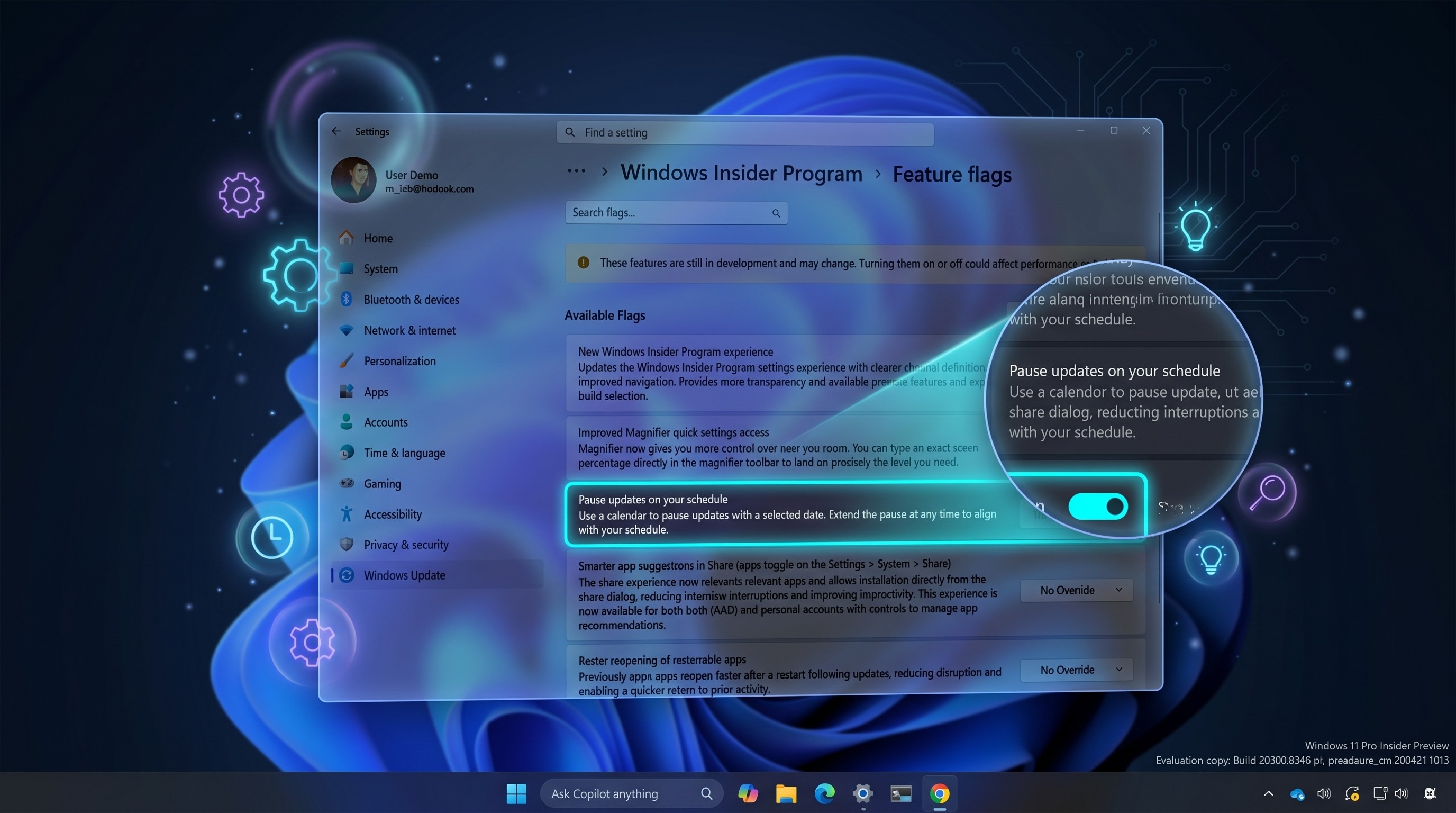
Intel says its patches will make PCs 'immune' to Meltdown and Spectre exploits
Intel now says its patches will make PCs "immune" to the recently disclosed Meltdown and Spectre exploits.
Intel has issued a new statement in response to the rapidly evolving situation around the Meltdown and Spectre processor exploits that security researchers disclosed yesterday. In its statement, Intel says that it is in the process of issuing updates to Intel-based systems that will make them "immune" to both exploits.
From Intel:
Intel has developed and is rapidly issuing updates for all types of Intel-based computer systems — including personal computers and servers — that render those systems immune from both exploits (referred to as "Spectre" and "Meltdown") reported by Google Project Zero. Intel and its partners have made significant progress in deploying updates as both software patches and firmware updates.
Further, Intel says that it expects to have patches issued for more than 90 percent of processors introduced in the past five years by the end of next week. This is in addition to patches and updates issued by other companies and manufacturers, including and emergency patch already issued by Microsoft for Windows users.


Intel has been seen as the hardest hit by news of the exploits. Prior to the disclosure from security researchers, reporting suggested that there was a single exploit that only impacted Intel processors. Later, it as revealed that there were actually two related exploits which, between them, impacted most modern processors from Intel, AMD, and ARM, to some extent.
According to information from researchers, Meltdown, which only impacts Intel processors, appears to be the easiest to deal with, with patches in the wild for Linux, Windows, and macOS. Spectre, which applies to Intel, ARM, and AMD processors, appears to be much harder to fix (though, it is harder to exploit), but steps are being taken to mitigate its effects.
For its part, AMD said in a statement to Fortune that its chips are affected, but it believes that there is a "near zero risk to AMD processors at this time."
There's still a fair amount of confusion around Meltdown and Spectre as information continues to come out. That includes questions around a potential performance impact caused by fixes for the exploits, a claim that first apppeared in The Register ahead of the exploits' disclosure and has since been downplayed by Intel. As for Intel's claims that its patches will make its chips "immune" to both Meltdown and Spectre, we'll have to wait and see.
All the latest news, reviews, and guides for Windows and Xbox diehards.

Dan Thorp-Lancaster is the former Editor-in-Chief of Windows Central. He began working with Windows Central, Android Central, and iMore as a news writer in 2014 and is obsessed with tech of all sorts. You can follow Dan on Twitter @DthorpL and Instagram @heyitsdtl.

 Windows Central Insider
Windows Central Insider