Intel's Project Circuit Breaker uses 'elite hackers' to find bugs
Intel's working with expert hackers to find bugs in its firmware, GPUs, chipsets, and more.
What you need to know
- Intel announced an expansion to its bug bounty program called Project Circuit Breaker.
- A team of elite hackers will work together to find bugs in Intel's firmware, GPUs, chipsets, hypervisors, and more.
- The first Project Circuit Breaker event, called Camping with Tigers, began in December 2021.
Intel's Project Circuit Breaker expands the company's bug bounty project to help find issues with firmware, GPUs, chipsets, hypervisors, and other components. Project Circuit Break consists of a group of 'elite hackers' working with Intel by hosting targeted time0boxed events that focus on specific technologies and platforms. Intel also provides training for hackers and facilitates collaboration between Intel engineers and bug-hunting experts.
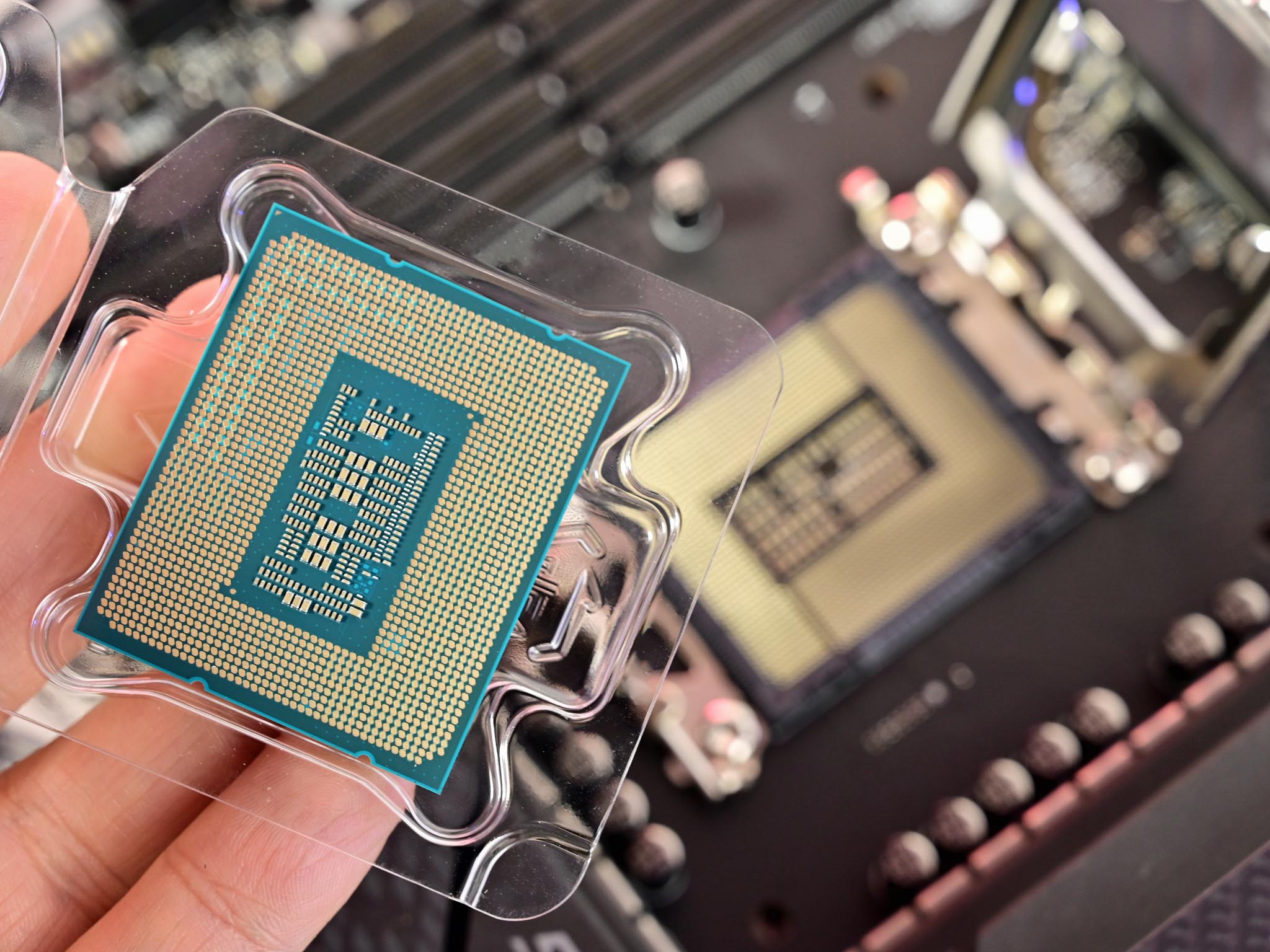
The first Project Circuit Breaker is called Camping with Tigers. It launched in December 2021 and runs through May of this year. 20 researchers received systems with Intel Core i7 processors for testing at the Camping with Tigers event.
"This program is part of our effort to meet security researchers where they are and create more meaningful engagement," said Katie Noble, director of Intel Product Security Incident Response Team and Bug Bounty. "We invest in and host bug bounty programs because they attract new perspectives on how to challenge emerging security threats – and Project Circuit Breaker is the next step in collaborating with researchers to strengthen the industry's security assurance practices, especially when it comes to hardware. We look forward to seeing how the program will evolve and to introducing new voices to the meaningful work that we do."


Project Circuit Breaker builds on Intel's preexisting bug bounty program. The company notes that 97 of 113 externally found vulnerabilities from 2021 were reported through Intel's bug bounty program. Intel initially made its bug bounty program public in 2018.
All the latest news, reviews, and guides for Windows and Xbox diehards.

Sean Endicott is a news writer and apps editor for Windows Central with 11+ years of experience. A Nottingham Trent journalism graduate, Sean has covered the industry’s arc from the Lumia era to the launch of Windows 11 and generative AI. Having started at Thrifter, he uses his expertise in price tracking to help readers find genuine hardware value.
Beyond tech news, Sean is a UK sports media pioneer. In 2017, he became one of the first to stream via smartphone and is an expert in AP Capture systems. A tech-forward coach, he was named 2024 BAFA Youth Coach of the Year. He is focused on using technology—from AI to Clipchamp—to gain a practical edge.

 Windows Central Insider
Windows Central Insider









