How to block desktop app access on Windows 10
Yes, you can restrict access to most apps on Windows 10, and in this guide, you will learn how.
On Windows 10, removing access to specific apps can come in handy in many scenarios, such as when you must prevent users from launching built-in tools (such as PowerShell and Command Prompt) to run scripts or make unwanted system changes. Maybe you need to set up an app that should only be accessible by you and no one else, or you installed the Microsoft 365 version of Office and since you can't customize the installation, you need to restrict access to some of the apps to comply with your organization's policies.
Regardless of the reason, if you have to restrict access to specific applications, Windows 10 includes at least two ways to disable them using Group Policy Editor or Security Policy console.
This guide will walk you through the steps to disable access to one or more desktop applications on Windows 10.


How to disable apps access from Group Policy
To disable access to certain apps on Windows 10 from Group Policy, use these steps:
- Open Start.
- Search for gpedit and click the top result to open the Local Group Policy Editor.
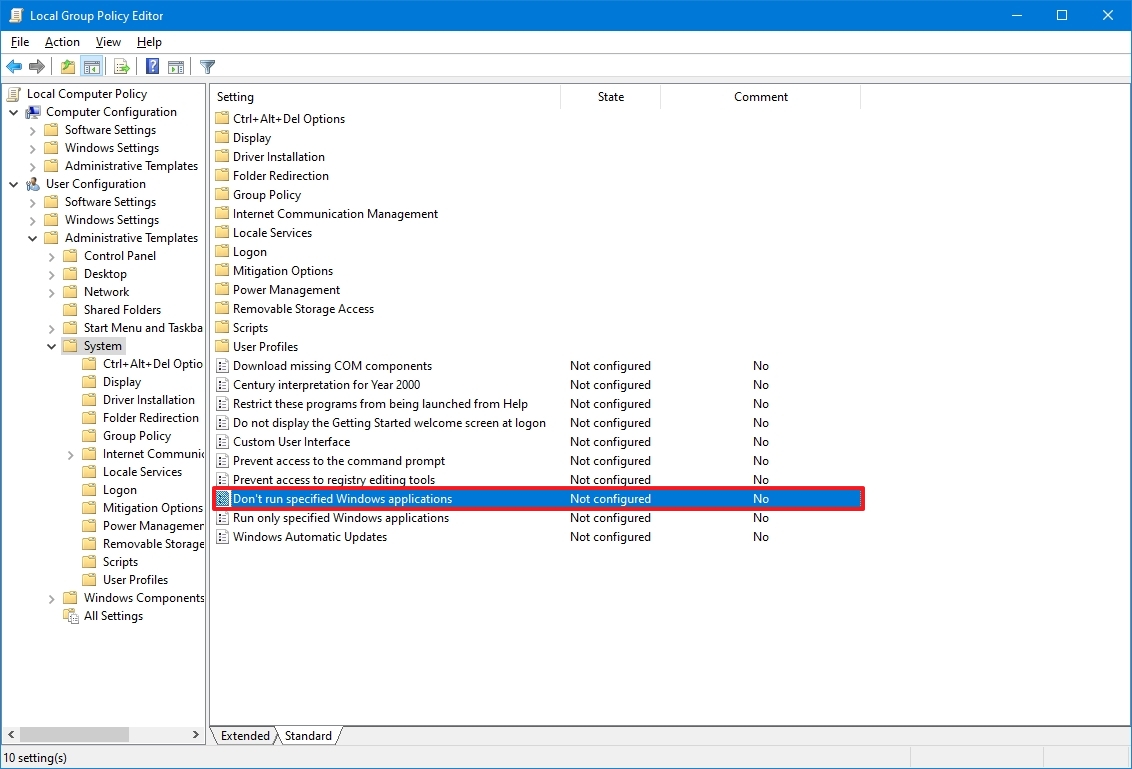
- Browse the following path: User Configuration > Administrative Templates > System
- On the right side, double-click the "Don't run specified Windows applications" policy.
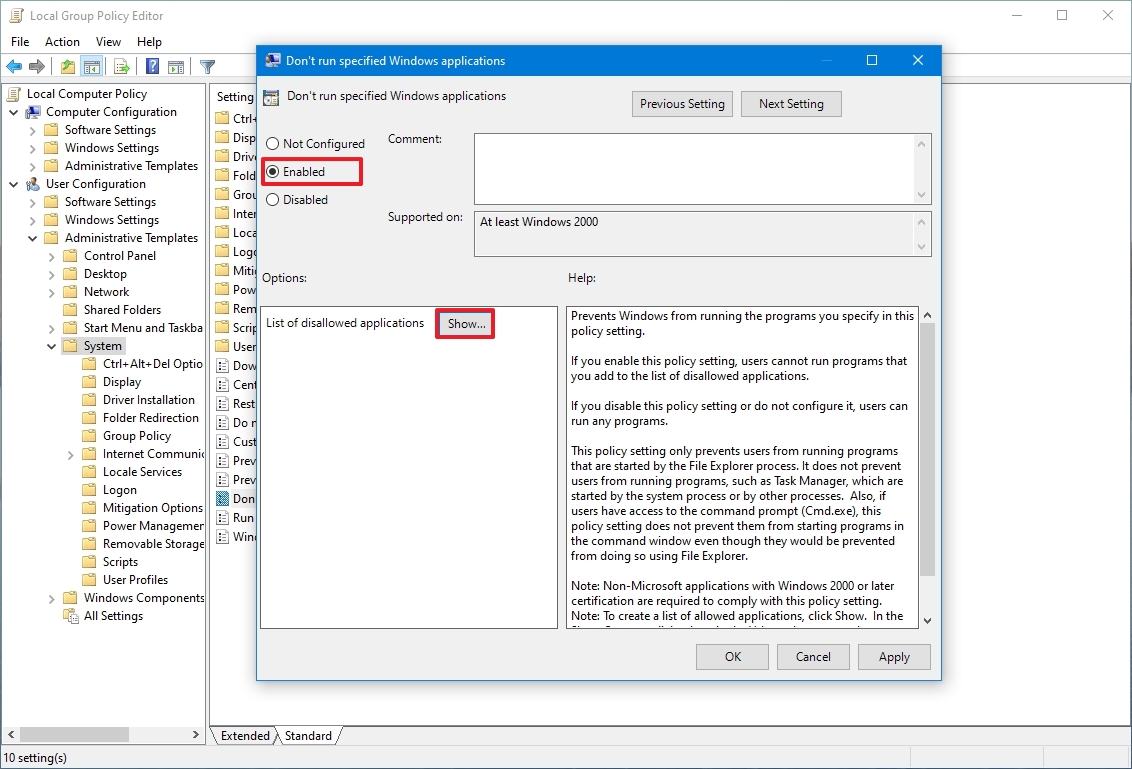
- Select the Enabled option.
- Click the Show button.
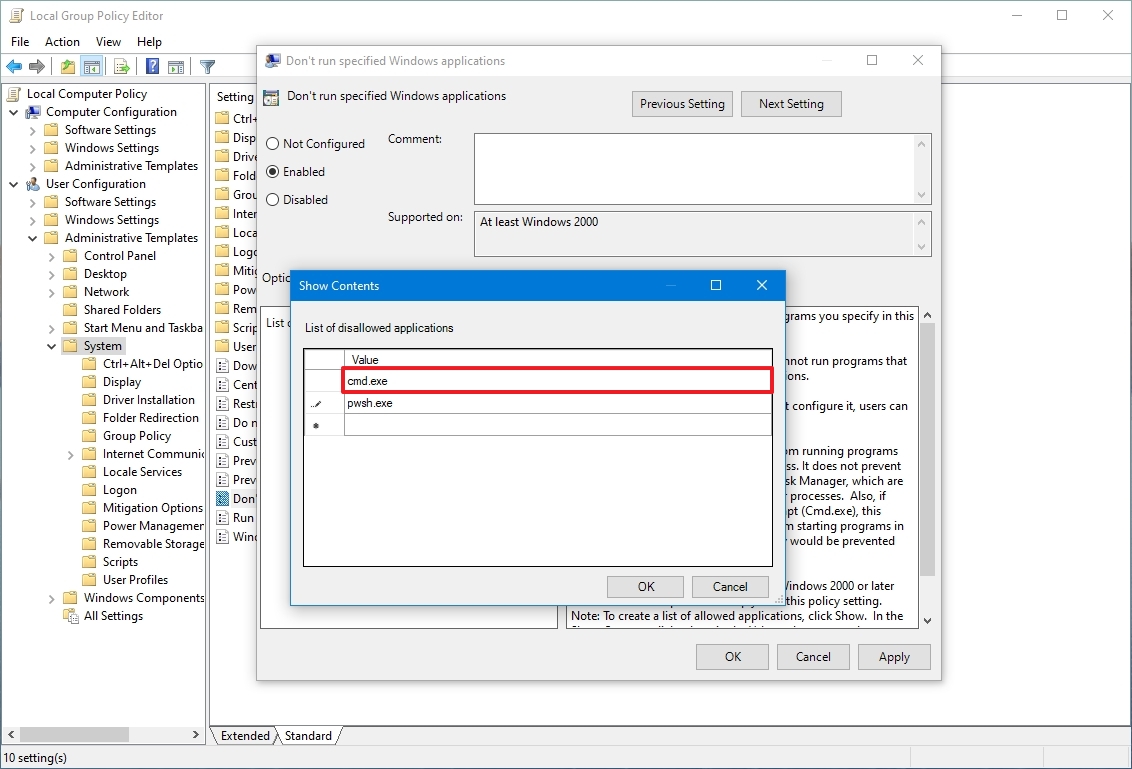
- Confirm the names of the apps you want to block.
- Quick note: Only add one name per line. Also, you need to specify the ".exe" file. For example, to block Command Prompt, you would add cmd.exe and pwsh.exe to block the built-in version of PowerShell.
- Click the Apply. button
- Click the OK button.
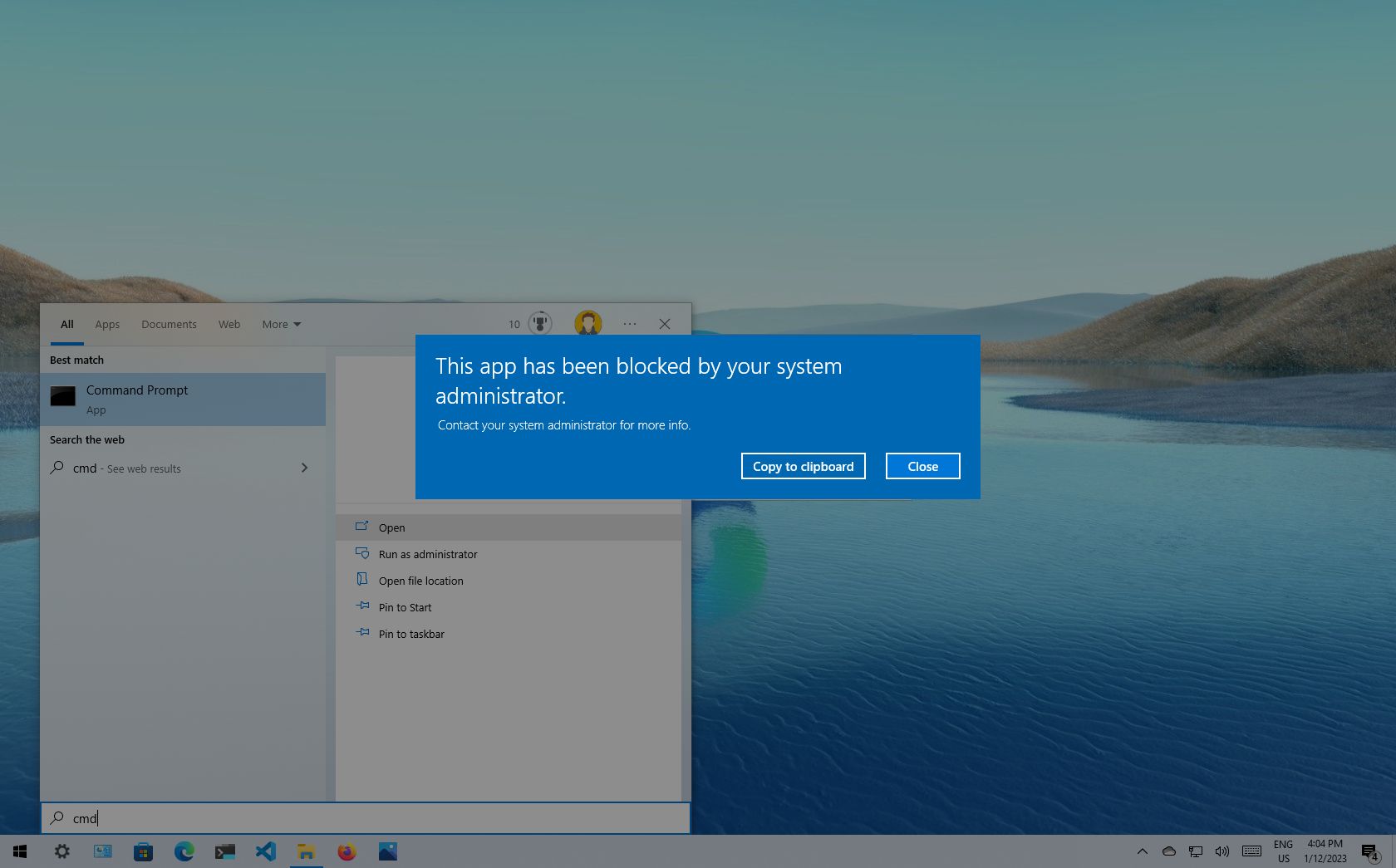
Once you complete the steps, the apps you specified should no longer be accessible by users configured on the device. The settings should apply immediately, but you may need to restart the computer for the changes to take effect in some cases.
You can always revert the changes using the same instructions, but in step 5, select the "Not configured" option.
These instructions will disable access to the apps for all users. However, you can also use the Local Group Policy Editor to apply the settings to one or multiple users while excluding the reset.
All the latest news, reviews, and guides for Windows and Xbox diehards.
How to disable apps access from Security Policy
To prevent users from launching specific apps with the Local Security Policy on Windows 10, use these steps:
- Open Start.
- Search for Local Security Policy and click the top result to open the app.
- Double-click to expand the "Software Restriction Policies" branch.
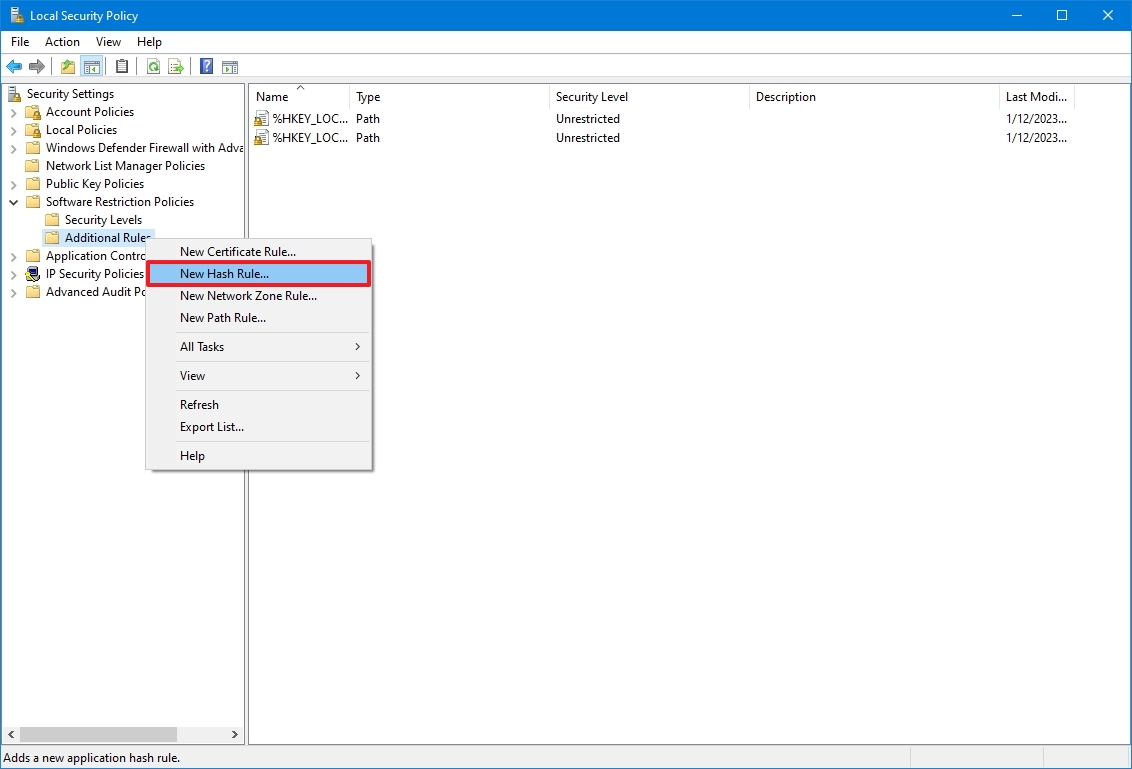
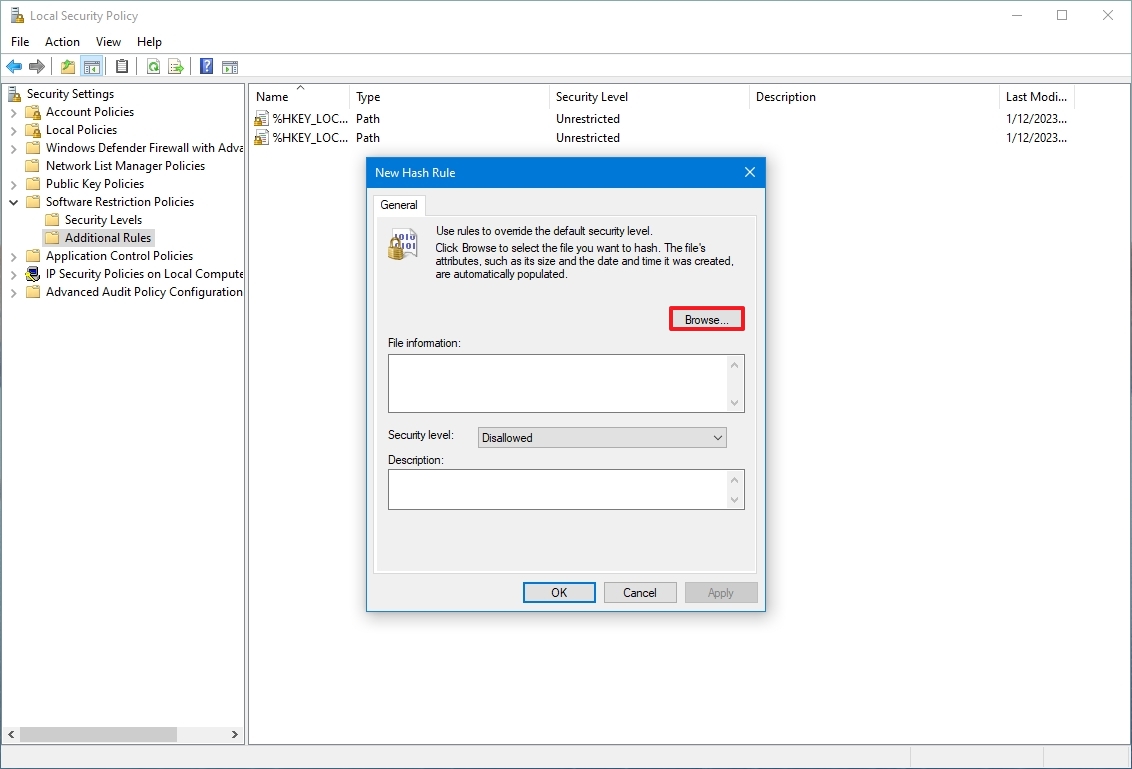
- Right-click the Additional Rules category and select the "New Hash Rule" option.
- Quick tip: If the category is not available, right-click the "Software Restriction Policies" branch and select the "New Software Restriction Policies" option.
- Click the Browse button.
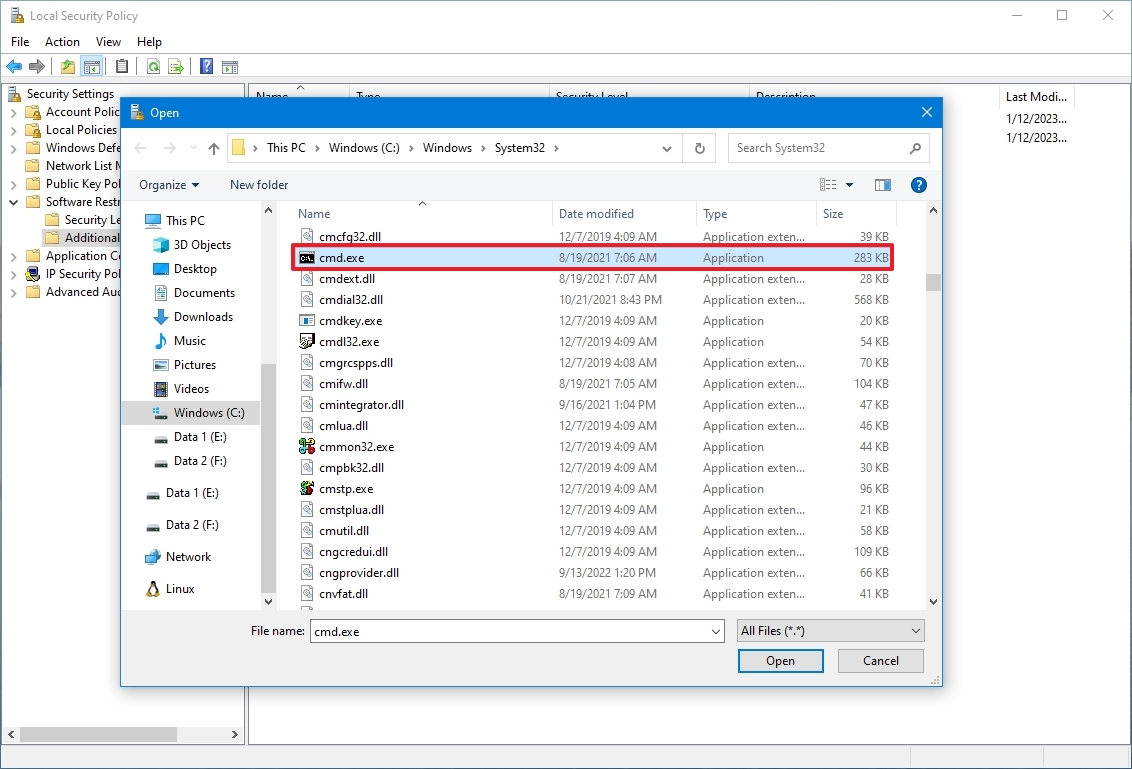
- Browse to the location of the application folder.
- Select the main executable (.exe) file – for example, cmd.exe.
- Click the Open button.
- Click the Apply button.
- Click the OK button.
- Restart the computer.
After you complete the steps, users will no longer be able to launch the application you specified. You can always repeat the steps to block access to other desktop applications.
If you want to undo the changes, you can use the same instructions outlined above, but on step 4, right-click the hash of the app currently blocked and select the "Delete" option.
If you are disabling applications to prevent users from making system changes, you can use these instructions to restrict access to PowerShell or Command Prompt. You can also limit access to the Task Manager and Registry.
Furthermore, you can try switching the account type to "Standard User" to prevent users from making system changes and make the account more secure. The only caveat with this approach is that users will still have access to apps like PowerShell and Command Prompt to perform some non-administrative tasks.
More resources
For more helpful articles, coverage, and answers to common questions about Windows 10, visit the following resources:
- Windows 11 on Windows Central — All you need to know
- Windows 10 on Windows Central — All you need to know

Mauro Huculak has been a Windows How-To Expert contributor for WindowsCentral.com for nearly a decade and has over 22 years of combined experience in IT and technical writing. He holds various professional certifications from Microsoft, Cisco, VMware, and CompTIA and has been recognized as a Microsoft MVP for many years.

 Windows Central Insider
Windows Central Insider