Windows Phone dodges Black Hat 2012 certificate vulnerability bullet - other smartphones not so lucky...

A recent paper presented at Black hat 2012 by Peter Hannay has demonstrated a vulnerability in how iOS and Android deal with certificates whilst operating with an Exchange Server. The good news in this report is that Peter was unable to trick Windows Phone 7.5 devices using the same methods.
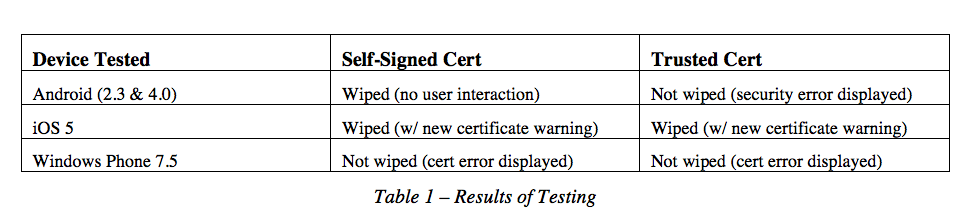
Using a man in the middle attack combined with a generic fake certificate, they were able to gain some traction in sending a command to iOS and Android devices to commence a device wipe. When devices are connected via Active Sync they commit to accepting certain responsibilities, one of the most important and sensitive of which is the wipe command. They tested off two sets of Exchange 2010 servers. One running with a self-signed certificate, a very common configuration for small business and another using a certificate from a trusted certificate signing authority.
Android devices accepted the fake certificate and wiped with no user interaction or warning on the Exchange server that was operating using a self-signed certificate. The Android device would not wipe whilst connected to the trusted certificate-holding server.


On both the self-signed and trusted certificate servers, iOS rolled over and wiped the device in both instances, only displaying a new certificate warning white flag whilst doing so. In both cases, a normal user would likely accept the certificate warning. You know, users do that kind of thing to get on with their lives.
Windows Phone on the other hand would not accept the new certificate in either case and would need to have one manually installed for such an attack to be possible. Hopefully these papers will lead to a strengthening of security on Android and iOS devices. In the meantime, we hope that more companies would wake up to the benefits of Windows Phones. Whilst we certainly do not wish to see any ill come of this, we can at least gloat about our platform being a little more savvy when it comes to accepting gifts from strangers over Wi-Fi pineapples?
Want to read more about Wi-Fi Pineapples? Need a place to vent some steam at the injustice of certificate signing authorities? The comments are open for business; we look forward to your contribution!
Source: Blackhat 2012; via WP Sauce
All the latest news, reviews, and guides for Windows and Xbox diehards.

Robert is a Former Contributor for Windows Central, covering hardware, software, and Windows Phone.

 Windows Central Insider
Windows Central Insider