Valorant's Windows 11 TPM gambit: Here's what experts are saying
Windows 11 and Valorant are both fans of TPM tech. What does that mean?
TPM 2.0 has been a touchy topic since Microsoft first made it mainstream with Windows 11's system requirements. Many, many months after TPM tech entered public discourse, many people still don't understand how it affects them, their ability to upgrade to Windows 11, or helps the security of their PC.
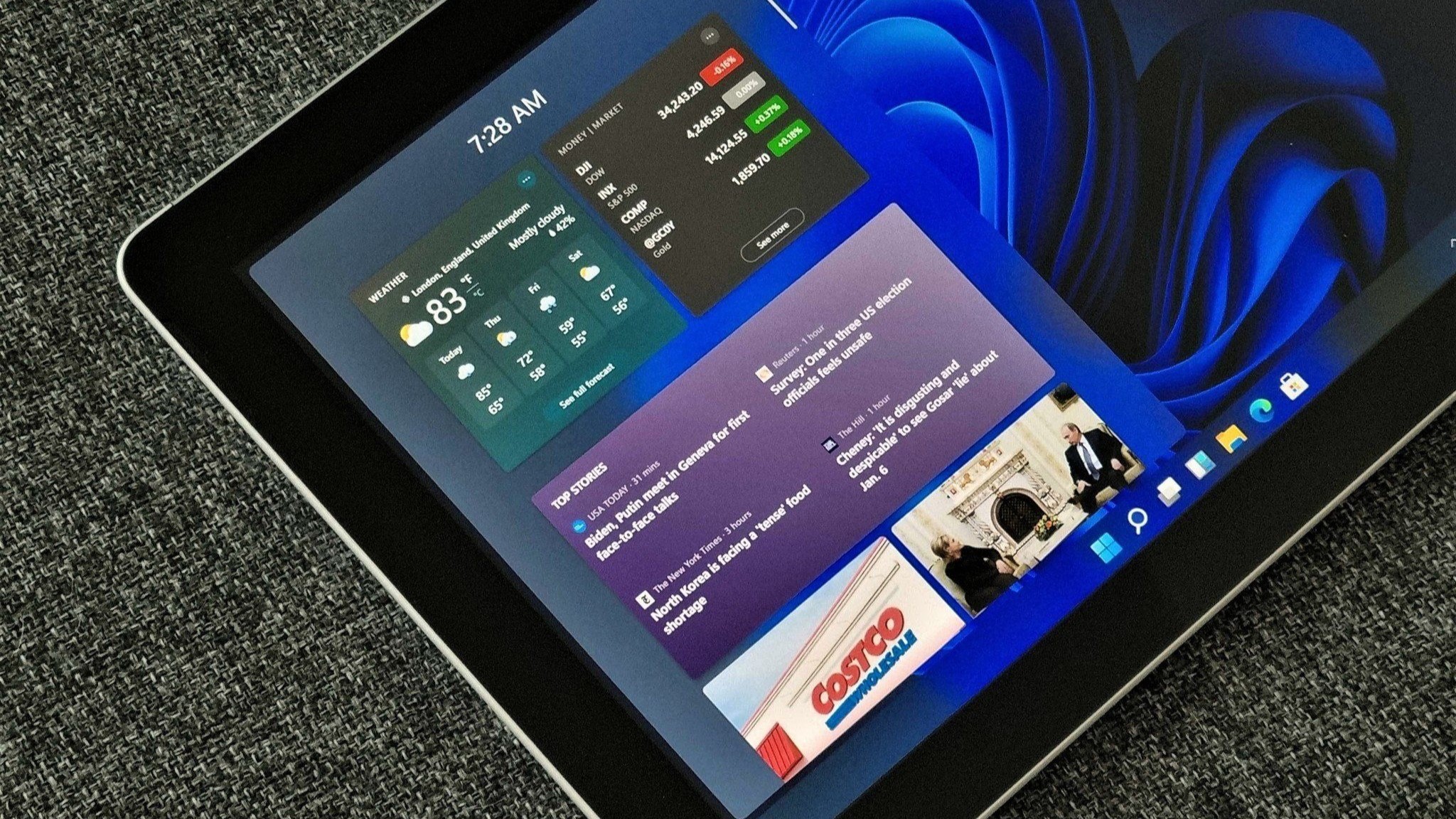
As such, it seemed like an out-of-left-field bit of news when Riot Games' Valorant started requiring TPM 2.0 and secure boot to run on Windows 11. Confusion ran rampant: Was this the beginning of a wave of games racing to catch up with Windows 11's requirements just for the sake of OS adherence, or was Riot spearheading a new breed of anti-cheat initiative?
Windows Central reached out to experts to learn a bit more about what TPM tech's role in Valorant and gaming as a whole may be going forward, as well as whether a new bar has just been set for Windows 11 gaming.


Useful measure or empty threat?
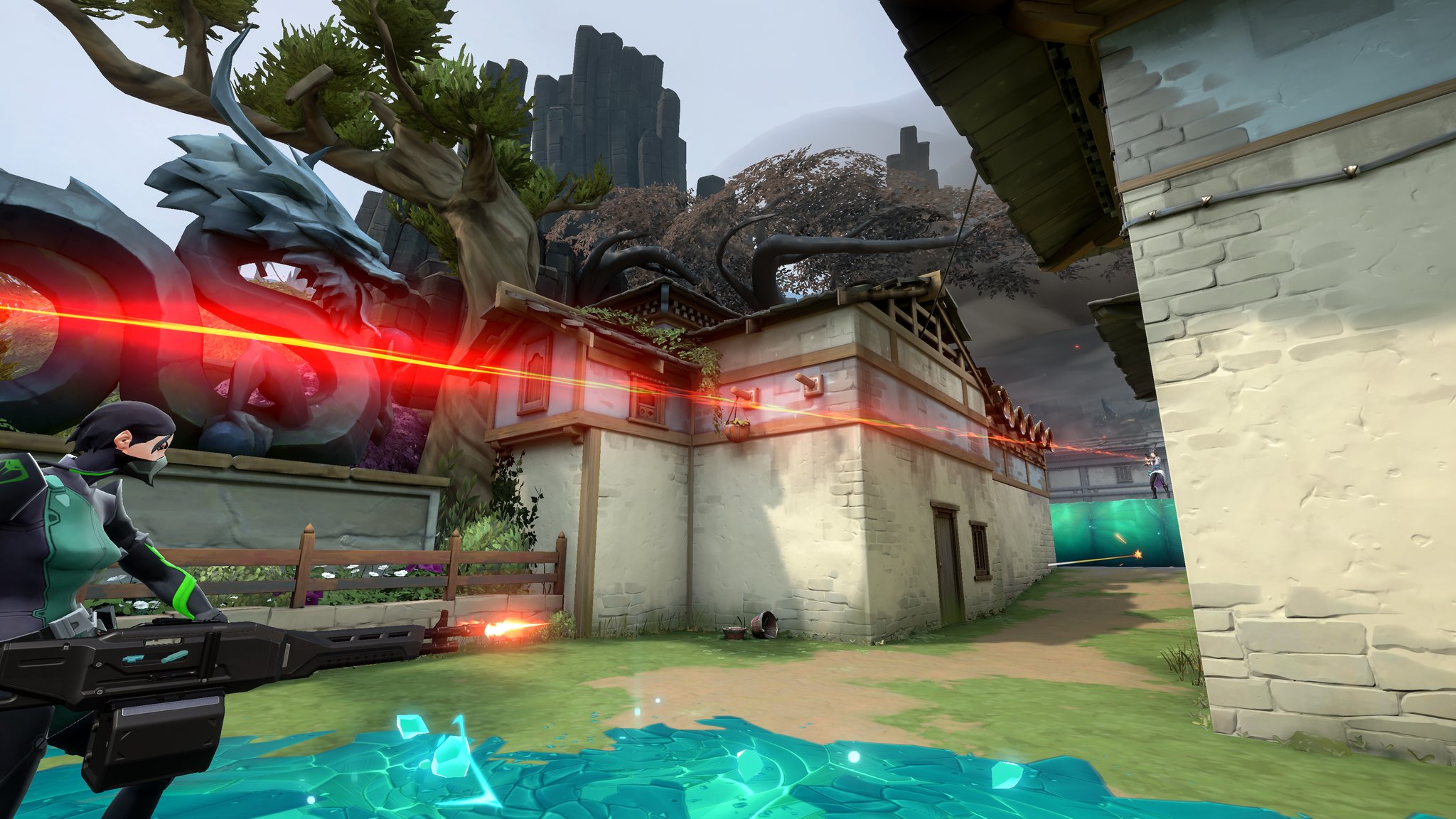
Hardware bans have existed in gaming for a long time and have often been circumvented. So Valorant's TPM 2.0 requirement seems to be, at least on the surface, a natural extension of what came before — in other words, one more piece of hardware hackers will have to spoof fresh instances of to circumvent when it comes time to get around Riot's new policy.
IDC analyst Lewis Ward weighed in on the subject, angling Riot's move as a positive for everyone but cheaters.
"I'm not a security expert, and perhaps in time hackers will find some workaround, but for now, it appears that TPM 2.0 and secure boot will be leveraged by Riot Games to permanently ban systems that have found to be using cheatware that violates the game's EULA," Ward said. "Obviously, they'll want to make sure they're getting the right systems (players) banned, but this tech is one way to raise the stakes on cheaters, and I have zero problem with that, and I don't think that most mainstream gamers do either."
However, there is a contingent of gamers, and general onlookers, who see issues with the TPM obstacle, labeling it as either ineffectual or invasive. Over on Twitter, many argued that Valorant's new TPM 2.0 and secure boot requirements will be toppled just like any other anti-cheat or hardware ID measure, making the new requirement an empty threat.
All the latest news, reviews, and guides for Windows and Xbox diehards.
Furthermore, many people stated they weren't fans of kernel-level anti-cheat measures. This brings us back to the "invasive" aspect of the new tool utilized by Riot Vanguard, the software security guard for Valorant.
Security: An unending arms race

Forrester analyst William McKeon-White shared his thoughts on the matter. He stated that Vanguard is an invasive piece of tech that's effective at what it's designed to do.
"So Valorant has been very anti-cheat oriented since its launch with Vanguard, and from my own experiences as well as those I've seen online, the move to create a comprehensive (albeit invasive) anti-cheat engine has worked well — of the things I see people complaining about in Valorant, cheaters aren't one of them," McKeon-White said. "The move to ensure TPM 2.0 adherence or safe-boot is another good pre-emptive step for ensuring cheats are nigh-on-impossible to use in Valorant."
McKeon-White acknowledged the realities voiced on Twitter, stating that cheaters will sooner or later figure out how to crack open the anti-cheat nut that is Windows 11's TPM 2.0 and secure boot combo. However, he pointed out that it's not about inventing a permanent solution; Riot's goal with Vanguard is to simply stay ahead of cheaters so by the time they crack one security measure, a new one is already in place. And to that end, McKeon-White deemed Valorant's TPM 2.0 strat as a smart move in the "cheating arms race," as he called it.
What will the competition do?

When asked whether it seems likely that other publishers and developers will take a similar approach to the one Riot has with regards to TPM requirements and security in general, McKeon-White wasn't sold on the idea that such copy-catting is a guarantee.
"With all of that said, and with all of Vanguard's success, I'm actually unsure if other developers/publishers will take a similar approach — what Vanguard ultimately does, having access to the core system, may be seen as too invasive or too risky by other devs/publishers," he said.
"Application-level security or behavioral-based enforcement may be more appealing, as it doesn't open up potential concerns around 'what if our system is compromised?' Additionally, surveillance via video games is a growing area of controversy, from all the data that games are collecting on players, and avoidance of system-level monitoring with high authorization may be seen as a way to ensure player privacy."
McKeon-White may very well be on the money with these theories. When reached for comment on the topic, Blizzard Entertainment did not clarify its stance in time for publication regarding whether similar security changes were headed Overwatch's way. Meanwhile, Ubisoft declined to comment on the TPM subject and its potential relation to Rainbow Six Siege security measures.
Riot Games itself did not respond to a request for comment.
Not over yet

As McKeon-White said, there's a chance these sorts of invasive security measures will ultimately cause more headaches for their creators than they're worth as controversies around such topics mount. However, there's also the reality that Riot Games continues with its hardcore approach to security on the simple basis that it works, for the most part.
Which of these opposing strains of anti-cheat ideology will become dominant going forward remains unclear; the only thing that's certain is that Valorant has brought attention to one of the newest safeguards cheaters will have to overcome. The key takeaway for security-minded gamers who don't want to fall into the swamp of invasive anti-cheat measures is this: If you don't want to risk getting banned due to TPM 2.0 and secure boot, stick with the Windows 10 version of Valorant for now. And if you don't want to deal with Vanguard's prying as a whole, stay away from competitive titles put out by Riot Games and opt for one of the many other best multiplayer PC games.

Robert Carnevale was formerly a News Editor for Windows Central. He's a big fan of Kinect (it lives on in his heart), Sonic the Hedgehog, and the legendary intersection of those two titans, Sonic Free Riders. He is the author of Cold War 2395.

 Windows Central Insider
Windows Central Insider