch software after exploitation through Spectre."
All the latest news, reviews, and guides for Windows and Xbox diehards.
You can read more on Spectre and Meltdown, including more technical details, in the researchers' full report.

Dan Thorp-Lancaster is the former Editor-in-Chief of Windows Central. He began working with Windows Central, Android Central, and iMore as a news writer in 2014 and is obsessed with tech of all sorts. You can follow Dan on Twitter @DthorpL and Instagram @heyitsdtl.

 Windows Central Insider
Windows Central Insider