BitLocker is one of Windows 11's most important security features, yet it doesn't always get the attention it deserves. Available in Pro, Enterprise, and Education editions of Windows 11, BitLocker offers full drive encryption to keep your data safe even if your PC is stolen or lost.
I've put together this guide with advanced tips to help all types of users get the most out of BitLocker.
Tips for storing BitLocker recovery keys
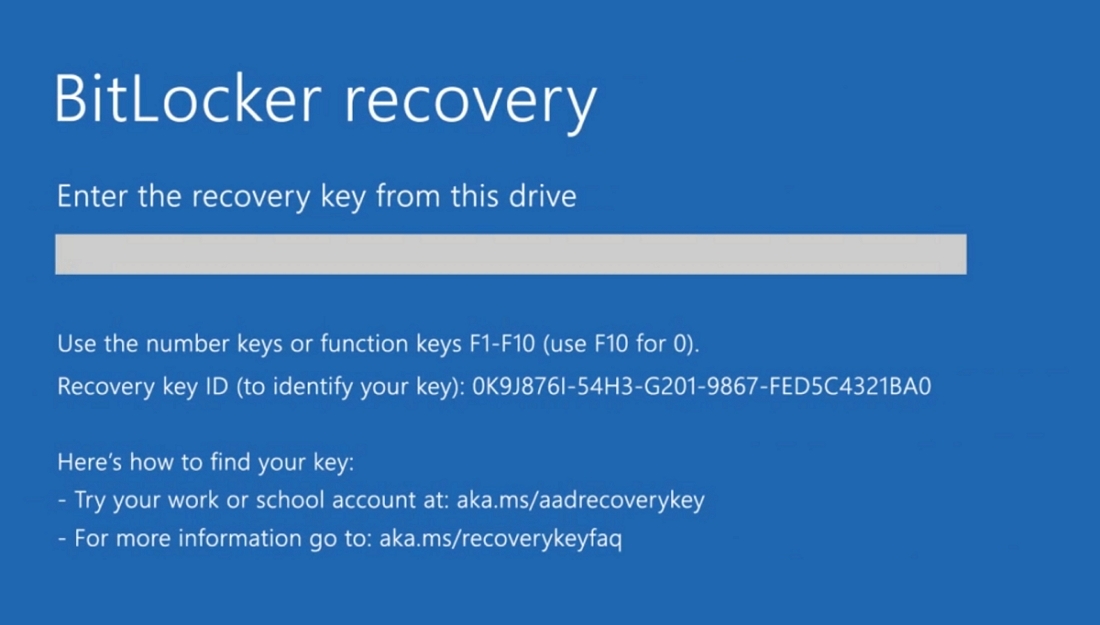
BitLocker recovery keys should never be taken lightly. They're essentially all that separates you from a forgotten PIN or other malfunction and a locked drive.
Even if BitLocker is configured properly, a recovery key might be requested after a user forgets their PIN, the PC's TPM chip resets, or the system's BIOS/firmware updates. Should a recovery key not be available, the user is effectively locked out for good.
👉 How to configure BitLocker encryption on Windows 11
Link your BitLocker recovery key to your Microsoft account
The first line of defense against a forgotten BitLocker recovery key should be your Microsoft account. You can link your recovery key to your account during BitLocker setup, making it easy to recover your drive once you're signed in.
Store your BitLocker recovery key in a password manager
You might also consider storing your BitLocker recovery key in a password manager. Something like DashLane or LastPass, which have their own capable encryption, keeps your recovery key safe for when you need it.
Store your BitLocker recovery key on an encrypted USB drive

If you'd rather rely on an air-gapped or offline solution, an encrypted USB drive can be used to store your BitLocker recovery key. Protect it with its own password not used anywhere else.
Consider split custody for BitLocker recovery keys
Going one step further, you might consider split custody of a BitLocker recovery key using something like a Hardware Security Module (HSM) or other type of encrypted storage. Since it requires two people to unlock, you can be sure that one bad actor won't compromise security.
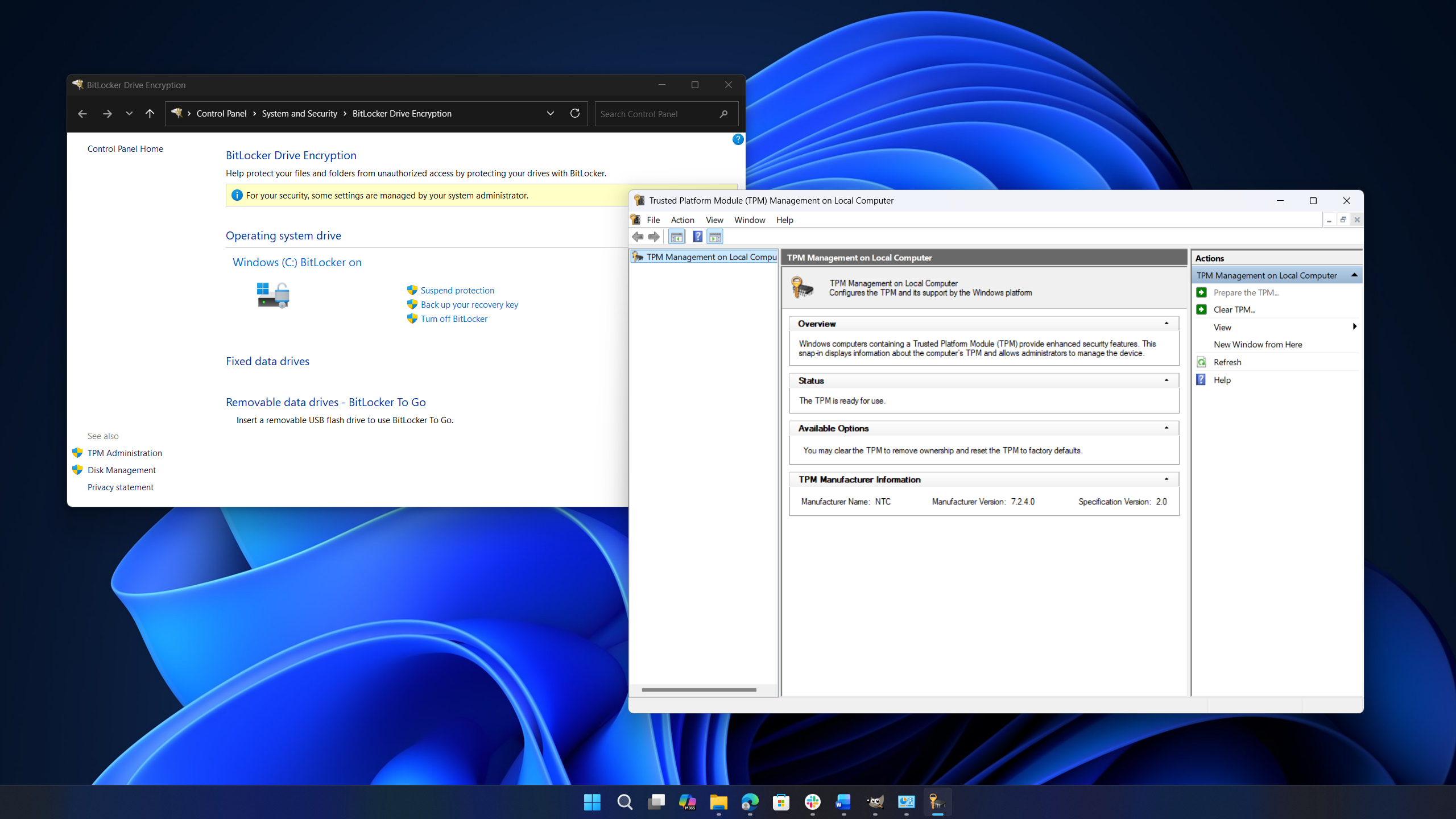
Suspend BitLocker before major system updates
Because BitLocker can reset itself and require a recovery key after major system updates to BIOS or firmware, it's recommended that you temporarily suspend the drive encryption before the update occurs. The same goes for when you're required to clear the PC's TPM.
This can be achieved via Control Panel > System and Security > BitLocker Drive Encryption > Suspend protection.
Tips for handling BitLocker recovery keys in enterprise environments
For enterprise BitLocker use, recovery keys should always be managed centrally by administrators using Active Directory Domain Service (AD DS) or Entra ID (Azure AD). They should also be backed up automatically whenever a PC is enabled in order to prevent lockouts.
These two measures alone can significantly reduce the time spent fixing user errors, and they can also help ensure compliance with enterprise security policies.
When enabling these policies, be sure to disable local encryption options for end users. This will ensure that BitLocker can only turn on once a recovery key is stored under an admin's purview.
Limit access to BitLocker recovery keys
Creating and storing BitLocker keys is only half the battle. Leaving key retrieval open to end users can pose a significant threat, which is why it's recommended that self-service retrieval be disabled.
When using Entra ID/Intune for recovery key storage, setting up a Role-Based Access Control (RBAC) will prevent unauthorized access. This will also make access audits a breeze.
Tips for properly configuring your PC's TPM for BitLocker
BitLocker relies heavily on your PC's Trusted Platform Module (TPM), a specialized piece of hardware that acts as a vault for your most important credentials.
When used with BitLocker, it ensures that your PC will only unlock when the system's boot sequence goes as expected. Although the TPM often gets ignored, it's a crucial part of your PC's security and should be treated as such.
👉 How to check if your PC has a trusted platform module (TPM)
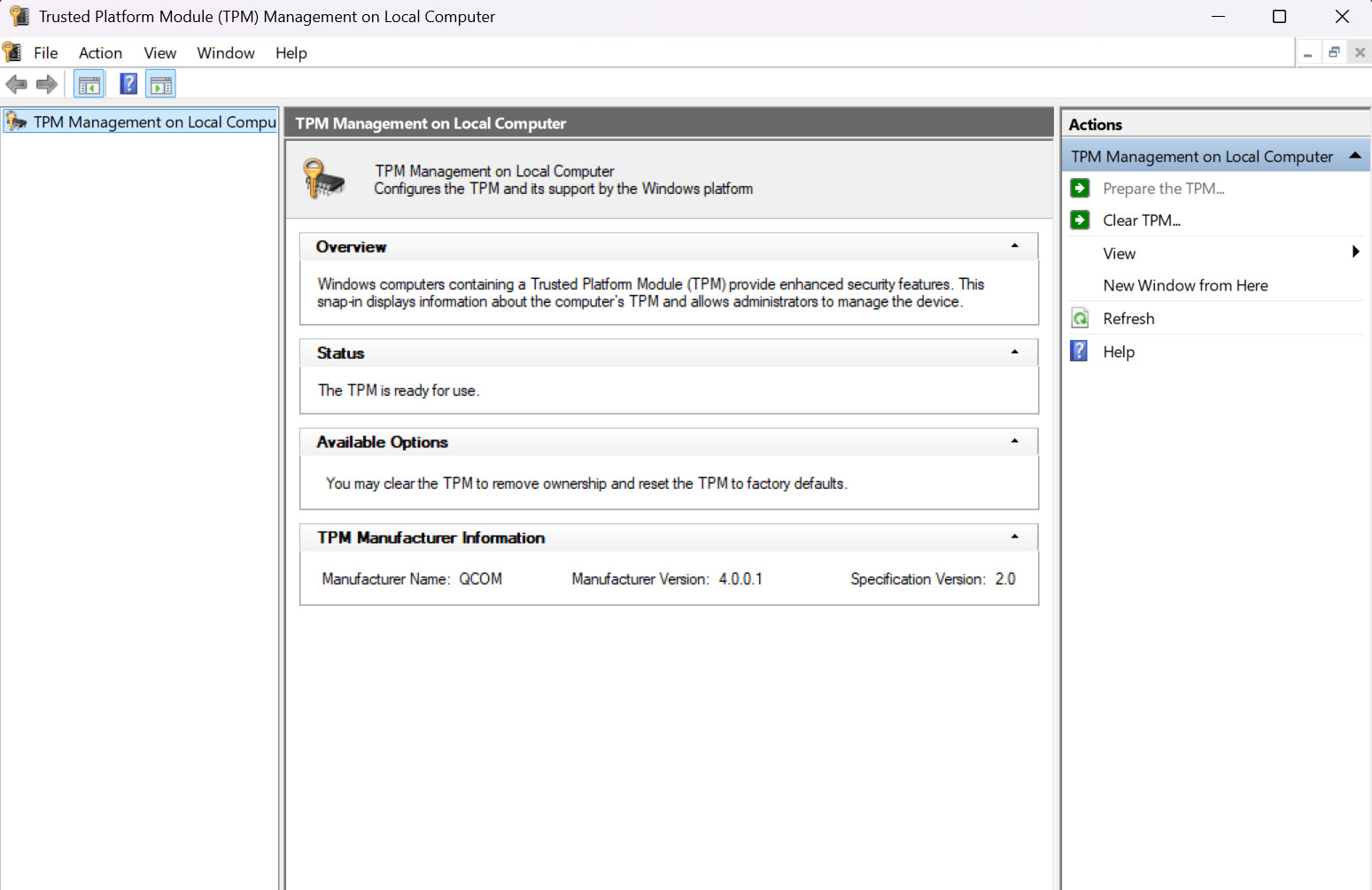
Verify your PC's TPM health
Before you enable BitLocker on your PC, it's always recommended that you check TPM health. A working TPM from the start ensures that you won't get thrown into any boot loops or wind up with a missing key.
Here's how to quickly check your PC's TPM health.
- Hit Win + R on your keyboard to bring up the Run window.
- Type tpm.msc and hit Enter on your keyboard.
This will open a new window displaying TPM details. In the Status section, it should read "The TPM is ready for use."
This is also a perfect opportunity to check the TPM specification version. BitLocker works best with TPM 2.0, which is also a requirement for installing Windows 11. If you have an older TPM chip, BitLocker will still work with reduced functionality.
Ensure the TPM is enabled before turning on BitLocker
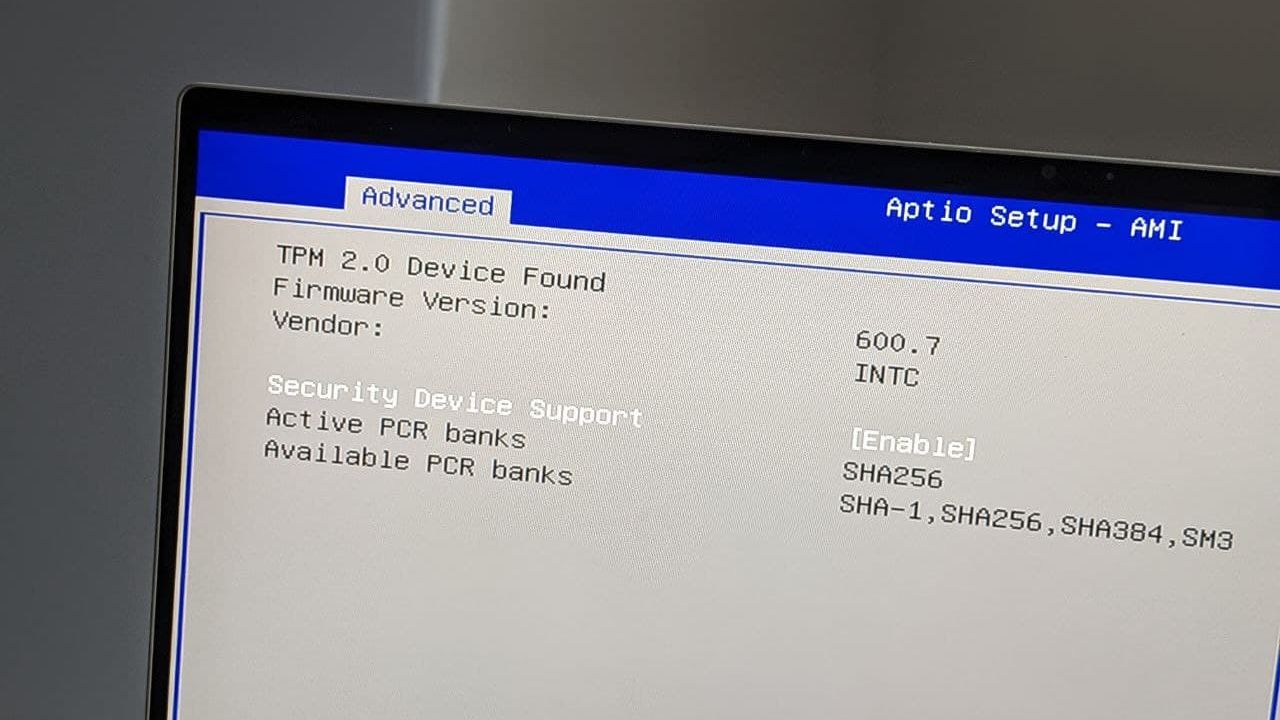
In some cases, your PC might have a TPM chip that's not enabled. Forcing BitLocker to run in this scenario is not recommended and can seriously complicate recovery efforts.
To enable a TPM, you'll need to take a trip into your PC's BIOS. Enable the TPM from there, set a password (if required), and reboot before proceeding normally.
👉 How to enable the Trusted Platform Module (TPM) on your computer
Enable TPM+PIN security for BitLocker
The TPM chip in your PC is designed to unlock your encrypted drive automatically when you boot your PC. While convenient, you can add extra security with a TPM+PIN option in BitLocker upon setting it up.
This two-factor authentication process blocks unauthorized boot attempts if a PIN is not provided. This stops automated unlock attempts (the TPM will cut off PIN attempts after a certain number) and ensures that your PC doesn't have its boot sequence hijacked.
TPM tips for enterprise BitLocker
The TPM tips provided above largely also apply to enterprise environments. PCs in use by employees should have their TPM configured properly before assignment in order to avoid complications.
For PCs that leave the office, it's especially important to set up TPM+PIN dual-factor security to avoid security issues when a device is stolen or lost.
Updates should be timed appropriately, and BitLocker should be disabled before they're pushed out to avoid unnecessary recovery steps.
Enforce centralized policies for TPM and BitLocker
When dealing with a large fleet of PCs, setting up centralized enforcement and monitoring of TPM status via Group Policy is always recommended. This ensures that there are no gaps in security and that BitLocker is able to function properly across all PCs.
Mistakes will still happen, but having a defined recovery process will ease the pain. Don't forget to test it out regularly to ensure it's ready to go when you need it.

Cale Hunt brings to Windows Central more than nine years of experience writing about PC gaming, Windows laptops, accessories, and beyond. If it runs Windows or in some way complements the hardware, there’s a good chance he knows about it, has written about it, or is already busy testing it.

 Windows Central Insider
Windows Central Insider