Massive new ransomware attack making its way around the globe

Just a month after the massive WannaCry ransomware attack hit computers around the world, it appears another attack is underway across Europe and around the globe. As reported by The Verge, Ukraine appears to be the hardest hit for the moment, with its central bank, Kiev metro, Boryspil airport, and a major power supplier all being affected.
Meanwhile, Maersk, based in Denmark, has confirmed its systems are down due to a cyberattack, and even Russian oil company Rosneft has been affected. The Verge also notes sporadic reports of infections are popping up across the UK and France. Sky News has now confirmed that British advertising firm WPP has been hit with a cyberattack as well.
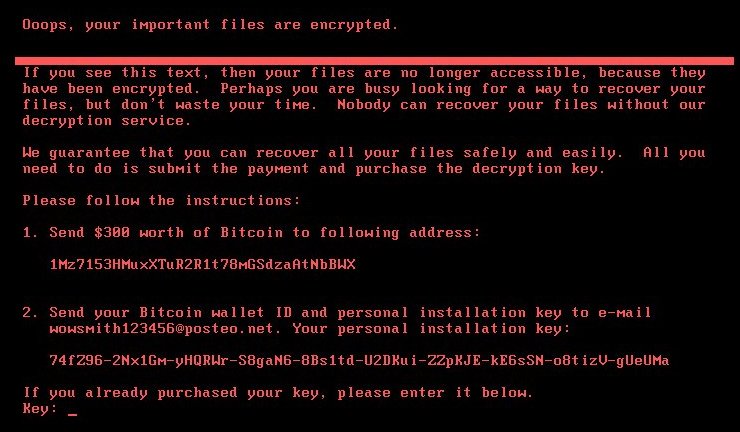
A Kaspersky Lab researcher on Twitter identified the culprit as a ransomware known as PetrWrap, or Petya. Symantec has since confirmed that the malware is using the same attack vector as WannaCry, which utilized a leaked National Security Agency (NSA) exploit known as Eternal Blue. Bitdefender has identified this particular attack as a strain of Petya known as GoldenEye, which encrypts both the files on a drive and the drive itself. After encryption, the ransomware asks for $300 in Bitcoin to decrypt the PC.


It's not clear just how widespread the problem is at the moment, but the attack has already spread to a number of big companies around the globe, including Merck and Mars Inc, since initially being reported. Last month's WannaCry attack was estimated to have impacted hundreds of thousands of PCs across Europe. That attack was eventually linked back to a group thought to be working out of North Korea, though this latest attack is of unknown origins for the moment.
While security firms recommend you refrain from paying the ransom, it turns out that would be useless at this point anyway. The email provider behind the account used for sending decryption keys has blocked the account, meaning anyone who has already paid the ransom wasted their money.
For its part, Ukraine is taking the attack in stride, posting the following to Twitter:
Some of our gov agencies, private firms were hit by a virus. No need to panic, we're putting utmost efforts to tackle the issue 👌 pic.twitter.com/RsDnwZD5OjSome of our gov agencies, private firms were hit by a virus. No need to panic, we're putting utmost efforts to tackle the issue 👌 pic.twitter.com/RsDnwZD5Oj— Ukraine / Україна (@Ukraine) June 27, 2017June 27, 2017
In a statement to the Verge, Microsoft commented about the new thread:
All the latest news, reviews, and guides for Windows and Xbox diehards.
Our initial analysis found that the ransomware uses multiple techniques to spread, including one which was addressed by a security update previously provided for all platforms from Windows XP to Windows 10 (MS17-010). As ransomware also typically spreads via email, customers should exercise caution when opening unknown files. We are continuing to investigate and will take appropriate action to protect customers.
Updated June 27, 2017: Updated with more information on the ransomware's attack vector and affected companies.
Updated June 27, 2017: Updated again with statement from Microsoft via the Verge.

Dan Thorp-Lancaster is the former Editor-in-Chief of Windows Central. He began working with Windows Central, Android Central, and iMore as a news writer in 2014 and is obsessed with tech of all sorts. You can follow Dan on Twitter @DthorpL and Instagram @heyitsdtl.

 Windows Central Insider
Windows Central Insider









