How to make sure data you store in the cloud stays secure

In the wake of high-profile hacks and thanks to awareness campaigns like Data Privacy Day, many people are coming to the realization that their cloud storage isn't exactly as secure as they thought. While all the blame in the world can be placed on the hackers responsible, this sort of thing will almost certainly happen again, and placing blame won't protect your data if it is targeted. No matter what cloud storage service you use, there are a few things you can do to ensure sensitive data remains as secure as possible.
- Dealing with passwords
- Setting up two-factor authentication
- Encrypting your data in the cloud
- Avoiding phishing and scams
Dealing with passwords
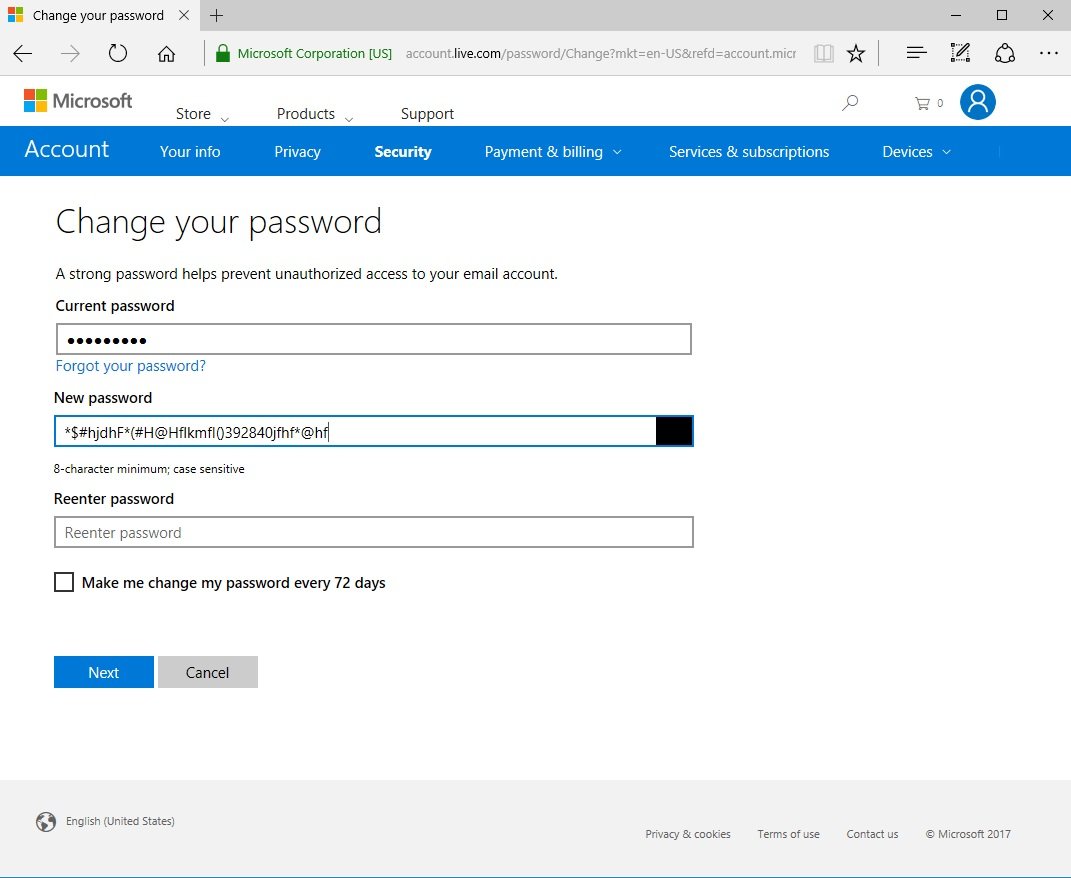
When it comes to passwords, there are some general rules to follow that will make it harder for hackers to guess or brute-force their way past the gates you set up.
Ditch old, weak passwords
The old TV trope of guessing a user's password by simply typing "password" didn't come about for no reason. Plenty of people used to (and likely still do) use a variation of this weak password.


Setting your password to something as easy to remember as "password" or something close — like your birthday, hometown or address — means any interested hackers will have an easy time getting in.
A strong password is a long password that includes letters, numbers, and symbols arranged in no particular pattern. These passwords are virtually impossible to guess, and using brute force takes longer for longer passwords. These can be difficult to remember, but that's where password managers come in.
Use different passwords for different services
Creating a great password for your cloud storage account will keep your data safer in the long run, but not if you use that same password for other services. Say you create an account on a random shopping website so that you can receive newsletters about sales, and you use the same great password you used for, say, OneDrive.
Now it's revealed that the shopping website didn't really protect its users' information, and an interested hacker has a new collection of passwords. Because your password isn't different between services, that one weak website has potentially compromised a collection of services you use every day.
All the latest news, reviews, and guides for Windows and Xbox diehards.
Use a password manager to keep track of your passwords
One of the main reasons people use short, common passwords is because they're easy to remember. Now that you have a different strong password for each service, they're not exactly easy to keep track of. Enter password managers. These services will keep track of all your passwords, will auto-fill password fields, and will even generate quality passwords so you don't have to. There are plenty of password managers out there, but check out our choice for the best:
True Key manages all your passwords in Edge with no hassle
Play it smart when using security questions
Plenty of services will ask you to provide a security question or two when you sign up. These security questions can be used in the event of a forgotten password, but they can also be used as a way for other people to get into your account. Why? Most security questions involve something about your school, your hometown, or your mother's maiden name. In plenty of cases, especially if you're at all in the public light, the answers to these questions can be researched and found.
If you have the option, forego adding security questions. If the service you're signing up for requires you to add a security question or two, don't use answers that can be researched. Instead, create a long, strong password as an answer to the security question. Store the "answers" in your password manager and access them if the need arises.
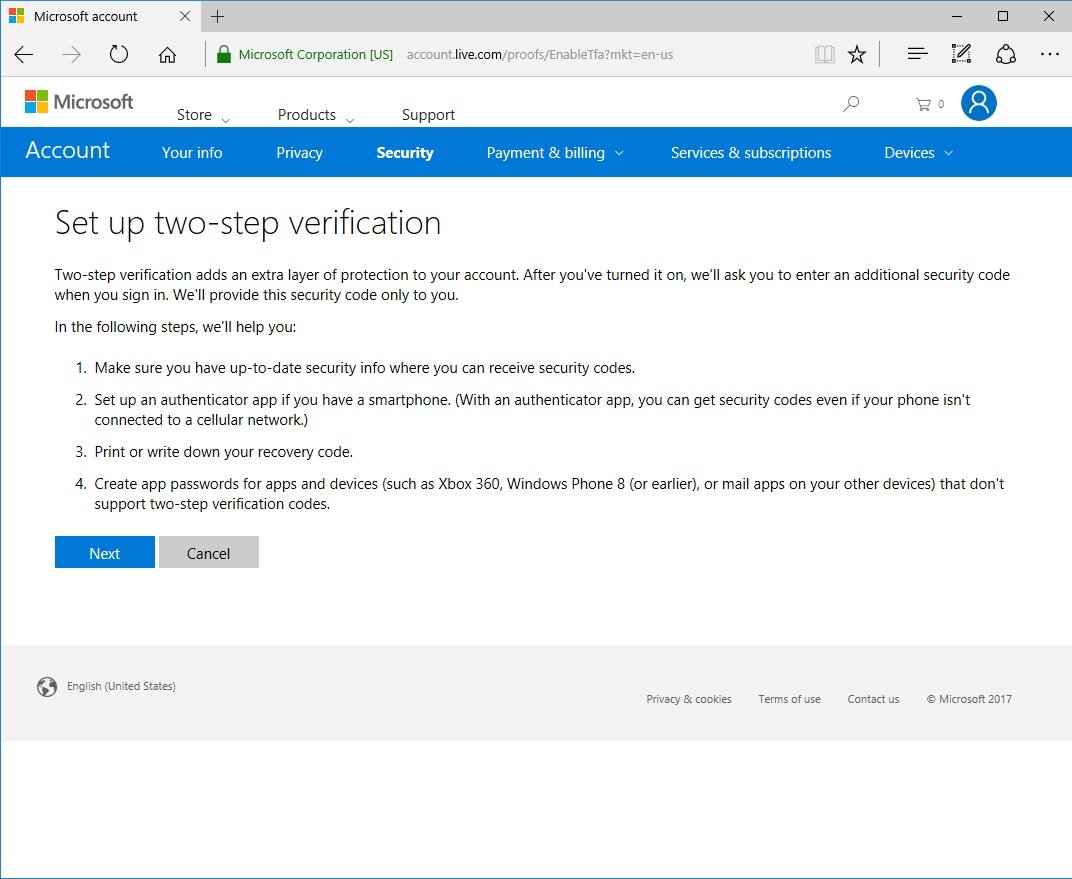
Setting up two-factor authentication
On top of creating a strong password as an access point to your data, setting up two-factor authentication (2FA) should be done wherever possible. Once 2FA is set up, you'll receive a unique code that must also be entered. Many services will text a code to your phone, while others take advantage of dedicated apps that deal with distributing your 2FA codes. This extra step will take more time to log in, but it is invaluable.
How to easily check if your favorite service has two-factor authentication
YubiKey
YubiKey is a neat little tool that gives you 2FA to carry around in your pocket. It's essentially a USB stick you can put on your keyring, or around your neck, that is compatible with Windows Hello and a number of other services, including Dropbox and several password managers.
In order to, say, get into your password manager's vault of saved passwords (an incredibly potent vault), you have to enter the master password plus insert the YubiKey into a USB slot on your PC. Any would-be hackers would need to actually get the physical YubiKey from you, providing that crucial secondary authentication method.
Encrypting your data in the cloud
When you upload photos and data to the cloud, you expect some privacy and security, which, in most cases, comes in the form of encryption. And not only transit encryption, but resting encryption for your files that are already saved in the cloud. Many services already provide this level of security — some require you to go with business accounts — but there is still a problem. In most of these cases, the cloud service itself holds the key to the encryption, meaning if they are compromised, your data will potentially be served up on a platter.
Instead of trusting the cloud service to safeguard the key to your data, you can take matters into your own hand by encrypting especially sensitive files before they even leave your PC. There are plenty of these encryption services available, including Boxcryptor and Rclone, but make sure to pick one that is compatible with your cloud service of choice. Remember, you don't have to personally encrypt everything that goes into the cloud, but you'll be glad if you did in the event of a hack.
If you're particularly concerned about the security of the internet connection you're using — most important if you frequent public spaces with free Wi-Fi — adding a VPN service to the mix isn't a bad idea. It will up your privacy when it comes to essentially any online activity, which is a major goal here.
If you're not sure where to start, we've put together a beginner's guide that will get you up to speed, and we've also rounded up the best VPN services out there.
Best VPN services
Avoiding phishing and scams
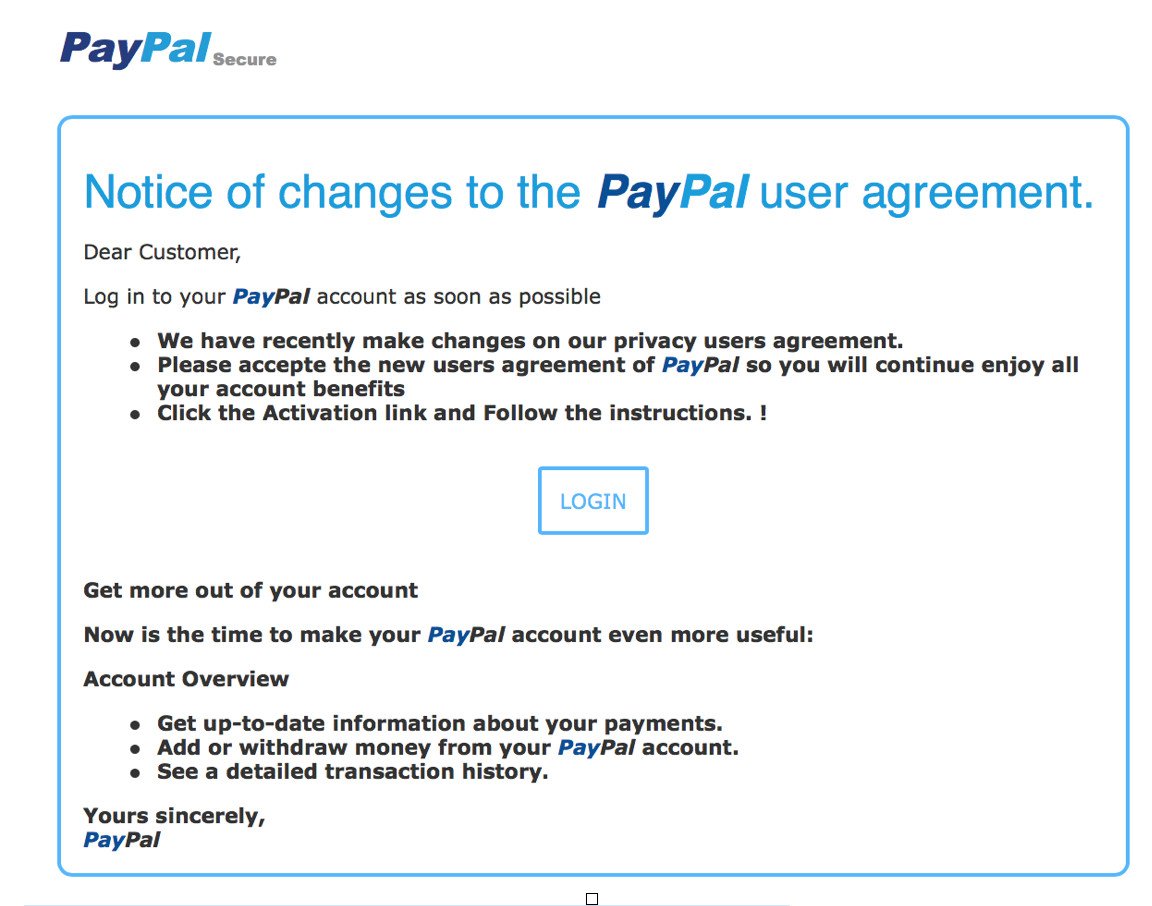
Now that you've created a strong password and have set up 2FA, you must remain vigilant when it comes to phishing. Phishing tactics usually involve an enticing or official-looking email sent your way that requires you to click a link and enter your password on the website the link opens.
These nefarious sites will closely resemble official sites, but they are designed to nab your username and password — no matter how strong — with your help. If you ever receive an email asking you to sign in through a link, ignore it.
Instead, navigate your way to the website in question by typing it into your browser. This ensures you're accessing the real website, and any problems mentioned in the suspect email (if they exist) should also be evident when you log in.
The number one rule to avoid phishing is to be wary at all times when navigating the internet. If something seems off or a little too good to be true, it probably is.
The bottom line
Although nothing is ever 100 percent safe online, following the methods explained above will help keep your data safer than before. If you're sending private documents to other people, don't forget to ensure they're also following these guidelines for keeping online data safe.
Updated January 28, 2019 It's Data Privacy Day again and we've refreshed this article in the hopes that it will help keep more than a few people from any unfortunate leaks or hacks.

Cale Hunt brings to Windows Central more than nine years of experience writing about PC gaming, Windows laptops, accessories, and beyond. If it runs Windows or in some way complements the hardware, there’s a good chance he knows about it, has written about it, or is already busy testing it.

 Windows Central Insider
Windows Central Insider