OAuth, app permissions, and a false sense of security
Disclaimer
There is nothing new in this post. I'm just bringing this up now because a lot of people seem to not know the facts. It also has nothing to do with Windows Phone specifically, but rather pretty much every platform. The point of this post is not to spread FUD, but to remind people to not take security for granted.
OAuth
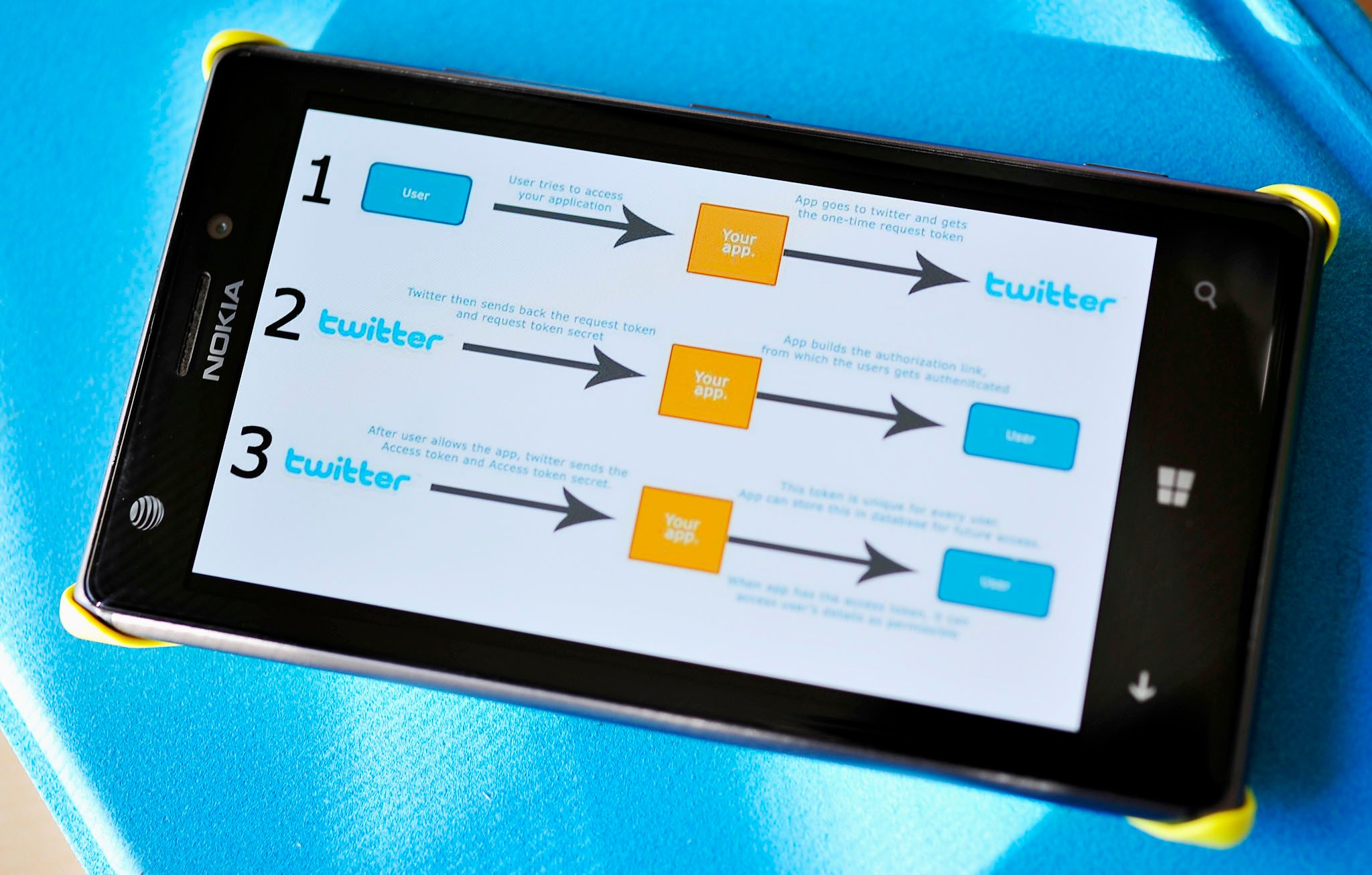
For those that don't know what OAuth is, it is an open standard for authorization. OAuth provides client applications a 'secure delegated access' to server resources on behalf of a resource owner. It specifies a process for resource owners to authorize third-party access to their server resources without sharing their credentials.
These days OAuth is used pretty much everywhere where an external client needs to login to some sort of service. You've used it with Google (I used it to upload the video in this post), Microsoft apps (Skype, Xbox Smartglass, Visual Studio), Twitter, Facebook, and countless others.


You'll know when you're using it because you'll see a button like: "Sign in with X", which will then pop up a login window on your PC or phone.
Over on /r/WindowsPhone (and the internet at large), I've read a number of comments stating that your credentials are safe when using a mobile app that uses OAuth. The theory is that the actual mobile app you're using never actually has access to your credentials because they are just opening up a window directly to the sites login, and the credentials go directly to the site (not ever to the app). The site then sends a token back to the app to say the credentials were valid, and from there the app can use that token with requests (to post a tweet for example). OAuth isn't just about keeping your password away from the app, but that is all that this post is about.
The issue is that this theory is just completely wrong. The big point of failure is that even though the app is showing the Twitter website directly - the actual browser component is still owned/contained by the app. So an app that you may or may not trust, can do pretty much what it wants to that Twitter website.
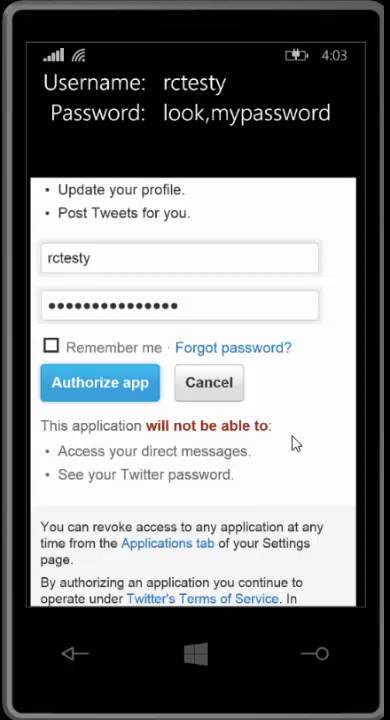
Below I made a video to demonstrate this. All I did was download a Windows Phone Twitter login sample, and add a tiny bit of code, which allows me to get the username and password that the user types (even though they are typing directly into the browser). The upper text is native XAML, the lower part is the Twitter OAuth browser component.
All the latest news, reviews, and guides for Windows and Xbox diehards.
Yes, in the time it takes to put on your fingerless hacker gloves, it is possible to make a "legit" OAuth login (i.e. it will still work and authenticate you, and is the real Twitter site) that will also steal credentials.
In a real-world application the person would obviously not show the credentials at the top of the screen, they'd silently send those off to a server which will collect all the accounts. I'm not 100% sure why someone would want to steal you account. It's not like we're sending nude selfies to each other, right?
Another issue with this browser-in-app way of doing OAuth is that the user has no idea what the actual URL of the page is. For all they know it could be going to a page that is just made to look the same as the real login page.

How do I keep safe?
This is a bit of a tricky one to give solid advice on. As far as I am aware there are only two "safe" mobile OAuth login options:
- Pin login: Some apps will open up the phones actual browser (outside of the app) and load the OAuth login. You then login, and it gives you a short code. Copy that code and paste it back in the app. This is pretty safe because the browser is not part of the possibly-dodgy app.
- Windows 8 OAuth: Windows 8 introduced an easy way for apps to use OAuth logins. When the app requests it, the OS will show a login over the app. This is a good mix between the browser-in-app method and the pin login, because it has the best of both worlds. The issue is that an app could still create a fake popup panel pretending to be the Windows 8 one.
Of course, the issue with both of the above is that they are completely dependent on the platform and app. It also depends whether the login service even supports pin-auth.
So the real advice here is to just keep aware of what you are doing, and what you are downloading. If you're downloading a Twitter app, don't even consider it if it doesn't have many ratings (meaning it hasn't had many guinea pigs). Even if it does have lots of ratings, take a few minutes to tap on the developers name and see what else they have made. Are they well known in the community? Do they have a seemingly-legitimate online presence (as oppose to someone you can't find anything about)?
You're basically trying to find out that the developer would be held accountable for wrong-doings and not just disappear into the night.
With Windows Phone specifically, most serious development efforts (and their developers) for the main services (Twitter, Facebook, Instagram, etc.) have been covered in depth by WPCentral. So if you have an urge to post grainy images of your food (and don't want to use the official app), why are you even looking in the phone marketplace? Go on WPCentral, search, and do some reading.
All this being said, I've never heard of a single wide-spread case of this happening on Windows Phone (I'm not sure if it has happened on other platforms).

App Capabilities
Credentials aren't the only thing that people have an affinity for stealing though. All the content on your little smartphone? Yeah, people want that.
There are a couple of ways that people can steal your stuff. The easiest way is for an attacker to simply ask nicely for it, and then let you enjoy a cute little game while it copies. What am I going on about? App permissions and capabilities!
You see, when you install an app on your phone from an official store/marketplace, it will prompt you for certain permissions that the app has requested. Clicking yes will then give that app access to those parts of the OS, or to that functionality in the OS.
To see a full list of permissions that an app needs on Windows Phone, scroll down to the bottom of the details section in the store and look at Requires (this applies when updating an app too, as seen in the image below).On WP8.1 it is slightly different. Open the app in the store, slide left/right twice to get to details, then scroll to the bottom.
People always freak out about apps requiring their location. While I don't want to downplay that, location should be the least of your concern. Even without access to your GPS your location can be approximated anyway. So let's look at a few others (these are Windows Phone specific, but apply everywhere):
ID_CAP_ISV_CAMERA – A lot of applications have valid reasons to use your camera, but most people assume that the app will only use the camera when you know about it. The issue is that having this capability means that any time the app is open, it can be streaming a live video of you to some dodgy dude in his basement. Let's say you download a tic-tac-toe game, and in the description it tells you that leaderboards allow you to take a custom profile photo. Along with allowing the app to do that, you're also allowing it to record you playing tic-tac-toe naked in bed.
ID_CAP_MEDIALIB_PHOTO – Some applications, like Twitter, provide an interface to select a photo from your phone and upload it. Tic-tac-toe could ask for the permission so that you can select a custom profile photo from images in your camera library. The issue comes in that, just like the camera above, the app can really do what it wants. While you're happily listening to Celine Deon while playing, it could be uploading all your personal photos.
ID_CAP_MICROPHONE – This is pretty self-explanatory. But basically, that tic-tac-toe game could also be recording your terrible singing while playing the game, and then upload it somewhere.
There are tons of others, but these were a few important ones.
For a simpler list of what each permission is, there is a guide on the Windows Phone site.

How do I keep my content safe?
Firstly, it is worth noting that almost all developers probably have their capabilities there for a valid reason. Not everyone is out to get you. I'm making a mobile racing game and am planning on using the half-click "focus" camera button as the accelerator, so will need to ask for camera permission, even though I never use the actual camera.
Sometimes developers also just put a capability there by mistake. I've done it accidentally before, and have seen lots of others do it too.There are some really silly requirements by some addons too. Amongst others, Google AdMob tells you to add ID_CAP_MEDIALIB_PHOTO to your app. I don't have a clue why they feel they need access to your photos to serve up some adverts. But I can tell you that it is safe to not put that capability in - AdMob still works fine.
If you aren't sure why tic-tac-toe needs access to your microphone, reach out to the dev and ask - BEFORE INSTALLING IT. Generally developers will be pretty easy to get hold of, and I've never had someone reply to me angrily when I ask what their capabilities were for.
Finally, on Windows Phone, apps are more limited in what they can request. This means slightly less functionality in a few apps, but also more security. I've tried to download Android games that have asked for access to my SMS's. That's when you hit the "Cancel" button fast.
Stay frosty
You are never really safe while typing your username and password anywhere. If it isn't people hi-jacking your WiFi, then it's people making dodgy apps to steal your accounts. Or if they're not trying to steal passwords, they're trying to upload your sketchy photo library. Even with an honest developer - give them a bag of money and they might consider doing something dodgy.
BUT, this isn't the movies, and naughty developers seem to be few and far between.
The greatest security measure you can take is to simply be both smart and aware of what you're doing. Stay frosty, people.
Matt "RogueCode" Cavanagh is a well known Windows Phone MVP and Nokia Developer Champion developer. You can follow him on Twitter @RogueCode or visit his developer blog.

Home to the most invested and passionate Microsoft fans, Windows Central is the next generation destination for news, reviews, advice and buying recommendations on the Windows, PC and Xbox ecosystems, following all products, apps, software, AI advancements, and accessories. We've been around for more than decade, and we take our jobs seriously. Windows Central writers and editors value accuracy and editorial independence in everything we do, never receiving compensation for coverage and never pulling punches.

 Windows Central Insider
Windows Central Insider