Get secure by encrypting your PC with Microsoft BitLocker for Windows 8 Pro

While the release of Windows Vista was plagued with burden and its legacy was remembered as such, one excellent feature to rise out of the wreckage has served its way through Windows 7 up to current day Windows 8 operating systems. The feature that we are referring to is, of course, Microsoft’s BitLocker Drive Encryption – full disk encryption at the click of a button.
WARNING: Disk Encryption is a delicate process, please be sure to backup your data before beginning. WPCentral, Mobile Nations, Smartphone Experts are not responsible for any data loss caused by a failure to read instructions carefully or ignoring our recommendation to backup ALL of your data before beginning. Please be sure to read the entire article before beginning your encryption journey. If you have doubts about anything, please ask in the comments below before proceeding.
BitLocker Drive Encryption
The encryption software was originally only included within Ultimate and Enterprise editions of previous operating systems can now be found in the more affordable Windows 8 Pro variation. The system itself has the ability to full encrypt a disk with an AES algorithm.


The Advanced Encryption Standard (AES for short) was published by the United States National Institute of Standards and Technology in 2001. As of a 2013 cryptanalysis of the cipher, it was found that there are possibilities other than using a brute force attack to break into an AES encrypted system, but none of them are currently possible with present day computer systems.
The Pros and Cons
If you are looking to encrypt your Windows 8 Pro PC, you should probably consider a few notions before proceeding. To start, you should be aware that in the event of disk or operating system corruption, you are more likely to lose your data if the drive is encrypted. While a normally corrupted PC can be booted up into a Linux variant and the data recovered with software – encryption makes this task ever more difficult and sometimes impossible (despite having a recovery key, as we will discuss).

BackTrack is one of many Linux distros that can be used to break into a Windows file system
Another factor that makes encrypting your disk a bit less invaluable is cloud storage; the files that you are trying so much to protect on your PC are hovering in space, in an unencrypted system. Sure, many online data services vary and the one you use might be using encryption, but for the most part – they are not. If you are using Microsoft’s OneDrive service to keep your files updated and backed up, then you are storing your files in an unencrypted cloud. An excellent wiki article on OneDrive and data encryption (or the lack of it) can be found on Microsoft’s support site by clicking here.
All the latest news, reviews, and guides for Windows and Xbox diehards.
Let us be realistic though, unless you are trying to protect your data from the government (which might be a reality these days), then you probably will not have to worry about someone hacking into Microsoft’s servers to steal your tax information. So let us leave that notion aside and note that you most likely simply want to protect your data from being accessed if your laptop or tablet is stolen.
Disk encryption is an excellent solution for preventing thieves from booting up your system with a side-loaded operating system to access your files. Encryption can provide a reliable and strong shield against the hacker looking to sniff your personal data.
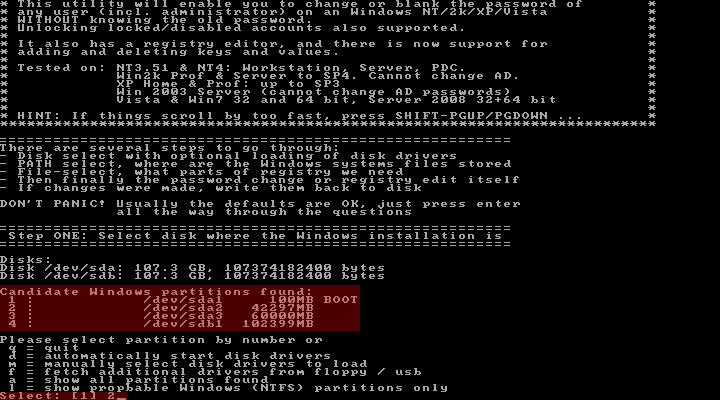
Here, an offline registry editor is used to remove a user's password from their Windows account
If you have decided that you wish to give BitLocker encryption a go, then we are ready to proceed. We, of course, recommend that you first backup all of your data in the event disk corruption occurring during the procedure (in fact, you should be backing up your data anyway).
If your data is backed up and you are ready to begin, then simply follow the steps below to a happier and more encrypted system.
How to Encrypt Systems with TPM Chips
Microsoft’s BitLocker system was designed for use in conjunction with machines that have Trusted Platform Module chips installed within them. To simplify what the TPM chip does, it holds the keys needed to boot up and unlock the operating system.

If your PC now has a giant lock on it, then it only makes sense that a key will be needed to unlock it. A TPM chip holds an encryption system’s keys, so the system can be easily booted. If the drive is removed from the system (and thus separated from the TPM chip), it cannot be booted. In addition, if the system is booted with a side-loaded operating system, the TPM chip will not give the keys up for use.
Many business machines have TPM chips including Lenovo’s ThinkPad series, Dell’s Latitude series, Microsoft’s Surface Pro, and HP’s EliteBook series. If you do have a business machine with a TPM chip, then you can follow the instructions below; otherwise, skip to the next section to see how to encrypt a system without a TPM chip. If you are unsure whether or not your system has a TPM chip, then follow the steps below and see if you are addressed with an error.
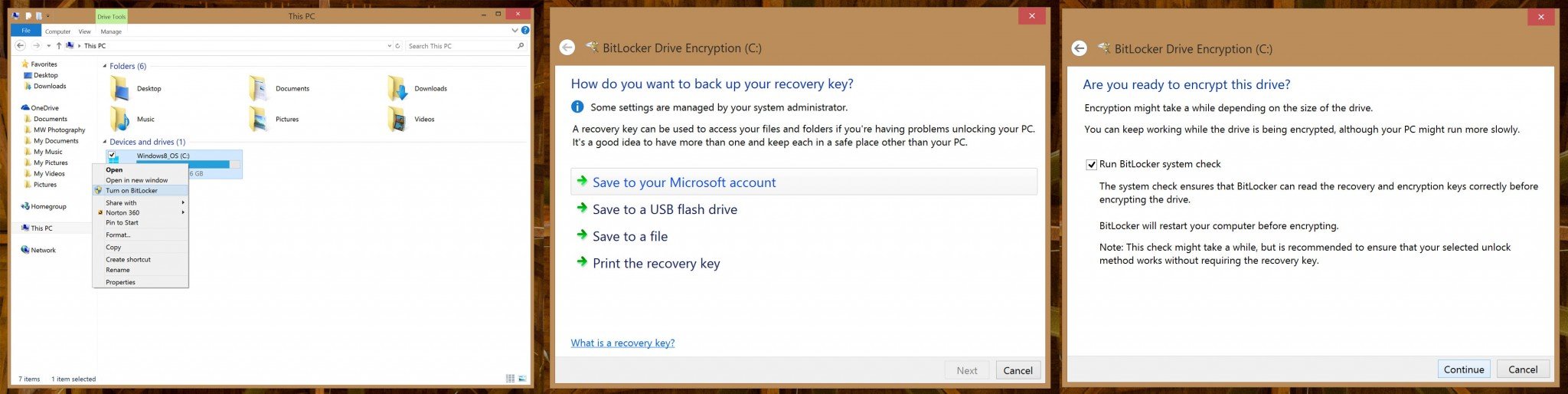
Click on the above image to enlarge it.
- To begin, please make sure that you are logged in as an administrator on your local machine.
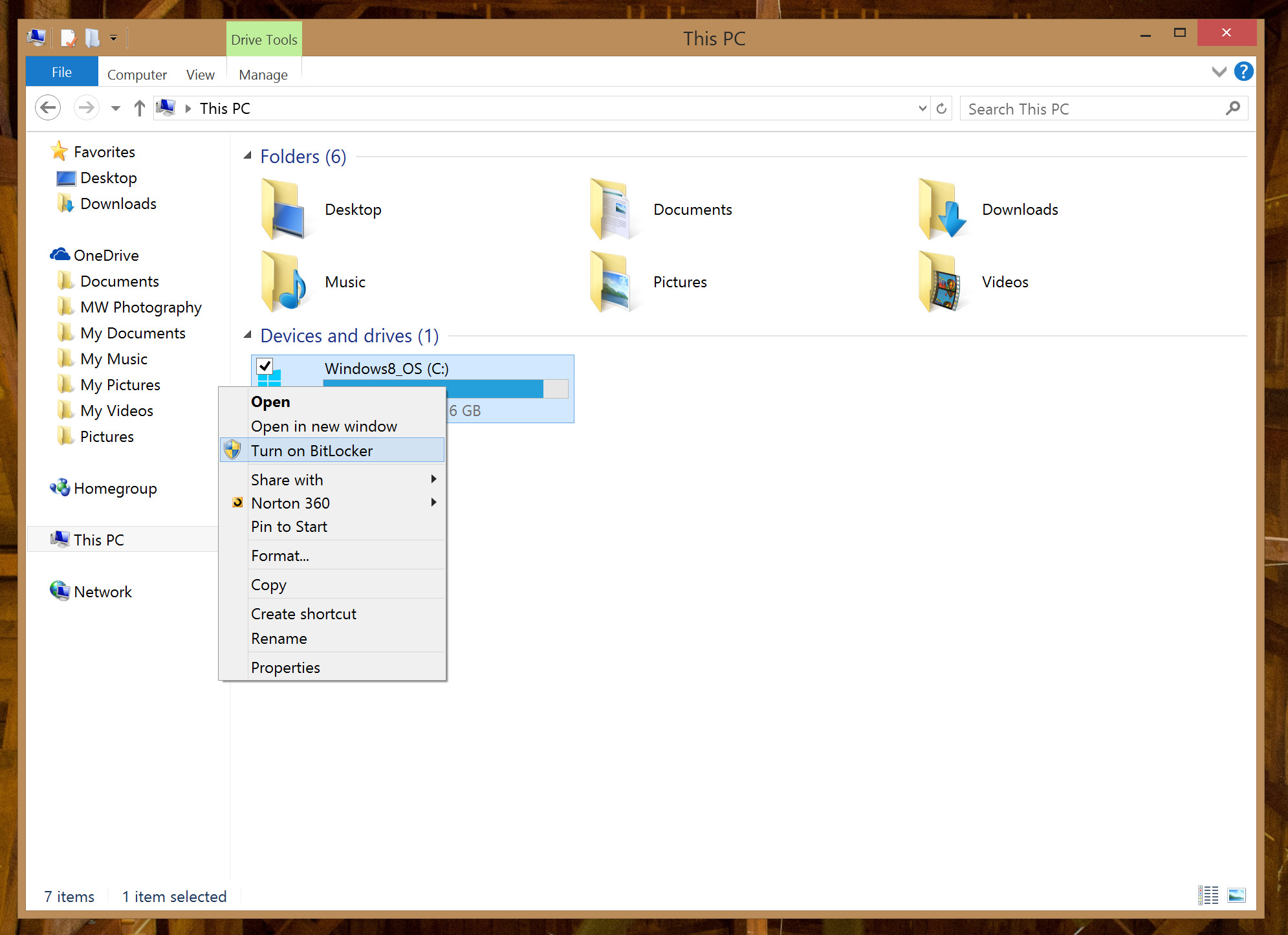
- Next, open “This PC” (recently known as “My PC” in previous versions of Windows.
- With the “This PC” Explorer window open, you should be able to see a complete list of your devices and drives. Right click the drive you wish to encrypt (usually the ‘C’ drive).
- Now select the “Turn on BitLocker Option”. If you have a system with a TPM chip, it may now prompt you to active the chip via a simple “TPM Security Hardware” wizard. If you do not have a TPM chip, you will now be presented with an error message stating that – if so, skip to the next section of this article.
- After you have initialized your TPM chip (which may require a reboot), you can go ahead and begin to active BitLocker. During the process you will be given a recovery password to use in emergencies; you can choose to “save to your Microsoft account”, “save the password on a USB drive”, “save the password in a folder”, or “print the password”. We suggest choosing the Microsoft account option, so you will never be at risk of losing your recovery key. One your key has been saved, click “Next” to continue.
- The next screen will ask if you wish “Encrypt used disk space only” or if you wish to “Encrypt entire drive” – we suggest going with the latter.
- Once you have selected your recovery method and disk encryption amount you will be given one last chance to turn back. Ensure that the right drive is select, check the “Run BitLocker System Check” box and click continue to proceed. Note: Your PC may reboot during this process.
- That is it! You should now see an “Encryption in Progress” status bar showing the competition status of the disk you are encryption. While the disk is encrypting itself, you will see a Drive Encryption icon in your taskbar – if any problems arise, you will be notified.
- Once the encryption has completely finished, you can use your computer as normal – the system is now safe!
How to Encrypt Systems without TPM Chips
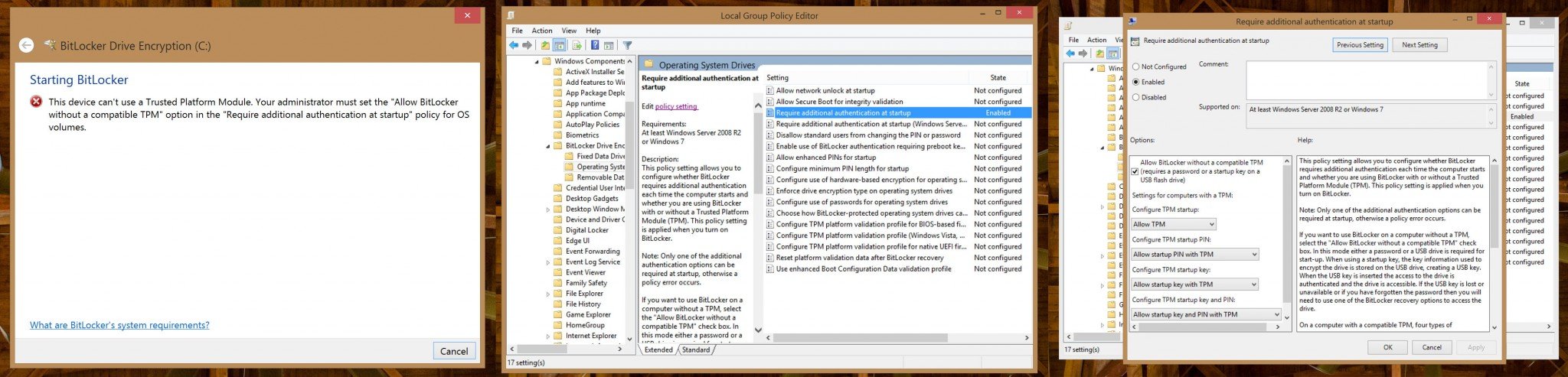
Unfortunately, not all PCs manufactured include built in TPM chips. If you are running a consumer notebook or Microsoft’s Surface 2 – then you will find an error message notifying you of the scenario; the error message may appear as follows:
“This device can’t use a Trusted Platform Module. Your system administrator must set the “Allow BitLocker without a compatible TPM” option in the “Require additional authentication at startup” policy for OS volumes”
For many people who are their own system administrators, this message can seem a bit daunting, but do not worry – if you really wish to encrypt your system with Microsoft’s BitLocker solution, we will help you out!
Click on the above image to enlarge it.
We will begin by changing a setting within the Group Policy Object Editor that will allow you to encrypt the system despite not having the (quite wonderful) TPM chip.
- To begin, go to your Start Screen and type in “gpedit.msc”, and hit enter. Alternatively, you can press “WINDOWS KEY + R” to bring up a Run dialog and type in the command from there.
- After typing the command, you will see the Local Group Policy Editor pop up in front of you. The editor is split into two parts, on the left hand side you will see a list of folders (much like you would see in Windows explorer) and on the right side, you will see a Window that will display options available within the folder we have selected. NOTE: Please be sure to follow all instructions as making the wrong change can seriously affect your system. If you are unsure of something, please ask in the comments below.
- On the right hand side of the editor, start by selecting the “Administrative Templates” option under “Computer Configuration”.
- On the right hand side of the editor, you should now see a selection of folders – double click “Windows Components”, then double click “BitLocker Drive Encryption”, and finally double click “Operating System Drives”.
- You will now see a list of items that appear to be files – these files are in fact settings that can be altered by a system administrator. Double click the item entitled “Require additional authentication at startup”. Note: There are two of these settings – do NOT click the one that includes “(Windows Server 2008 and Windows Vista)”.
- A dialog box will now popup entitled, “Require additional authentication at startup”. Begin by selecting the bubble entitled “Enabled” (by default, “Not Configured” will be selected).
- The options that were once grayed below should become available. Check the box that says “Allow BitLocker without a compatible TPM (requires a password or a startup key on a USB flash drive)”. Leave all other options as they are and hit “Apply” followed by “OK”. You can now close the policy editor window.

Okay, now that you have enabled Microsoft's BitLocker within Windows 8 Pro, it is time to start encrypting that system! Follow the steps below to continue and encrypt the system.
- Open “This PC” (recently known as “My PC” in previous versions of Windows).
- With the “This PC” Explorer window open, you should be able to see a complete list of your devices and drives. Right click the drive you wish to encrypt (usually the ‘C’ drive).
- Now select the “Turn on BitLocker Option”. If you were previously met with an error before – that error should be gone now.
- You will be prompted how you wish to unlock your drive upon booting it up. As the machine cannot store its key on a secure TPM chip, you will have to select another way to store it. Either you can use a USB flash drive by selecting “Insert a USB flash drive” or you can enter a password at boot by selecting “Enter a password”. In this example, we are going to select “Enter a password”. Note: If you choose the option to require a USB flash drive, you must have it on you at all times when you wish to boot the PC.
- The system will now prompt you to enter a password to unlock the drive. Use a password that contains uppercase and lowercase letters, numbers, symbols, and spaces for the highest level of security. While you do not have to adhere to the suggestion, we suggest creating the strongest password you can come up with for BitLocker. Note: Be sure to remember your password – if you do not, then you will be unable to boot the system.
- After you have entered your super secure password you will be given a recovery password to use in emergencies; you can choose to “save to your Microsoft account”, “save the password on a USB drive”, “save the password in a folder”, or “print the password”. We suggest choosing the Microsoft account option, so you will never be at risk of losing your recovery key. One your key has been saved, click “Next” to continue.
- The next screen will ask if you wish “Encrypt used disk space only” or if you wish to “Encrypt entire drive” – we suggest going with the latter.
- Once you have selected your recovery method and disk encryption amount you will be given one last chance to turn back. Ensure that the right drive is select, check the “Run BitLocker System Check” box and click continue to proceed. Note: Your PC may reboot during this process.
- That is it! You should now see an “Encryption in Progress” status bar showing the competition status of the disk you are encryption. While the disk is encrypting itself, you will see a Drive Encryption icon in your taskbar – if any problems arise, you will be notified.
- Once the encryption has completely finished, you can use your computer as normal – the system is now safe! Simply enter your password at startup (or plug in your flash drive) to boot the system.
Some Questions You May Have

- How do I disable BitLocker? Simple, right click on the encrypted drive in the “This PC” explorer window and select “Turn off BitLocker Drive Encryption”, then select “Disable BitLocker Drive Encryption” from the dialog box that appears.
- I forgot my password, how can I access my machine? Boot up your encrypted machine and the “BitLocker Drive encryption Recovery Console” will appear. From here, use the method that you selected above to access your recovery key and access the system.
- If I am using an external backup drive, should I continue using it? If you backup your data to the unencrypted drive, then you might as well never have encrypted your drive. We suggest either keeping the backup drive in a safe unless it is needed or using BitLocker to encrypt your external drive.
- How do I change the encryption type of BitLocker? Use the Group Policy Editor as before, but this time select the “Choose drive encryption method and cipher strength”. From there you can select exact type of encryption you wish to use.
- What about TrueCrypt? The encryption solution, TrueCrypt, is a great alternative to Microsoft’s Bitlocker, and you can check it out by visiting their site here. We choose to use BitLocker as our encryption method for two reasons: It is the official solution provided by Microsoft and it is easily integrated into the Windows operating system.
- I have addition questions, what can I do? You can start by performing a Bing search to see if your question has already been been answered. Alternatively, you can comment below, ask in our Windows 8 forum, or send me a personal question via Twitter (@Marcham93).
We hope you enjoyed this article on encrypting your personal data. Securing your drive and information is the first step towards a more secure future. Remember though, if you take your files outside of the system by placing them on an unencrypted backup, unsecured cloud service, or unencrypted USB flash drive – you are not safe.

DISCLAIMER: Like all security systems - if there is a will, there is a way to break in. While BitLocker is an extremely secure method of protecting your data, there are possible exploits (as with all systems) that might allow an experienced hacker to access the system; you can read more about those exploits by clicking here.
Do you encrypt your personal drive – do you use Microsoft’s BitLocker solution?

Michael is a Former Contributor for Windows Central, covering Microsoft hardware and software, including Xbox.

 Windows Central Insider
Windows Central Insider