Microsoft warns Office 365 users: Don't fall for this phishing campaign
An active threat is making the rounds.
What you need to know
- A phishing campaign is going on right now.
- It's meant to con Office 365 users into giving up their credentials.
- Microsoft says to watch out for it.
Microsoft wants to alert you to a phishing scheme going on that involves the most classic of tricks, including barely misspelled domain names, URLs, and sender addresses. If you're hyper-vigilant of typos and tend to catch these things even when your spam filters fail to, you're all safe. But for everyone else who only takes a quick glance to verify whether an email is from a legitimate sender, Microsoft has a message: Look closer.
Here's what the Microsoft Security Intelligence Twitter account has to say about the most recent campaign: "An active phishing campaign is using a crafty combination of legitimate-looking original sender email addresses, spoofed display sender addresses that contain the target usernames and domains, and display names that mimic legitimate services to try and slip through email filters."
The original sender addresses contain variations of the word "referral" and use various top-level domains, including the domain com[.]com, popularly used by phishing campaigns for spoofing and typo-squatting.The original sender addresses contain variations of the word "referral" and use various top-level domains, including the domain com[.]com, popularly used by phishing campaigns for spoofing and typo-squatting.— Microsoft Security Intelligence (@MsftSecIntel) July 30, 2021July 30, 2021
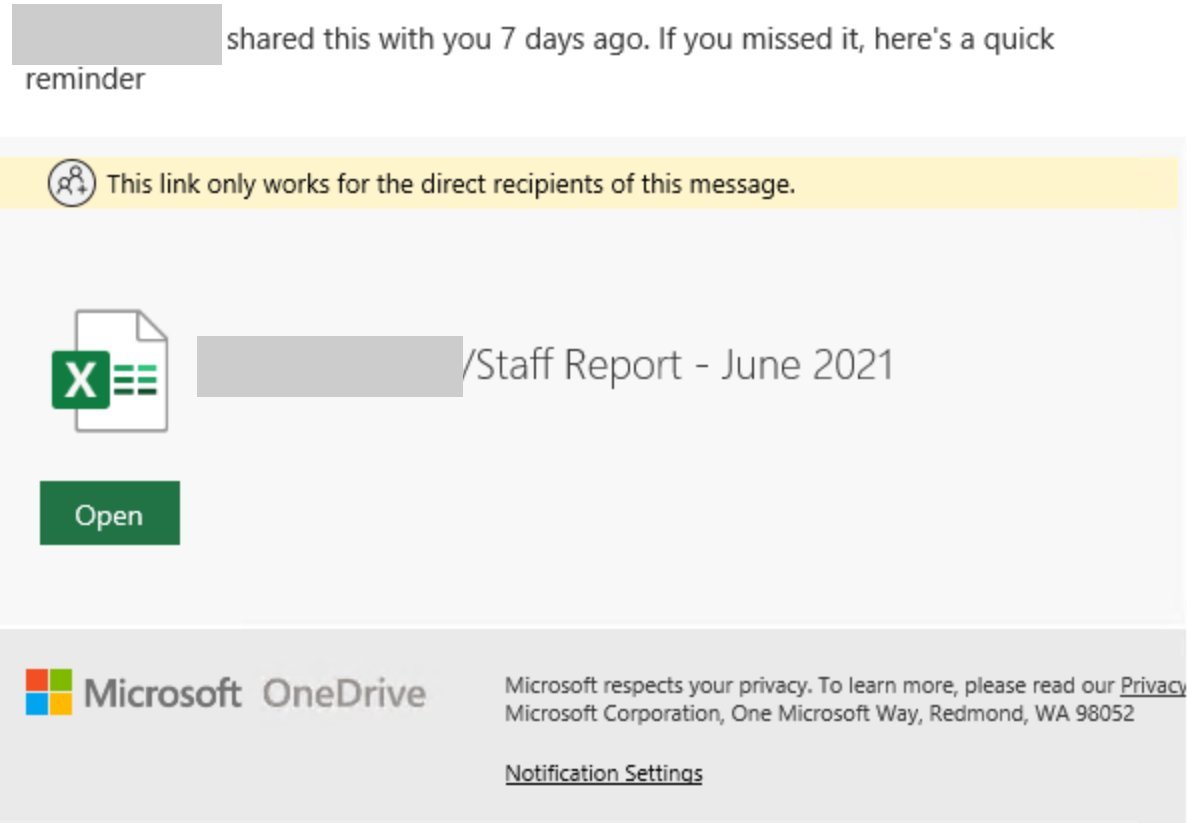
If you receive an email with file share requests for bonuses, staff reports, and related items, accompanied by a sketchy link, don't click on it. The URLs in these malicious emails are no good and can lead to an Office 365 phishing page where you'll be asked to type in your credentials. What makes these phishing efforts more tricky than usual is that "both URLs require sign-in to continue to the final page, bypassing many sandboxes." Furthermore, Microsoft says this particular phishing campaign utilizes other evasion techniques that make it hard to handle.


However, Microsoft isn't just alerting people to the threat; it's also offering assistance with hunting it down. You can grab Microsoft's advanced hunting query over on GitHub to make sure no phishing emails have snuck past gateways and endangered innocent inboxes.
All the latest news, reviews, and guides for Windows and Xbox diehards.

Robert Carnevale was formerly a News Editor for Windows Central. He's a big fan of Kinect (it lives on in his heart), Sonic the Hedgehog, and the legendary intersection of those two titans, Sonic Free Riders. He is the author of Cold War 2395.

 Windows Central Insider
Windows Central Insider









