Researchers fool Windows Hello face recognition on older versions of Windows 10
There are many reasons to keep your PC up to date, but a flaw recently discovered by researchers in Windows Hello's face recognition on older versions of Windows 10 may be chief among them.

The flaw, discovered by researchers at Syss (via The Register) allows Windows Hello to be spoofed on Windows 10 releases older than the Creators Update (build 1703). However, even if your PC is currently running the Creators Update or Falls Creators Update, facial recognition needs to be set up again to circumvent the flaw.
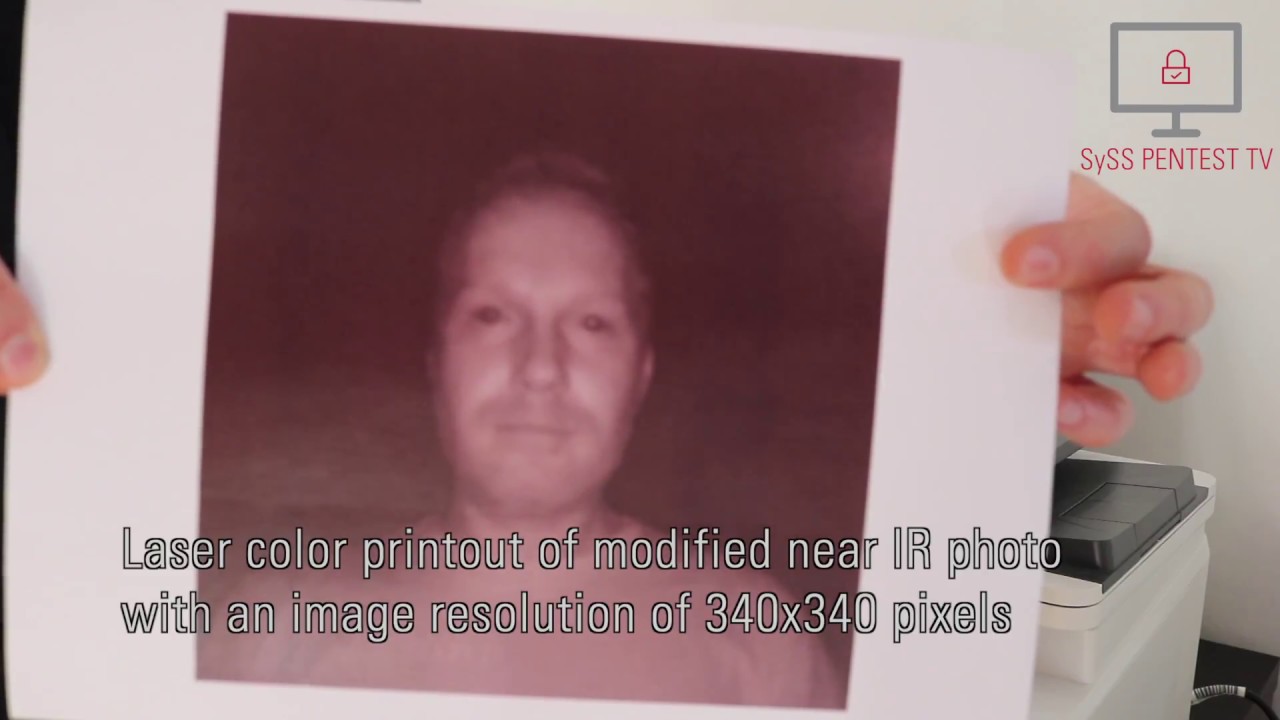
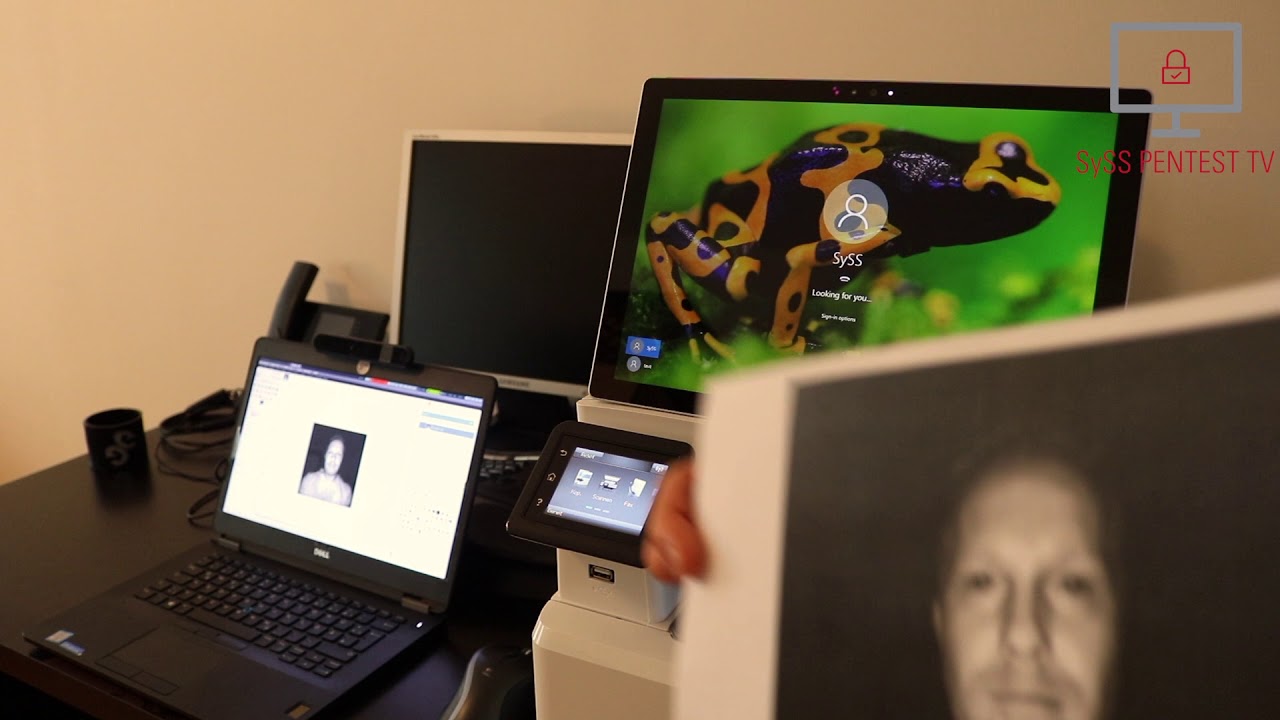
Matthias Deeg and Philipp Buchegger, the researchers who discovered the attack, say that Windows Hello can be fooled by using printed photos of an authorized user that has been modified. Using a frontal photo taken with a near-infrared camera, facial recognition on the affected Windows 10 versions could be fooled. Deeg and Buchegger tested the spoofing attack with Windows Hello's standard setup, as well as with "enhanced anti-spoofing" enabled, and were able to bypass both. From the report:
Both, the default Windows Hello configuration and Windows Hello with the enabled "enhanced anti-spoofing" feature on different Windows 10 versions are vulnerable to the described spoofing attack and can be bypassed. If "enhanced anti-spoofing" is enabled, depending on the targeted Windows 10 version, a slightly different modified photo with other attributes has to be used, but the additional effort for an attacker is negligible. In general, the simple spoofing attack is less reliable when the "enhanced anti-spoofing" feature is enabled.
While worrying, the attack requires a pretty specific set of steps to work. The best way to stay protected is to make sure you're PC is current with either the Creators Update or Fall Creators Update. Once updated, you'll want to set up Windows Hello's face recognition from scratch to guard against spoofing.


You can view demonstrations of the exploit in action in the videos below.
Thanks, Daniel, for the tip!
All the latest news, reviews, and guides for Windows and Xbox diehards.

Dan Thorp-Lancaster is the former Editor-in-Chief of Windows Central. He began working with Windows Central, Android Central, and iMore as a news writer in 2014 and is obsessed with tech of all sorts. You can follow Dan on Twitter @DthorpL and Instagram @heyitsdtl.

 Windows Central Insider
Windows Central Insider