How to use 'netstat' command on Windows 11 and 10
You can use the netstat command to monitor and troubleshoot many network problems, and in this guide, I'll show you how.
On Windows 11, the Network Statistics (netstat) tool has been around for a long time (including on Windows 10 and older versions), and it's a command-line utility you can use in Command Prompt to display statistics for all network connections. It allows you to understand open and connected ports to monitor and troubleshoot networking problems for systems or apps.
The tool helps you to list active network (incoming and outgoing) connections and listening ports. You can view network adapter statistics and statistics for protocols (such as IPv4 and IPv6). You can even display the current routing table and much more.
In this how-to guide, I'll show you the steps to use the netstat command to examine connections to discover open and connected network ports on Windows 11 (and 10).


How to use netstat on Windows 11 and 10
In the client version of Windows, you can get started with the Network Statistics tool with a simple command, but then you have a lot of options to view different network activities, and here's how.
Netstats basics
To get started with netstat, use these steps:
- Open Start.
- Search for Command Prompt, right-click the top result, and select the Run as administrator option.
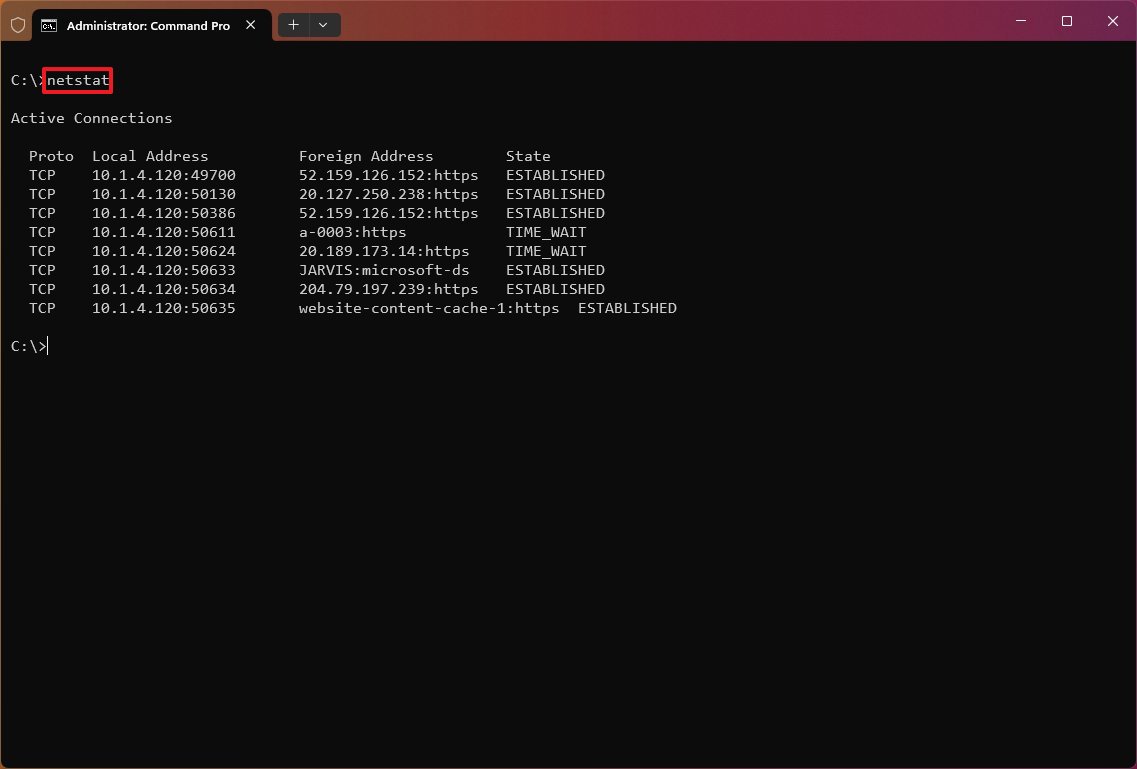
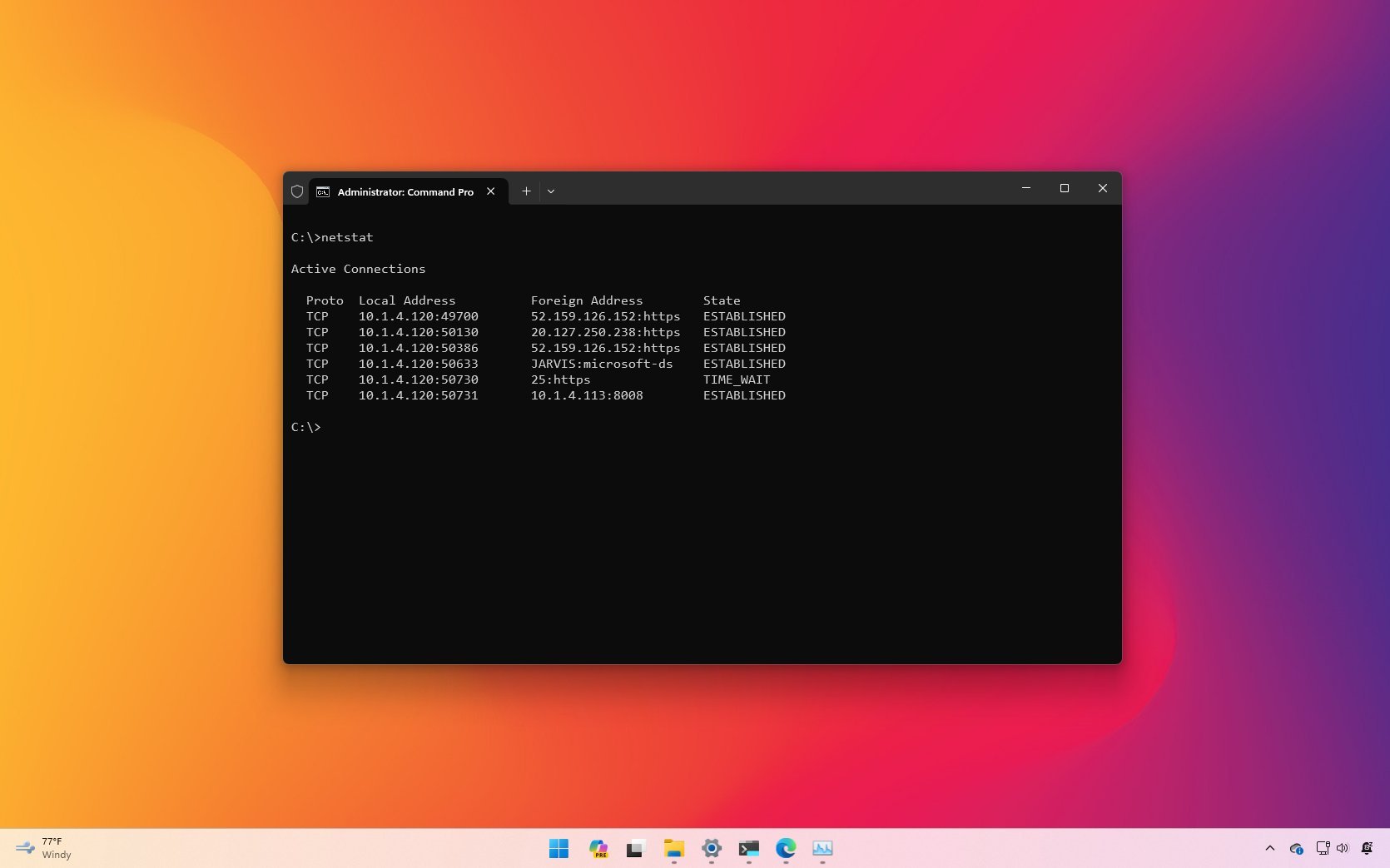
- Type the following command to show all active TCP connections and press Enter: netstat
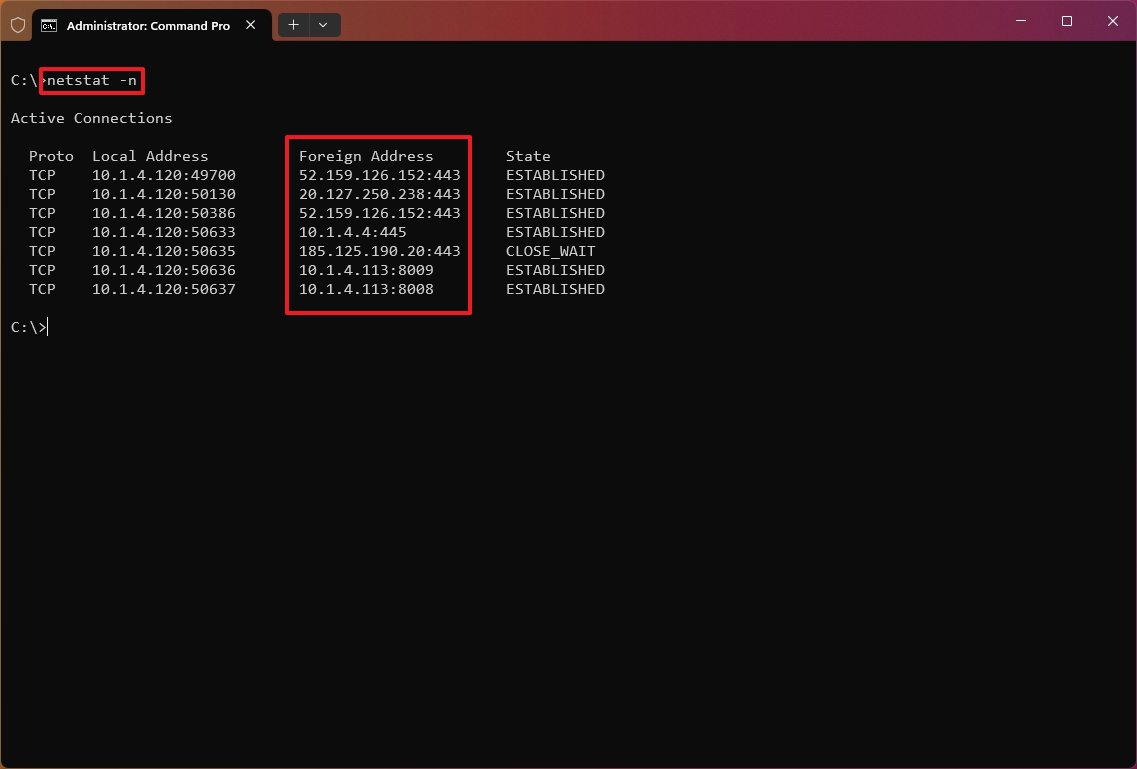
- (Optional) Type the following command to display active connections showing numeric IP address and port number instead of trying to determine the names and press Enter: netstat -n
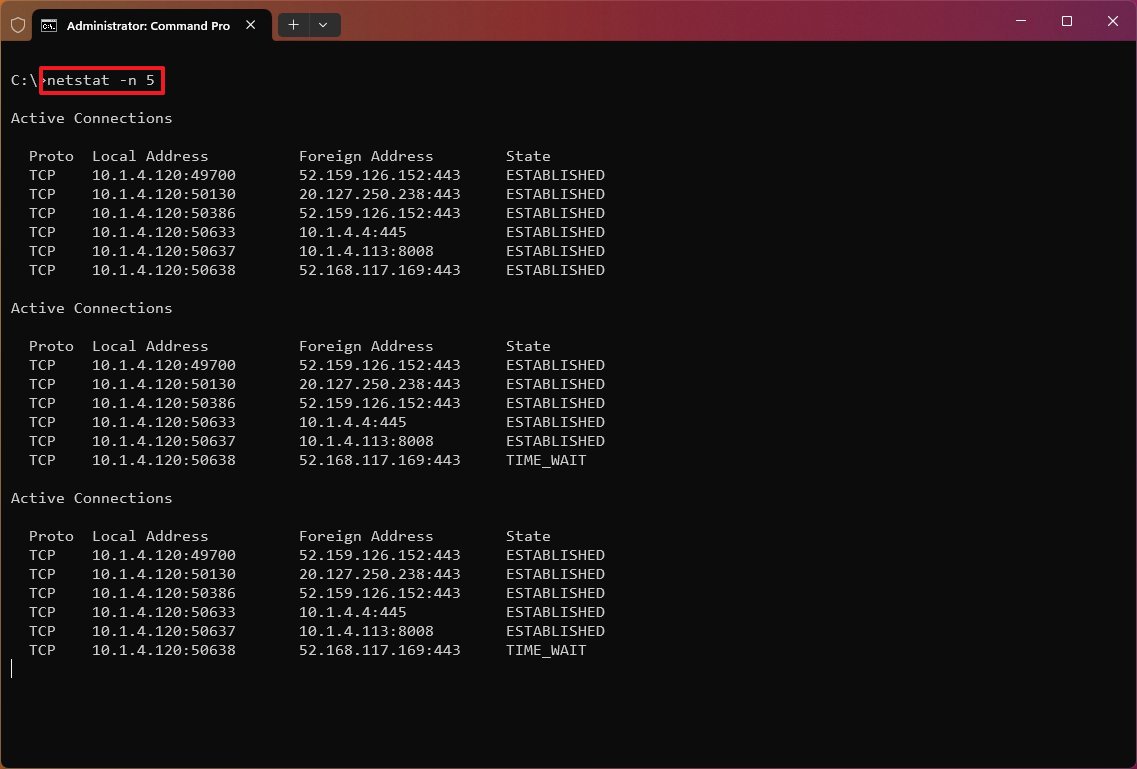
- (Optional) Type the following command to refresh the information at a specific interval and press Enter: netstat -n INTERVAL
In the command, replace "INTERVAL" with the number (in seconds) to re-display the information. This example refreshes the command in question every five seconds: netstat -n 5
- Quick note: When using the interval parameter, you can terminate the command using the "Ctrl + C" keyboard shortcut.
Once you execute the command, it'll return a list of all active connections in four columns, including:
All the latest news, reviews, and guides for Windows and Xbox diehards.
- Proto: Shows the connection protocol (TCP or UDP).
- Local Address: Shows the computer's IP address followed by a semicolon with the port number of the connection. The double-semicolon inside brackets indicates the local IPv6 address, and "0.0.0.0" refers to the local address.
- Foreign Address: Lists the remote device's IP (or FQDN) address with the port number after the semicolon port name (for example, HTTPS, HTTP, Microsoft-ds, and wsd).
- State: Indicates where the connection is active (established), the local port has been closed (time_wait), and the program hasn't closed the port (close_wait). Other status include, closed, fin_wait_1, fin_wait_2, last_ack, listen, syn_received, syn_send, and timed_wait.
Netstat parameters
The tool also includes several parameters you can use to display different information about the network connections on Windows 11 (and 10).
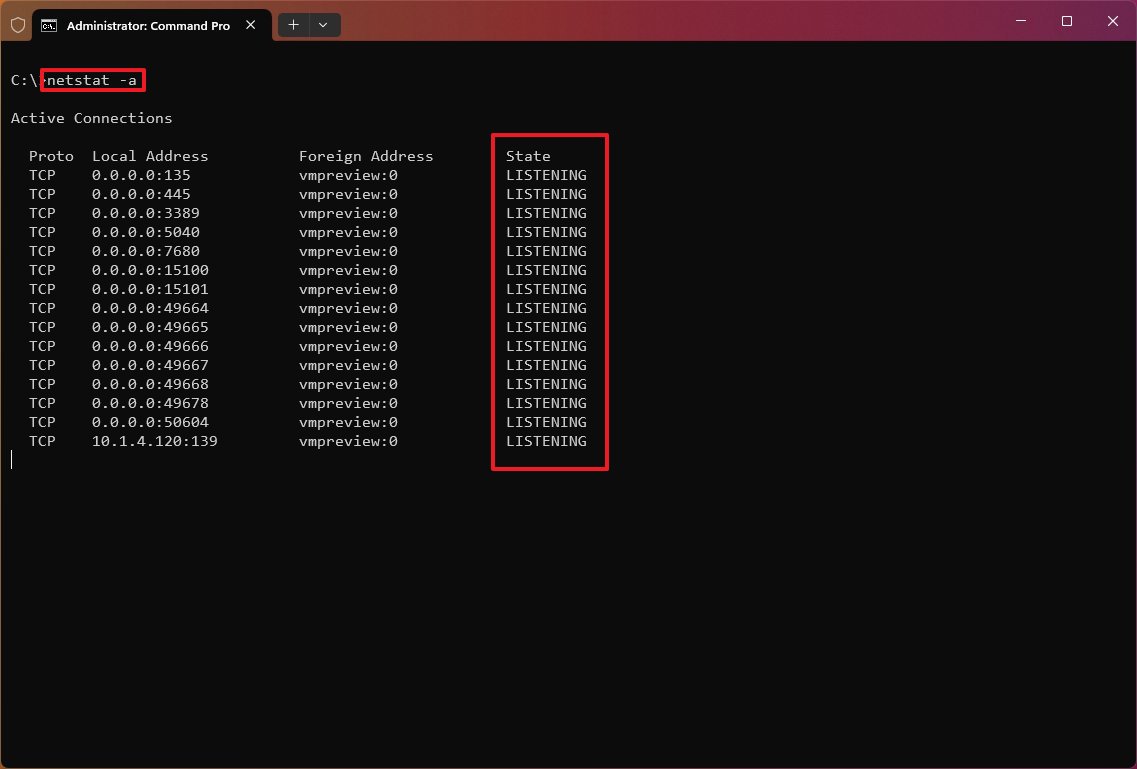
Show active and inactive connections
The "netstat -a" command displays all active and inactive connections and the TCP and UDP ports the device is currently listening to.
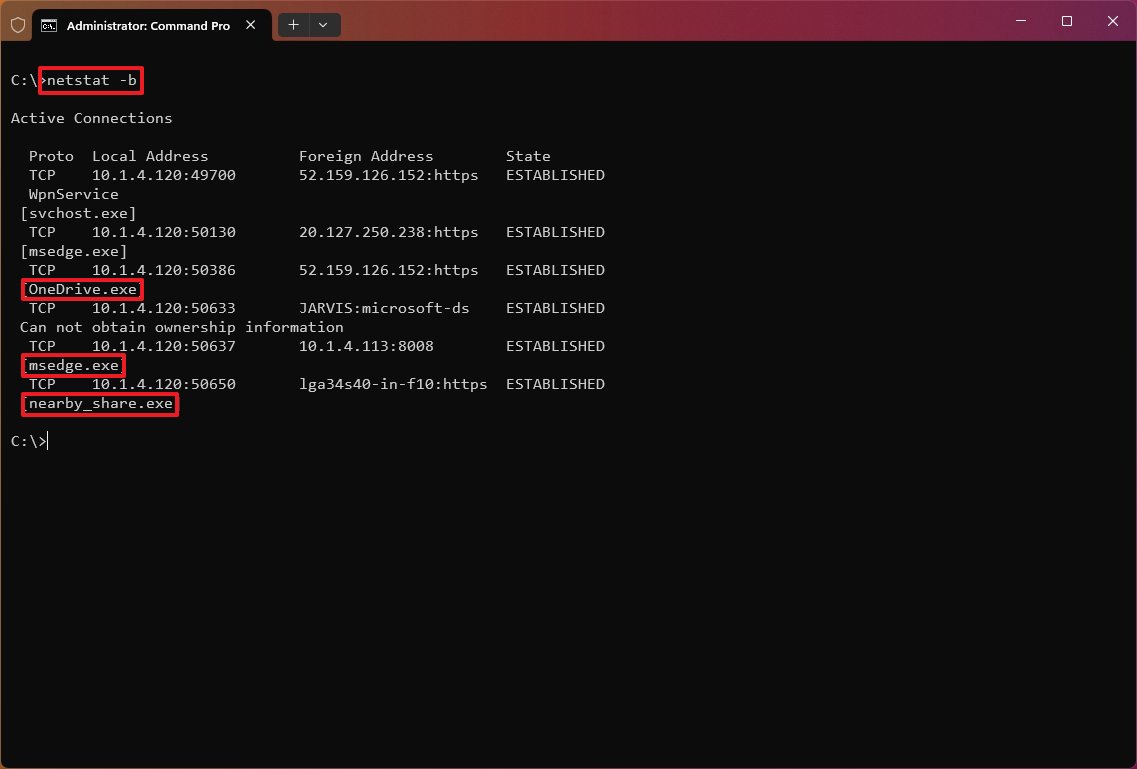
Show executable information
The "netstat -b" command lists all the executables (applications) associated with each connection. Sometimes, applications may open multiple connections.
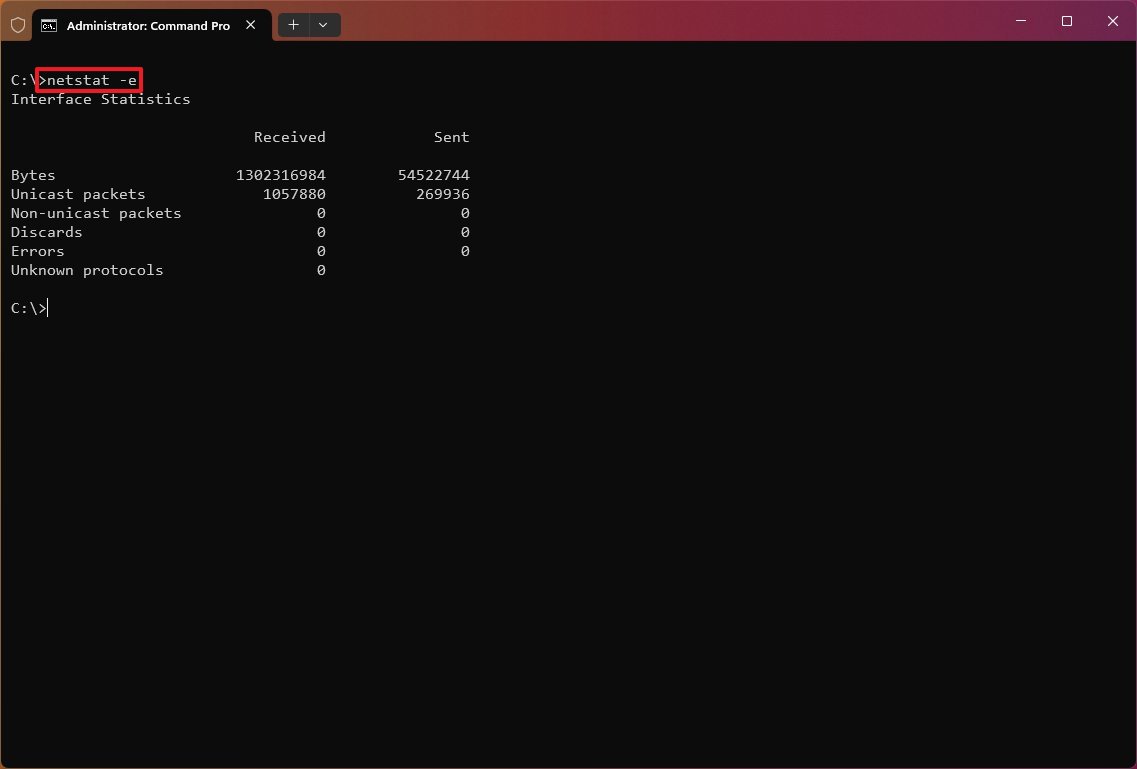
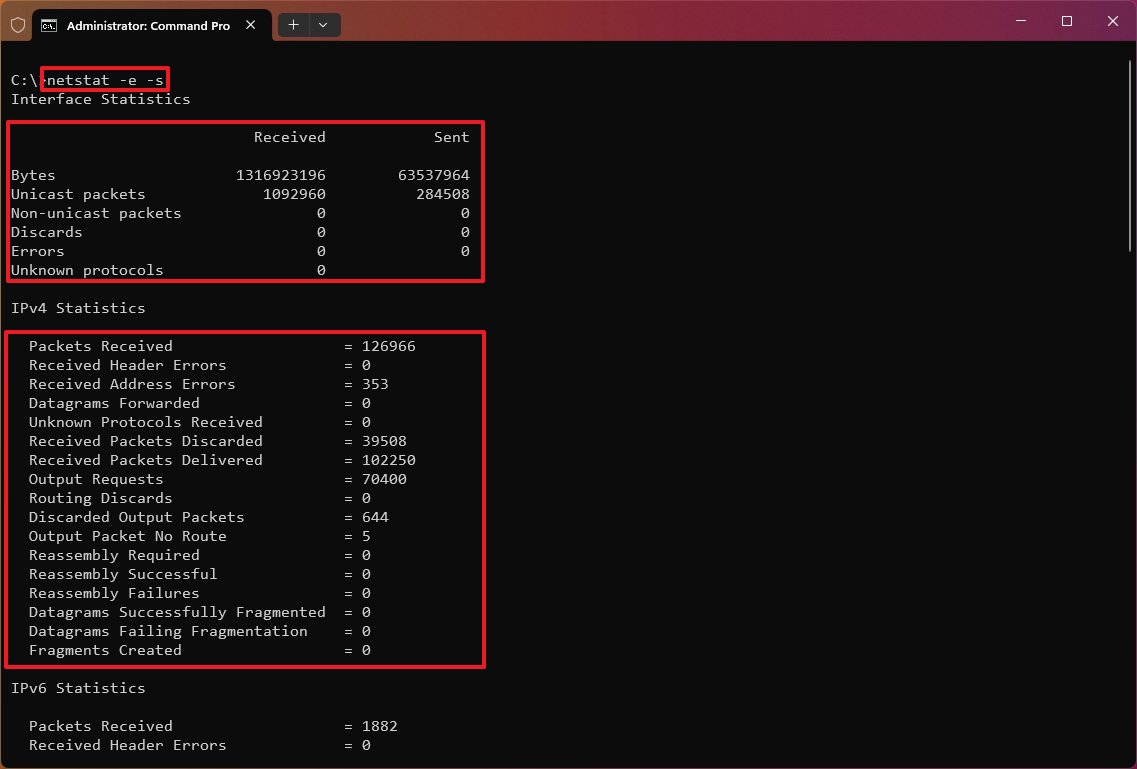
Show network adapter statistics
The "netstat -e" command generates a statistic of the network interface, which shows information like the number of bytes, unicast, and non-unicast sent and received packets. You can also see discarded packets, errors, and unknown protocols, which can help you troubleshoot networking problems.
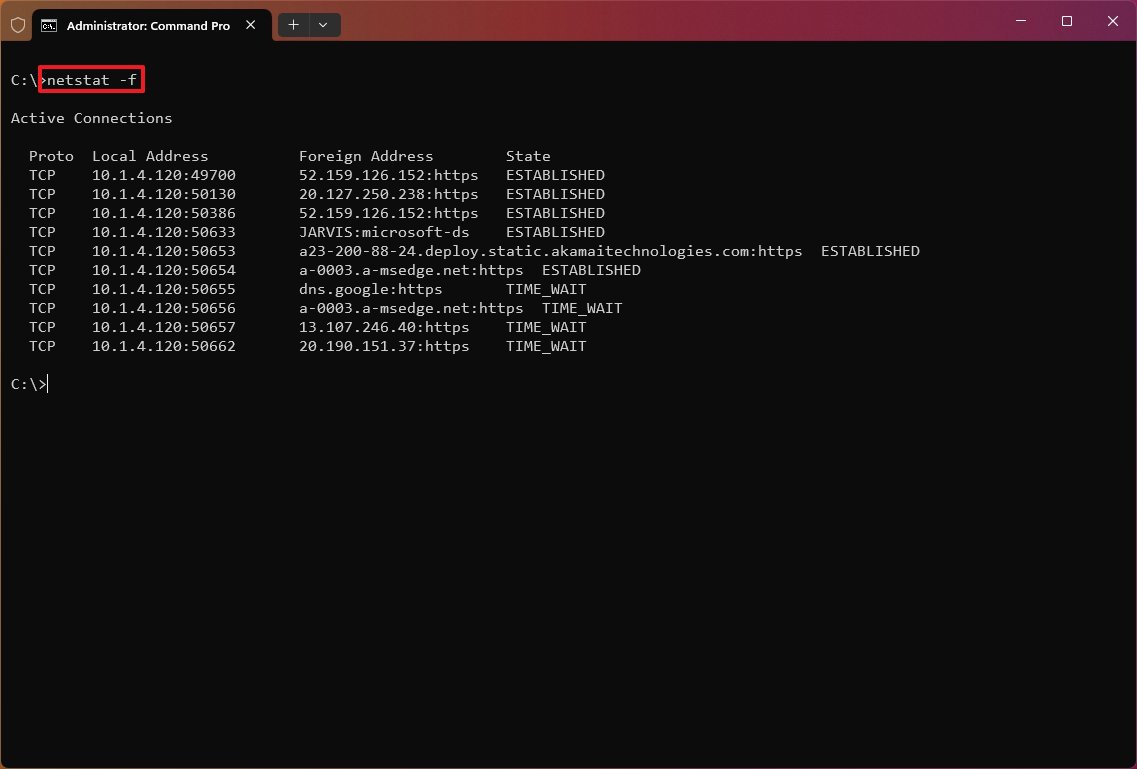
Show FQDNS for foreign addresses
The "netstat -f" command shows the fully qualified domain name (FQDN) for foreign addresses. For example, "a23-200-88-24.deploy.static.akamaitechnologies.com:https" instead of "a23-200-88-24:http" or "23.200.88.24".
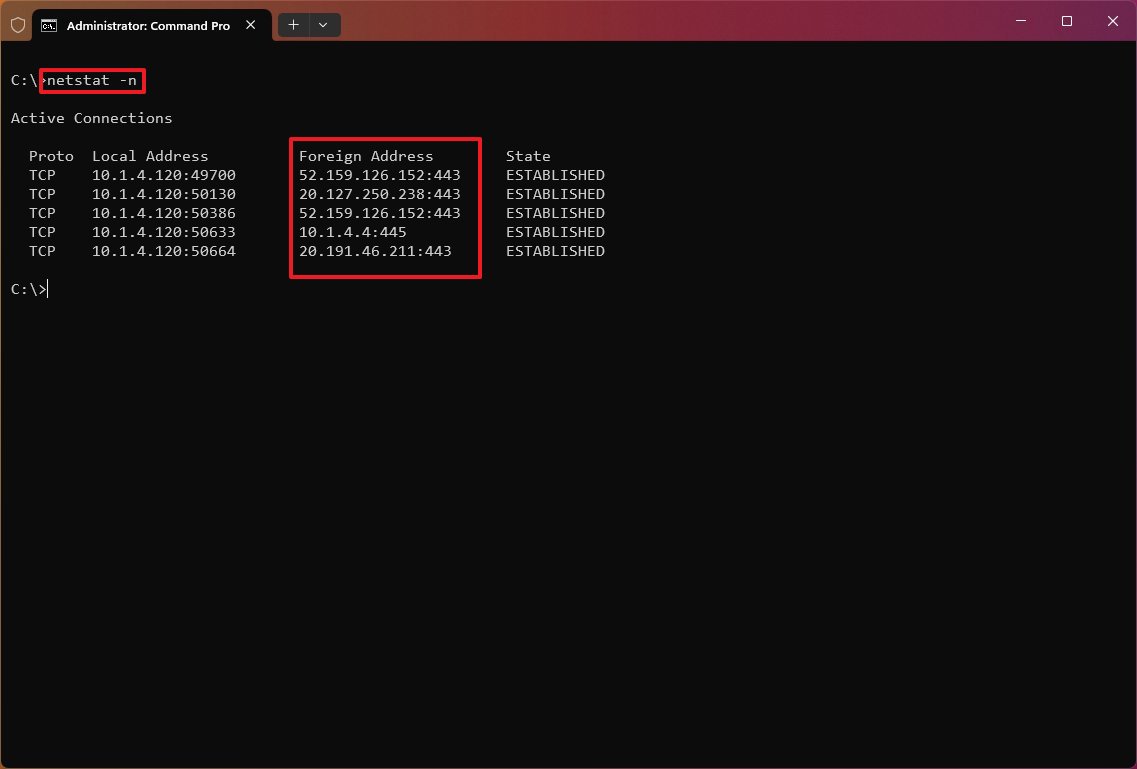
Show numerical form
The "netstat -n" command displays the addresses and ports in numerical form—for example, 52.159.126.152:443.
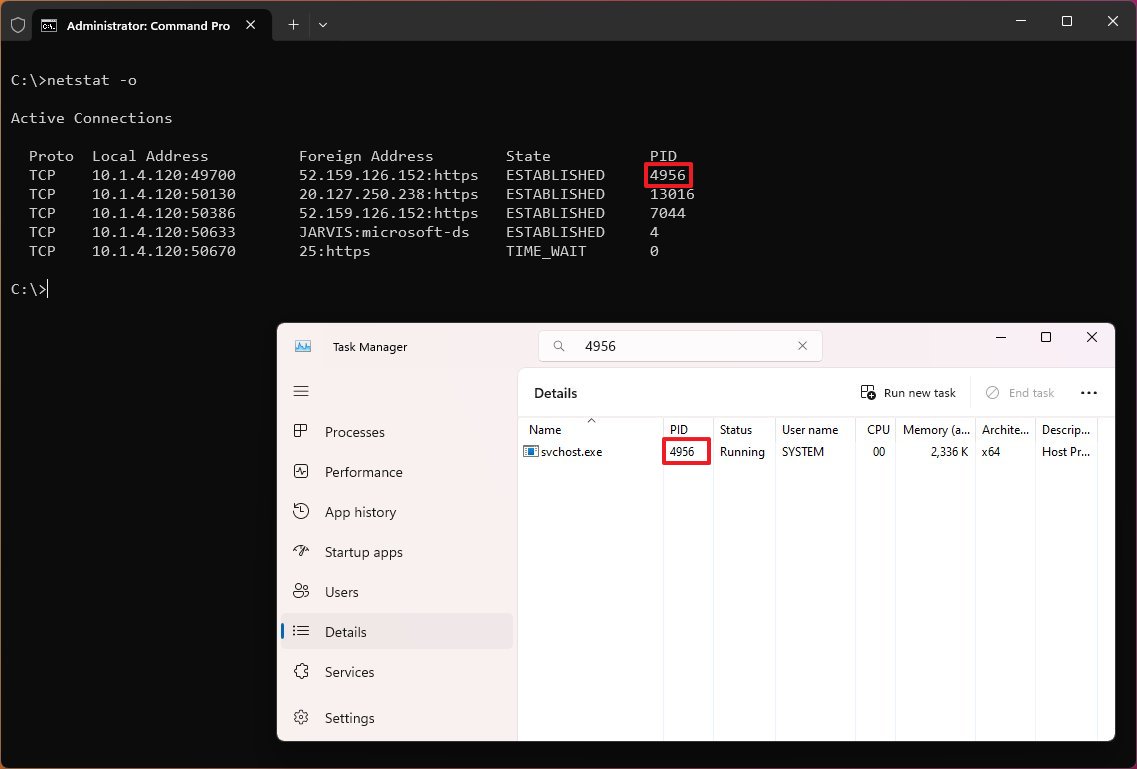
Show process ID
The "netstat -o" command shows active TCP connections like "netstat," but with the difference that adds a fifth column to display the Process ID (PID) for each connection. The processes available in this view are the same in the "Details" tab of Task Manager, which also reveals the application using the connection.
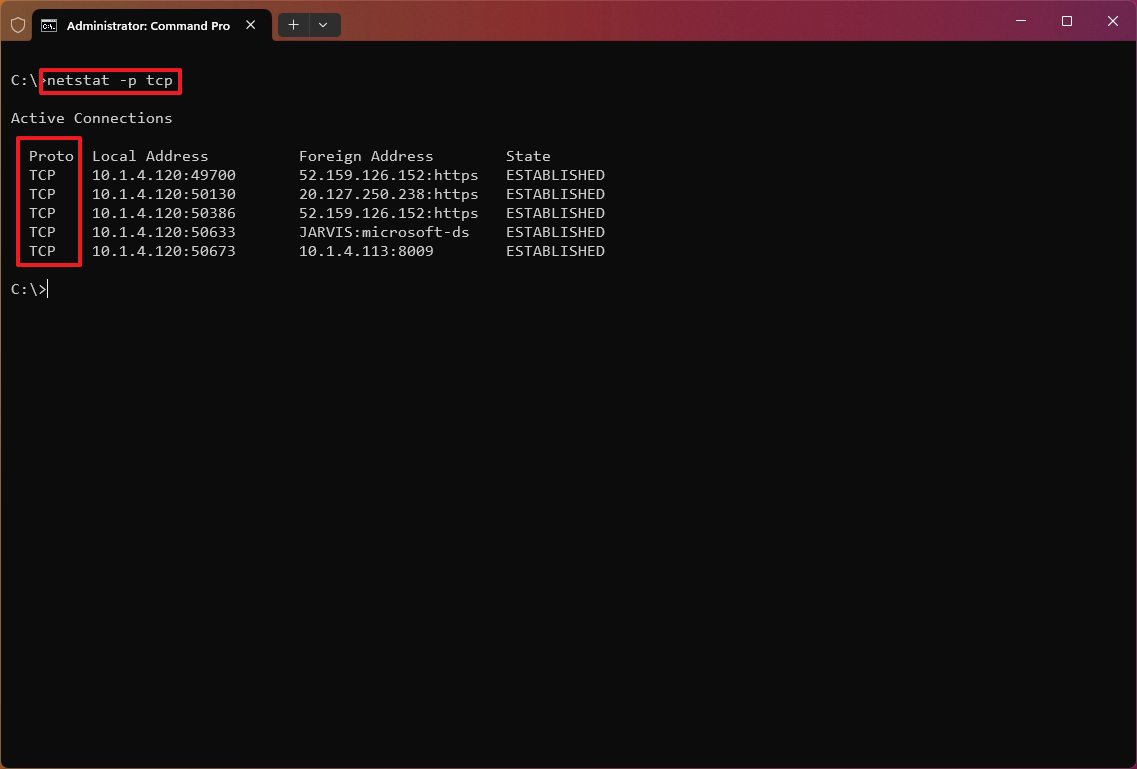
Show connections by Protocol
The "netstat -p" can be used to display connections per protocol that you have to specify using "TCP," "UDP," "TCPv6," or "UDPv6" next to the command. For example, you can use the "netstat -p TCP" command to view a list of TCP connections.
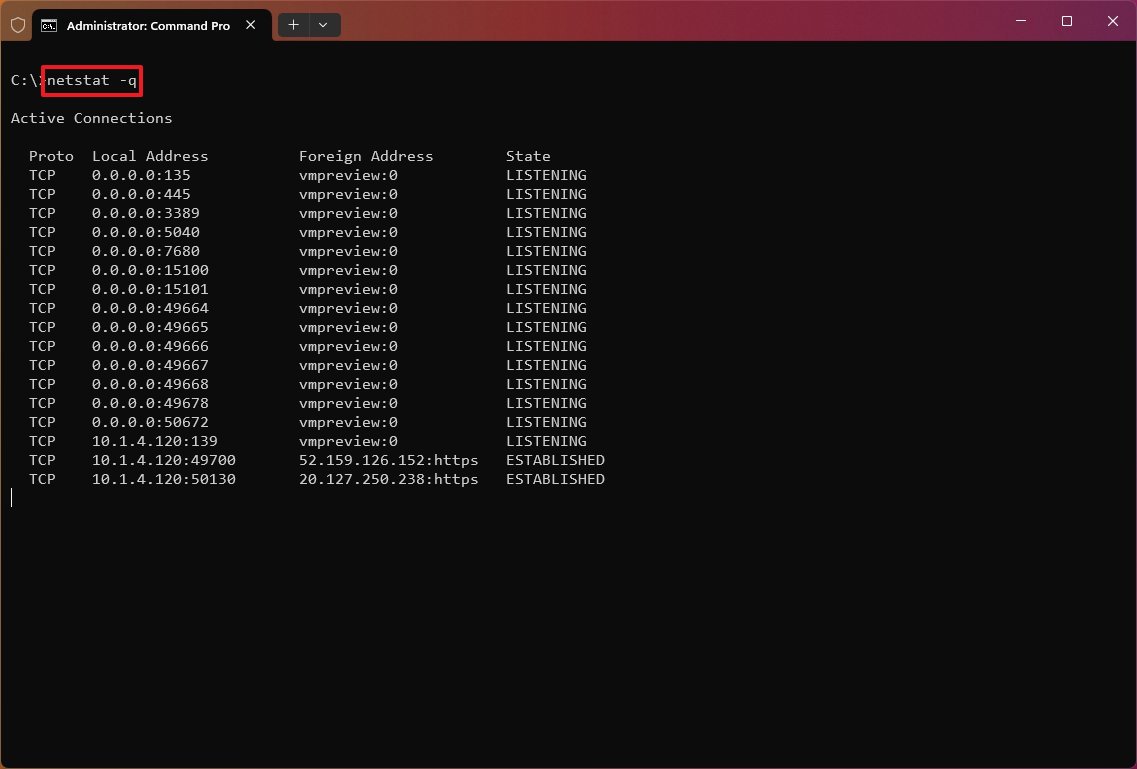
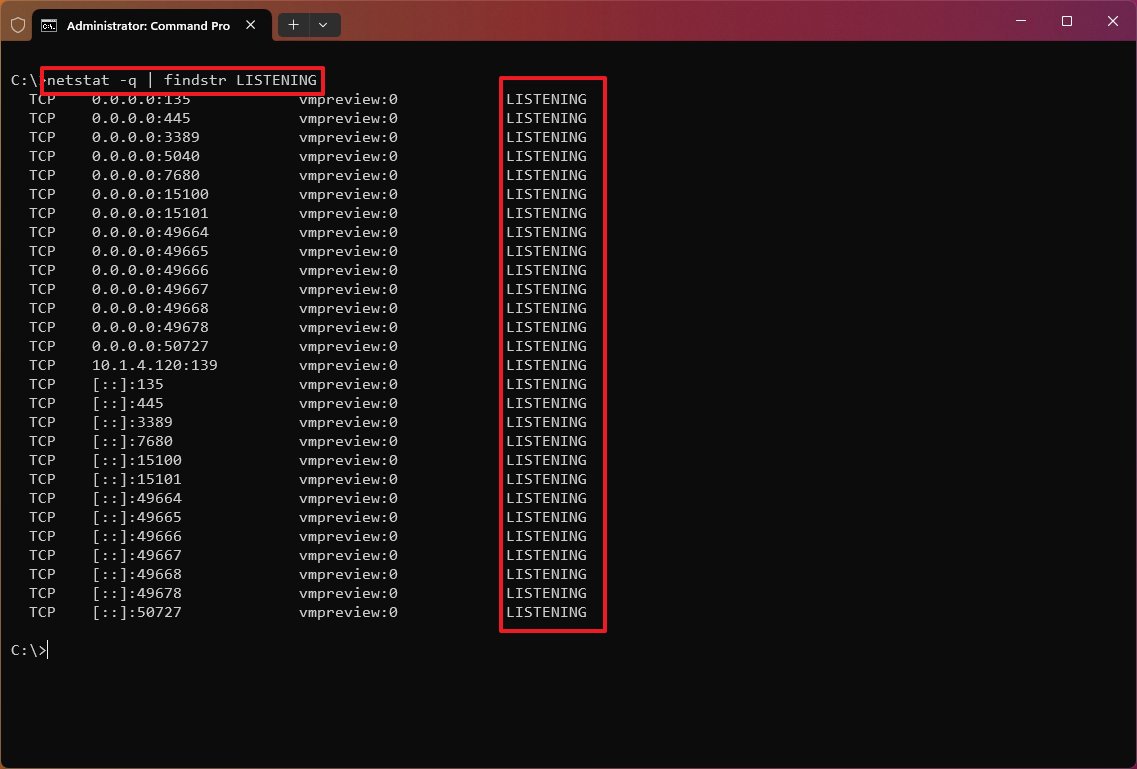
Show listening and non-listening ports
The "netstat -q" commands can produce a list of all the connections with the listening and bound non-listening ports.
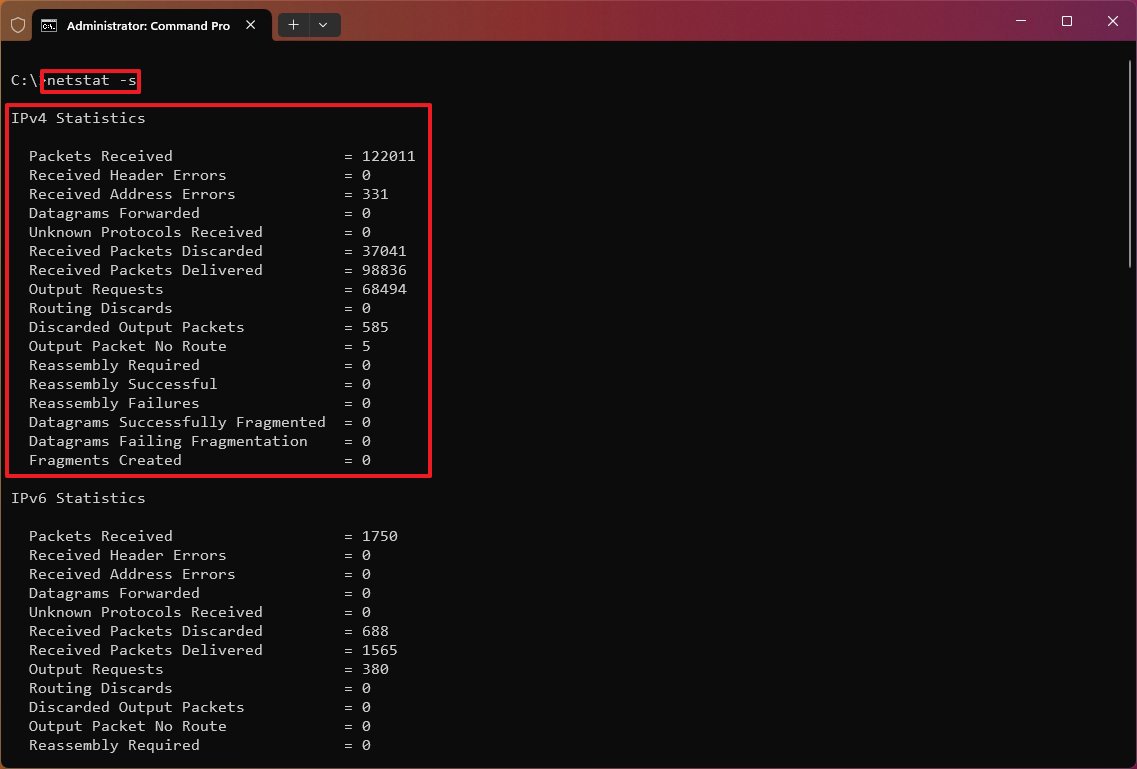
Show statistics by Protocol
The "netstat -s" shows network statistics for the available protocols, including TCP, UDP, ICMP, and IP protocols (versions 4 and 6).
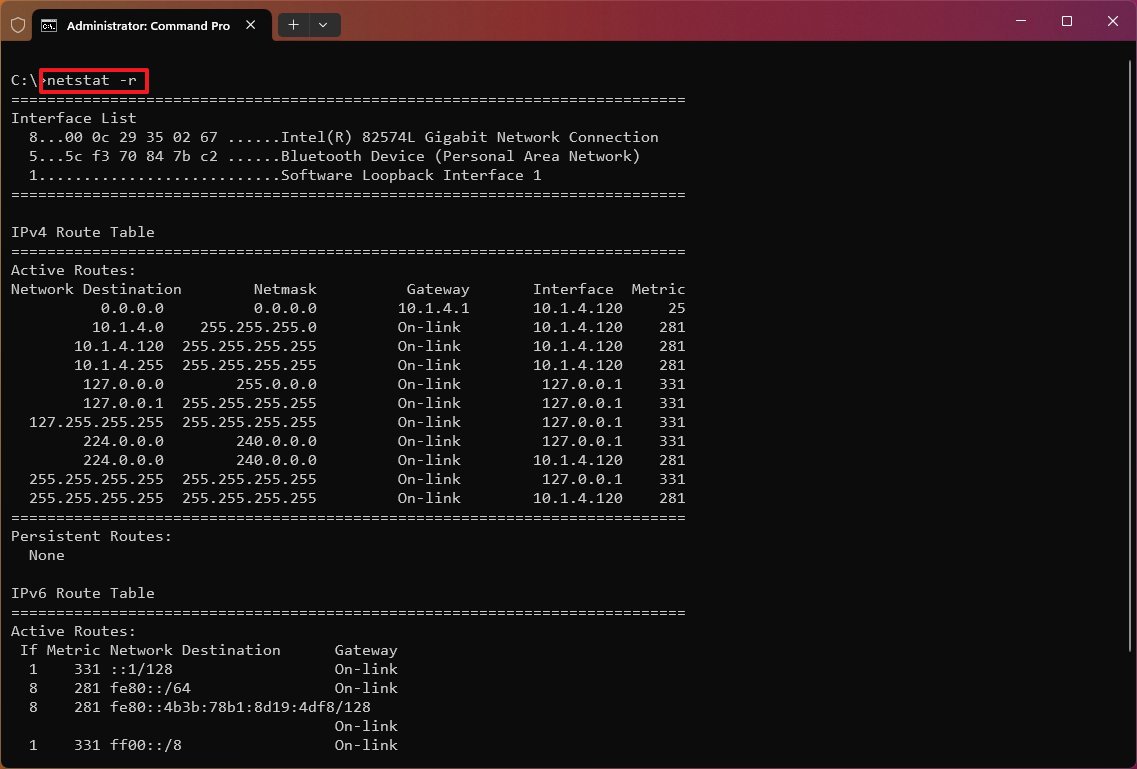
Show routing table
The "netstat -r" command displays the current network routing table that lists the routes to destinations and matrics known by the device for IP version 4 and version 6 (if applicable). If the returned information looks familiar, it's because you can also output the data using the "route print" command.
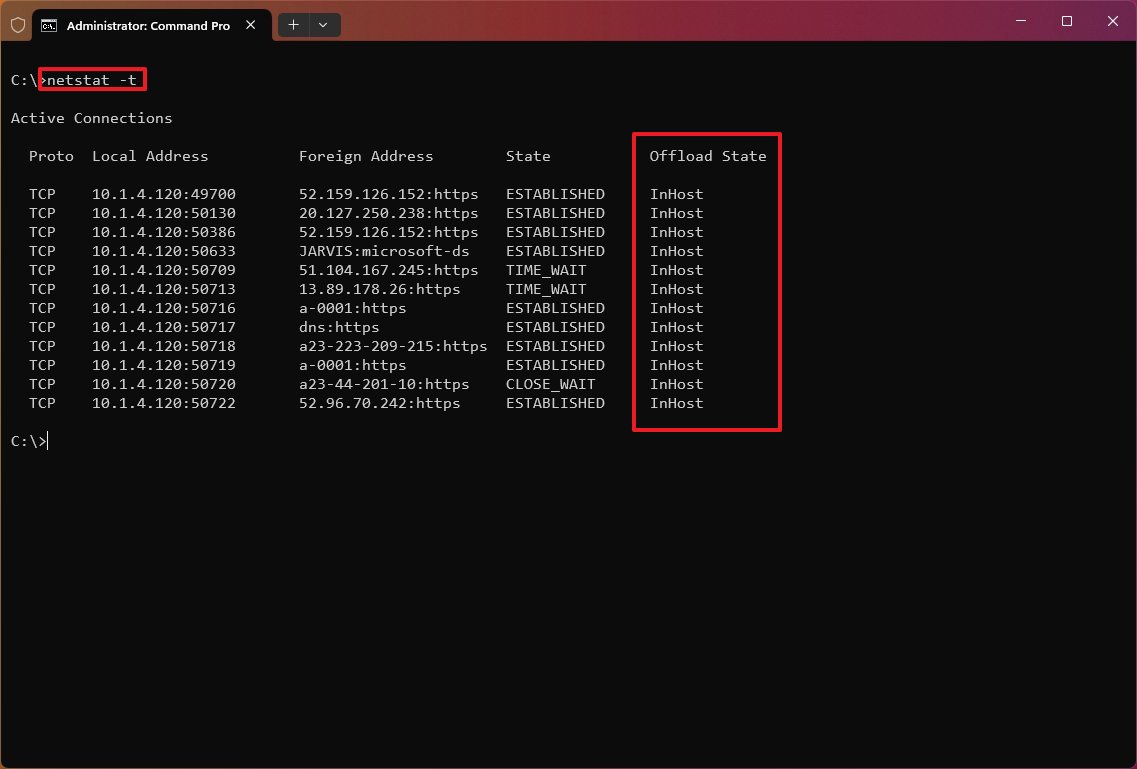
Show offload state connections
The "netstat -t" command generates a list of the current connection offload state. The offload state refers to the TCP Chimney Offload, which is a feature that transfers the network workload from the processor to the network adapter during data transmissions. The "InHost" value indicates that offloading isn't enabled, and the "Offload" means that the feature is transferring the workload to the network adapter. (This feature is only present on supported network adapters.)
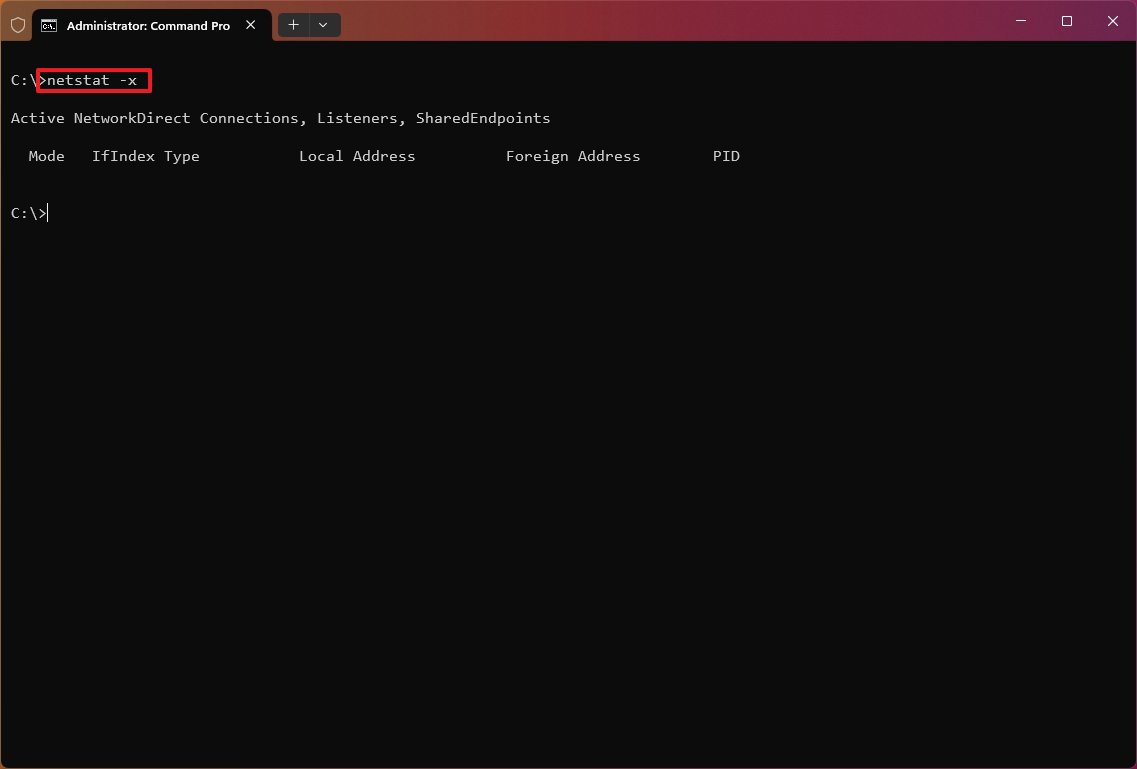
Show NetworkDirect connections
The "netstat -x" is another supported command, and it produces a list of NetworkDirect connections, shared endpoints, and listeners.
NetworkDirect is a specification for Remote Direct Memory Access (RDMA), which is a process that allows fast data transfers using the network adapter, freeing up the processor to perform other tasks. Usually, you'll never use this command unless you're using the Windows server version or a high-performance application with a network adapter that supports this feature.
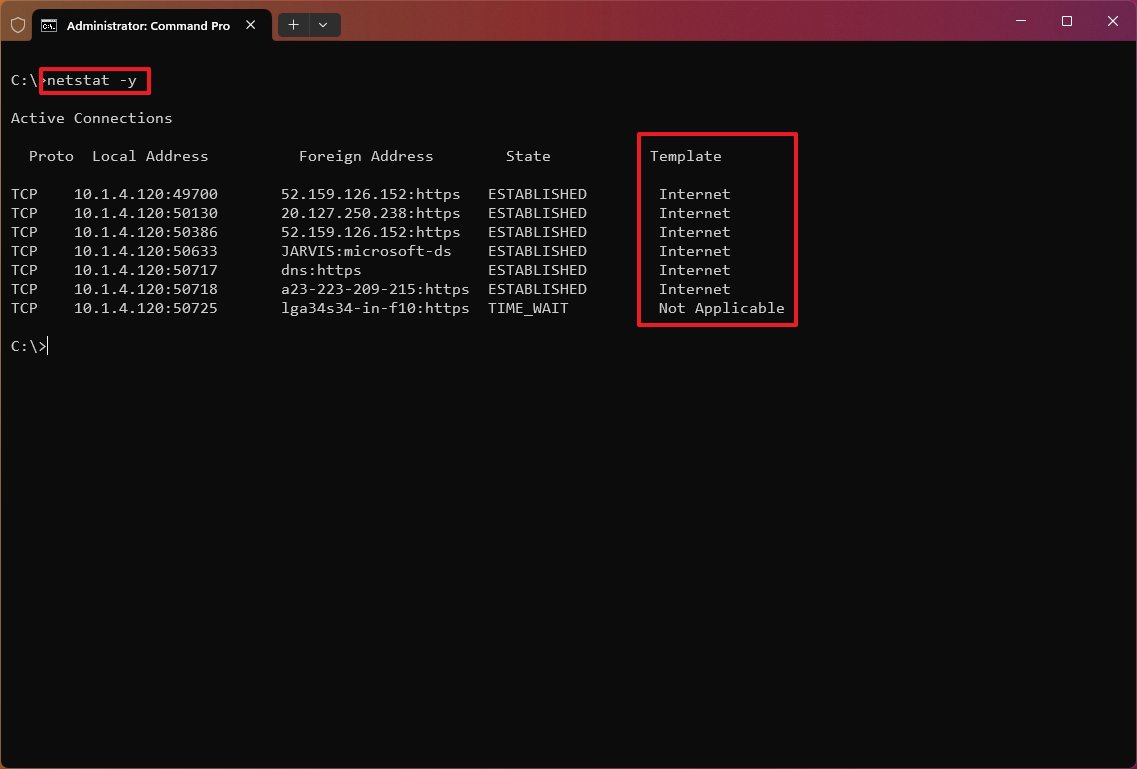
Show connection template
The "netstat -y" command displays TCP connection templates for all connections.
Combine parameters
When using the "netstat" command, you can combine the parameters to display various information for many cases.
For example, the "-e" parameter can also be used with the "-s" parameter to see statistics for each available protocol, and the "-o" parameter can be combined with "-a," "-n," and "-p" as necessary.
With the "netstat -p" command, you append the "s" parameter. You can display statistics from even more protocols, including "icmp," "ip," "icmpv6," and "ipv6."
Also, when using more than one parameter, you can combine them with a single "-." For example, instead of writing the command "netstat -e -s," you can write it like this: "netstat -es."
To see all the available parameters and additional help, you can always use the "netstat /?" command.
Netstat search
In addition to displaying all the available statistic information, you can also output only the certain details you need using these steps:
- Open Start.
- Search for Command Prompt, right-click the top result, and select the Run as administrator option.
- Type the following command to list all the connections that have the state set to LISTENING and press Enter: netstat -q | findstr STRING
In the command, replace "STRING" for the information you want to list. Also, the findstr option is case-sensitive, which means you must enter the string you want to find with the exact casing. This example lists the connections set to "LISTENING:" netstat -q | findstr LISTENING
This other example shows all the connections from a foreign server FQDN, in this case, Amazon: netstat -f | findstr amazon
The "findstr" command isn't part of the netstat tool. It's a simple command to search for a text string in a file, but you can use it with many of the options for this tool to make more sense of the information you're viewing.
The tool is not exclusive to Windows, as it's also available across platforms, including Linux and macOS. Even though the parameters and syntax may be different, they all are very similar.
More resources
For more helpful articles, coverage, and answers to common questions about Windows 10 and Windows 11, visit the following resources:
- Windows 11 on Windows Central — All you need to know
- Windows 10 on Windows Central — All you need to know

Mauro Huculak has been a Windows How-To Expert contributor for WindowsCentral.com for nearly a decade and has over 22 years of combined experience in IT and technical writing. He holds various professional certifications from Microsoft, Cisco, VMware, and CompTIA and has been recognized as a Microsoft MVP for many years.

 Windows Central Insider
Windows Central Insider