Microsoft's righteous attack on passwords to march ahead in 2021
Microsoft is working with partners to create a future without passwords.
What you need to know
- Microsoft is working towards a future without passwords, as highlighted by a new blog post.
- Passwords can create security risks and be difficult to remember.
- Microsoft supports a wide range of passwordless technology.
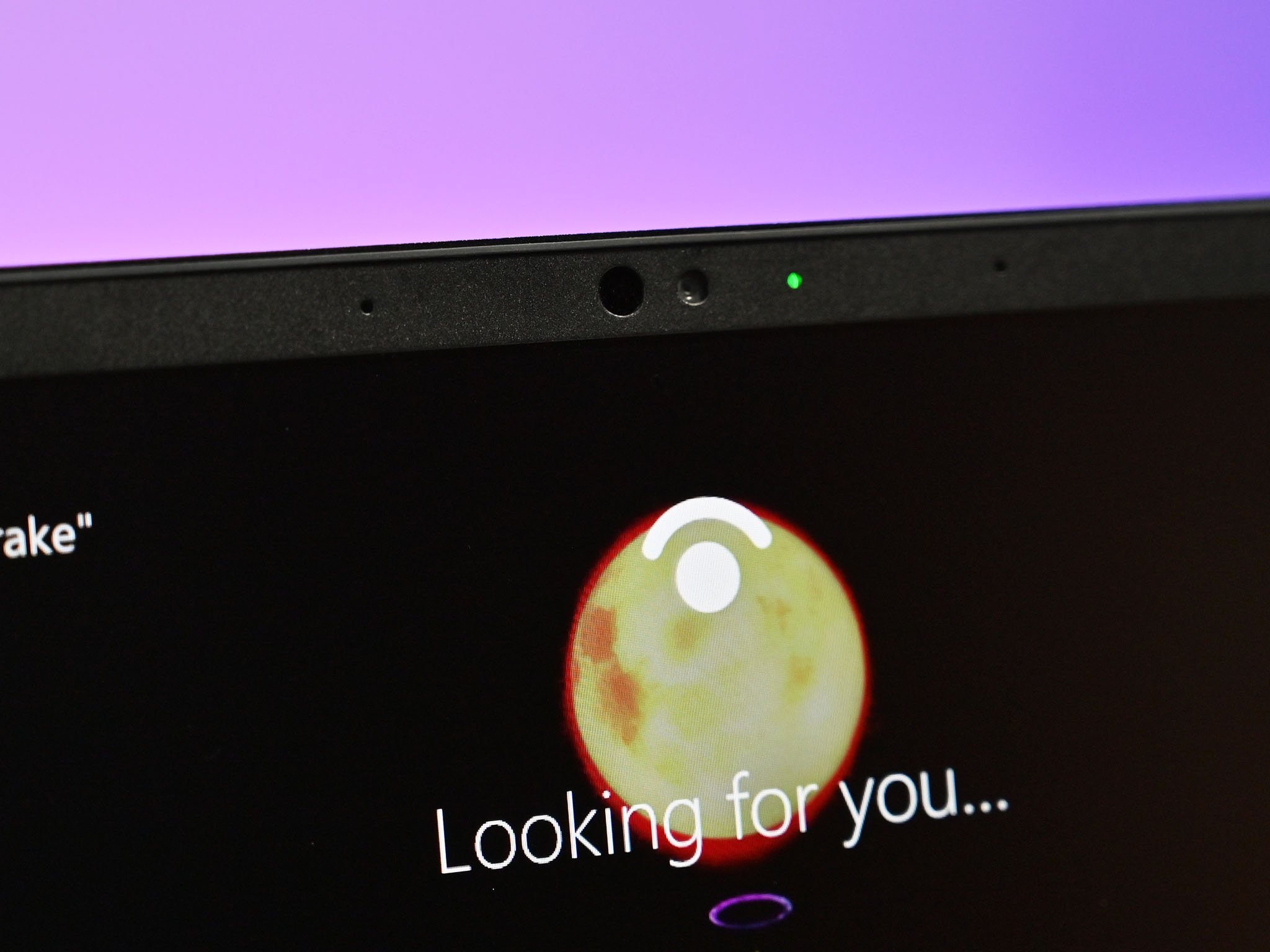
Microsoft has worked for years to move towards a future without passwords, or at least with significantly fewer of them. Windows Hello allows people to sign into their devices without a password and Microsoft works with several partners to allow people to use devices without passwords. A new blog post from Microsoft highlights some of the major steps forward in 2020 for passwordless technology and the future of the tech in 2021.
As highlighted by Microsoft in its blog post, passwords create security risks and can be a hassle to use. Microsoft highlights some key indicators that show that passwordless tech is on the rise:
- Passwordless usage in Azure Active Directory is up by more than 50 percent for Windows Hello for Business, passwordless phone sign-in with Microsoft Authenticator, and FIDO2 security keys.
- More than 150 million total passwordless users across Azure Active Directory and Microsoft consumer accounts.
- The number of consumers using Windows Hello to sign in to Windows 10 devices instead of a password grew to 84.7 percent from 69.4 percent in 2019.
According to the World Economic Forum, an estimated 80 percent of cybercrime attacks are directed at passwords. To help people move away from passwords, Microsoft works with companies like YubiKey, HID Global, Trustkey, and AuthenTrend. In February, Microsoft also rolled out preview support of Azure Active Directory for FIDO2 security keys.


In 2021, Microsoft plans to release a converged registration portal, which allows people to manage passwordless credentials through the My Apps Portal.
If you want to add biometric security to your PC and move away from passwords, you can grab a webcam with Windows Hello or a fingerprint reader with Windows Hello.
All the latest news, reviews, and guides for Windows and Xbox diehards.

Sean Endicott is a news writer and apps editor for Windows Central with 11+ years of experience. A Nottingham Trent journalism graduate, Sean has covered the industry’s arc from the Lumia era to the launch of Windows 11 and generative AI. Having started at Thrifter, he uses his expertise in price tracking to help readers find genuine hardware value.
Beyond tech news, Sean is a UK sports media pioneer. In 2017, he became one of the first to stream via smartphone and is an expert in AP Capture systems. A tech-forward coach, he was named 2024 BAFA Youth Coach of the Year. He is focused on using technology—from AI to Clipchamp—to gain a practical edge.

 Windows Central Insider
Windows Central Insider









