How to check if someone logged into your Windows 10 PC
Did you ever wonder who had access to your PC and when it happened? In this guide, we'll show you the steps to use Windows 10's auditing feature to track login attempts.
On Windows 10, you can enable the "Auditing logon events" policy to track login attempts, which can come in handy in many scenarios, including to find out who has been using your device without permission, troubleshoot certain problems, and more.
When the policy is enabled, Windows 10 can track local, and network logins whether they're successful or not, and every event will include the account name and the time of when it happened among other information. Typically, this feature is reserved for organizations, but anyone can use it as long as you know the process.
In this Windows 10 guide, we'll walk you through the steps to see when and who has signed into your device using Group Policy and the Event Viewer.


How to enable logon auditing policy on Windows 10
If you're running Windows 10 Pro, you can use the Local Group Policy Editor to enable the "Audit logon events" policy to track success and feature sign-in attempts on your device.
Important: Group Policy isn't available on Windows 10 Home, but interesting enough, at least login auditing for successful attempts comes enabled by default in this edition. If you're running Windows 10 Home, you can skip these steps, and jump right into the Event Viewer instructions.
- Use the Windows key + R keyboard shortcut to open the Run command.
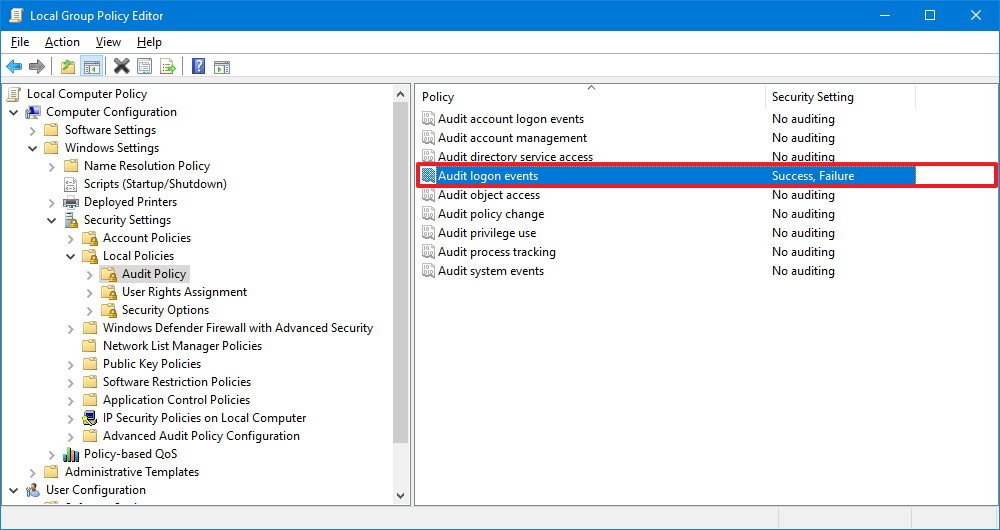
- Type gpedit.msc and click OK to open the Local Group Policy Editor.
- Browse the following path:
Computer Configuration > Windows Settings > Security Settings > Local Policies > Audit Policy - On the right side, double-click the Audit logon events policy.
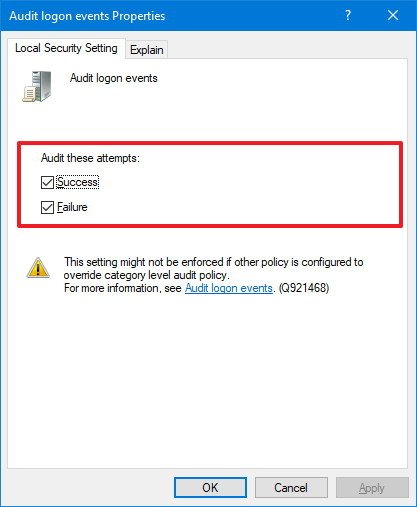
- Check the Success and Failure options.
- Click Apply.
- Click OK.
After completing the steps, Windows 10 will track every login attempt to your device whether it's successful or not.
If you're no longer interested in tracking logins on your computer, you can use the same instructions, but on step No. 5, make sure to clear the Success and Failure options.
All the latest news, reviews, and guides for Windows and Xbox diehards.
How to see who logged into Windows 10
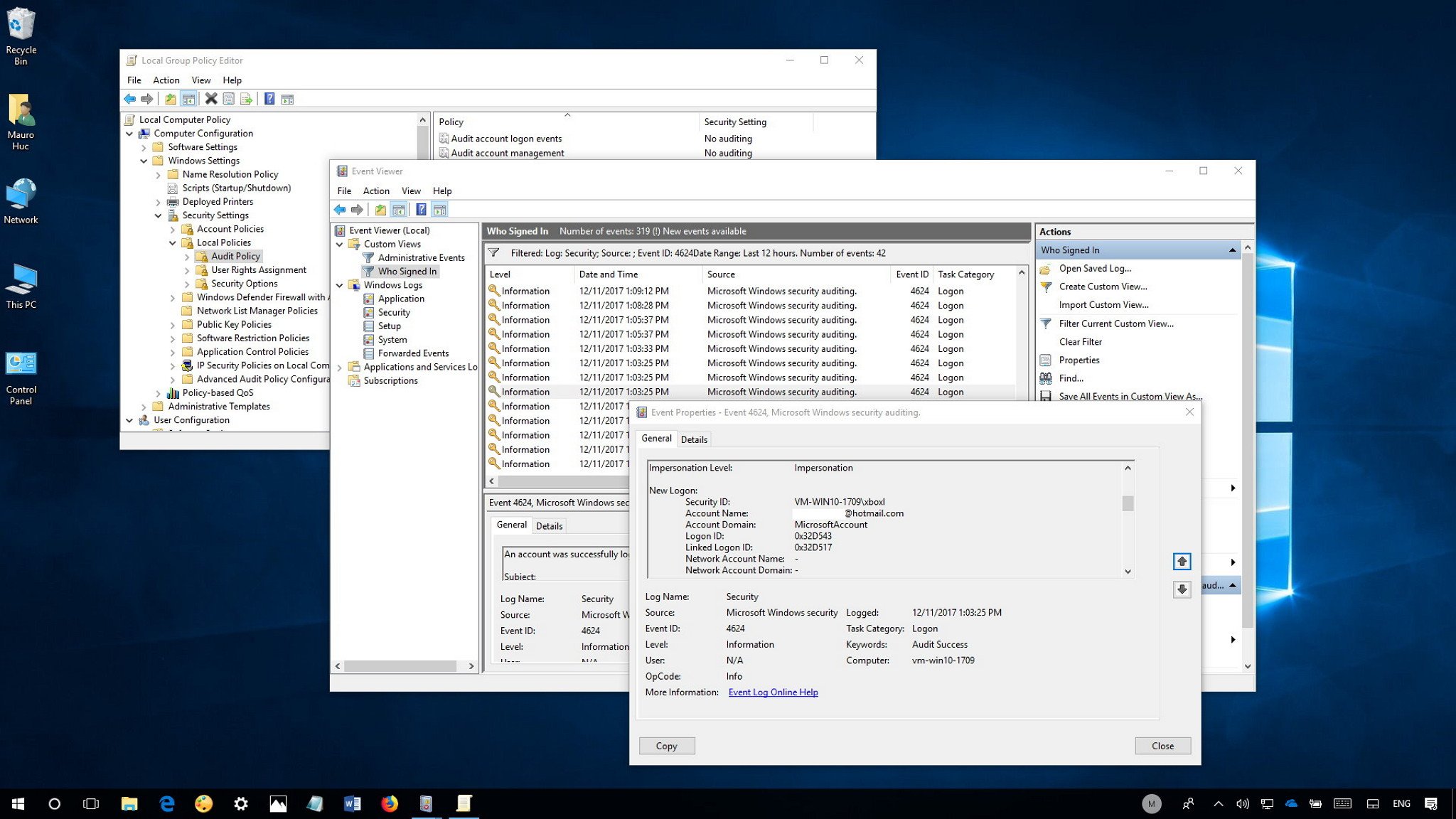
Once you've configured Windows 10 to audit logon events, you can use the Event Viewer to see who signed into your computer and when it happened.
- Open Start.
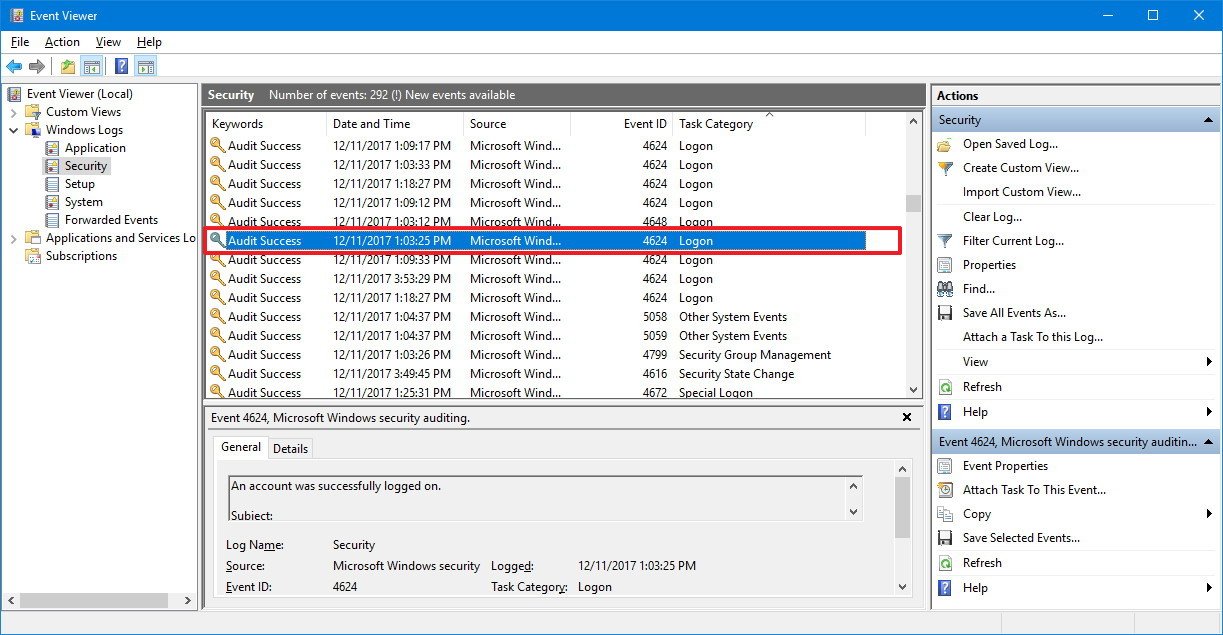
- Search for Event Viewer, click the top result to launch the experience.
- Browse the following path:
Event Viewer > Windows Logs > Security - Double-click the event with the 4624 ID number, which indicates a successful sign-in event.Quick Tip: On Windows 10 Pro, you can also double-click the event with the 4625 ID number to see unsuccessful attempts, or event ID 4634 to see when the user logged off.
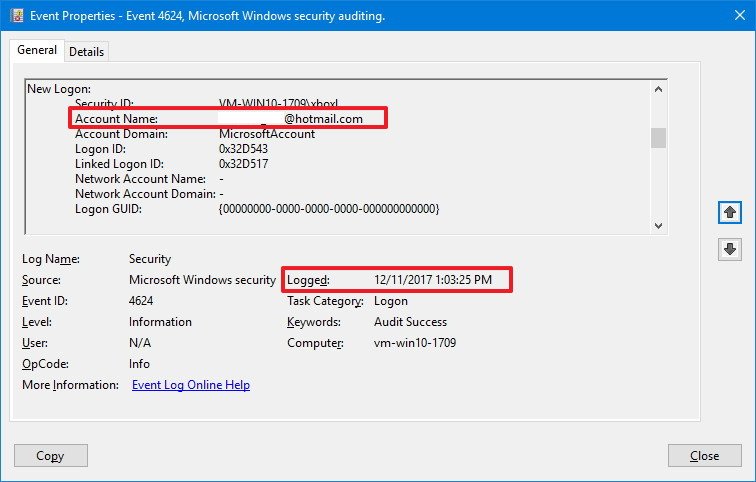
In the event log, you'll find a lot of useful information, but you can simply look at the Logged section to figure out when the event took place, and within the "General" tab, look under New Logon to find out the account that was granted permission to your computer.
Using filters
The "Security" page logs many login attempts, including from background services, as such you may need to browse a few events until you find the information you're seeking. However, you can speed up the process using the Event Viewer filter feature to create a custom view to see only the login attempts.
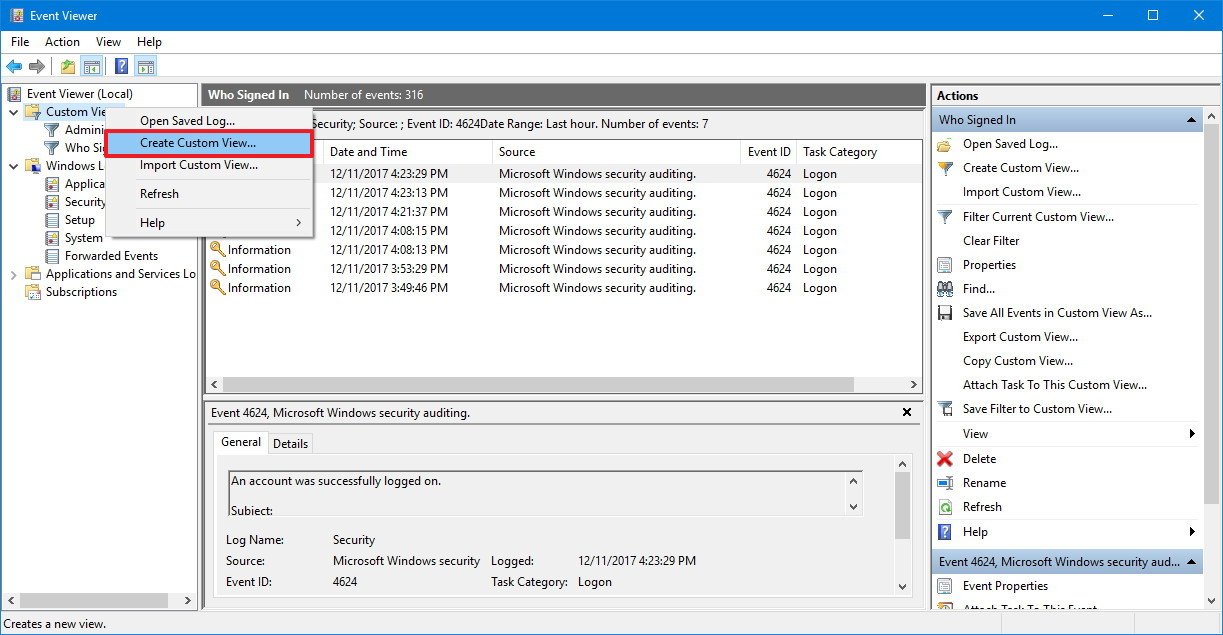
- Right-click Custom Views.
- Select the Create Custom View option.
- Use the Logged drop-down menu, select a time range you want.
- Check the By log option.
- Use the "Event logs" drop-down menu, and select Security under "Windows Logs."
- In the "All Event IDs" field, type 4624.
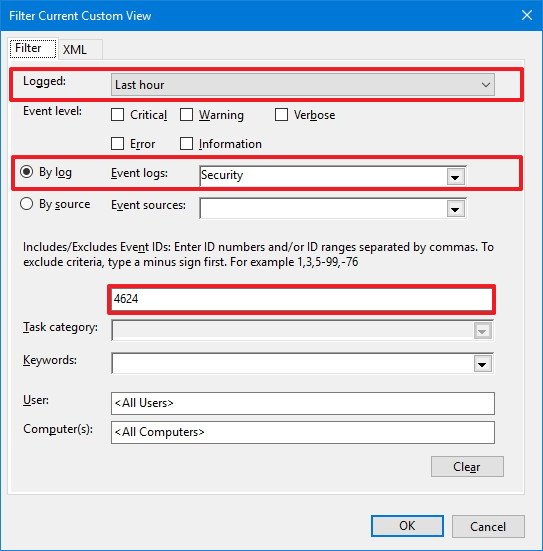
- Click OK.
Once you've completed the steps, you'll be able to find out who and when someone successfully signed into your device more quickly.
Although we're focusing this guide on Windows 10, you can also refer to these instructions to track logins to your device on previous versions, including Windows 8.1 and Windows 7.
More Windows 10 resources
For more helpful articles, coverage, and answers to common questions about Windows 10, visit the following resources:
- Windows 10 on Windows Central – All you need to know
- Windows 10 help, tips, and tricks
- Windows 10 forums on Windows Central

Mauro Huculak has been a Windows How-To Expert contributor for WindowsCentral.com for nearly a decade and has over 22 years of combined experience in IT and technical writing. He holds various professional certifications from Microsoft, Cisco, VMware, and CompTIA and has been recognized as a Microsoft MVP for many years.

 Windows Central Insider
Windows Central Insider