How to encrypt data before storing it in the cloud (and why you should)
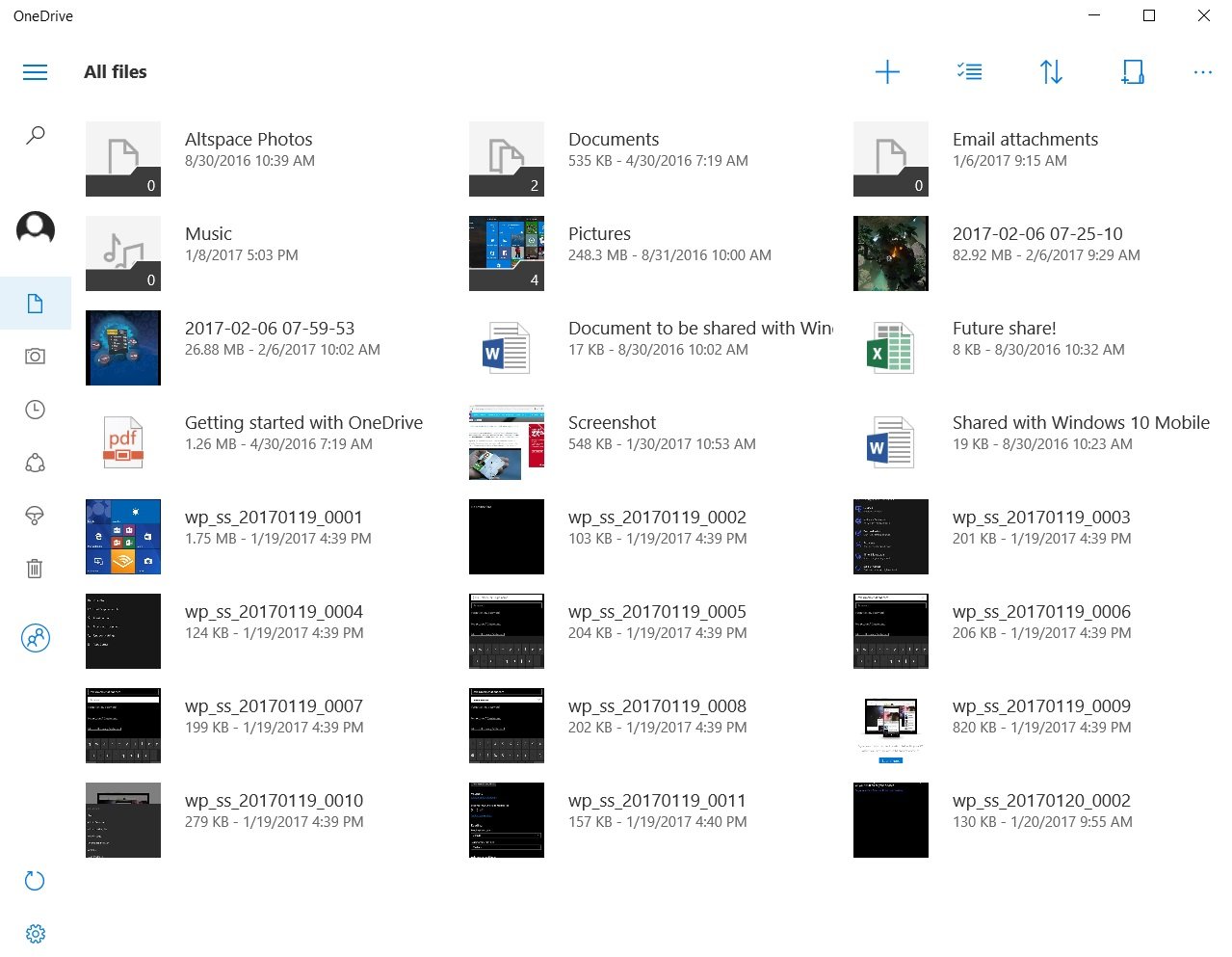
After another round of high-profile celebrity hacks, it's clear that cloud storage isn't exactly as safe as it's made out to be. It's easy to sync your files with a service such as OneDrive or Dropbox, but it's also easy to forget about those files down the road. You may have deleted some sensitive photos from your phone, but they still ended up synced in the cloud, and now they're in the hands of a hacker.
Let's take a look at how your cloud data can be potentially compromised and how you can add another layer of protection by encrypting them before they reach the cloud.
Cloud-storage encryption
There are two forms of encryption when you're dealing with cloud storage services: transit and resting. When your files travel between your PC and a cloud service, the files and folders you upload are generally encrypted with at least 128-bit secure sockets layer (SSL) technology.


When your data is resting in storage, however, there is less of a chance that it will have encryption, and if it does, the cloud service will likely hold the key. In the case of OneDrive, only those with a business subscription can take advantage of resting encryption. Dropbox, on the other hand, provides resting 256-bit encryption, but it holds the encryption keys.
Encryption of your data, while it's in transit and comfy in the cloud, works great against brute-force attacks. It would take a supercomputer years to crack the 256-bit encryption. It's much more likely that failure on the user side will involve a phishing attack or a weak password that can be guessed by an interested party. If your account can be accessed through the front door, decryption isn't necessary.
Keeper of the encryption keys
To otherwise unscramble the encrypted data, a key is needed. Each time data is encrypted, one of these keys is created and is saved somewhere. Many online backup services — which are separate from cloud-sync services — let you create the encryption key and take responsibility for keeping it safe. If you lose the key, say goodbye to your backed up data.
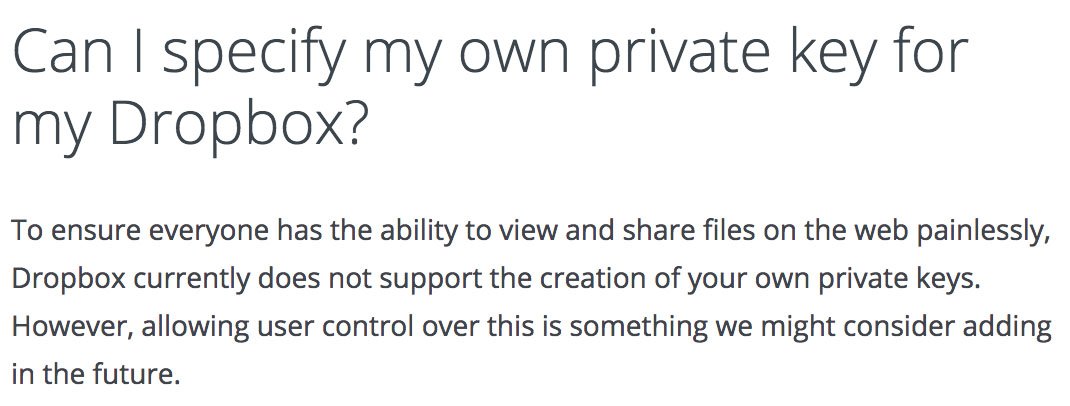
Cloud storage services used for syncing and sharing, such as Dropbox, do not provide users with the option to create their own encryption keys. It's up to the user to trust the service with creating and safeguarding the key. There's less of a chance that you'll end up locked out forever because you forgot that key, but there's also a chance that the service itself will be compromised, in which case the entire thing is out of your hands. Bottom line: No matter how careful you are, things can go wrong when someone else holds the keys.
All the latest news, reviews, and guides for Windows and Xbox diehards.
Encrypt your data before it reaches the cloud
Some people refuse to use cloud storage because of security concerns. Others claim they have nothing to hide and wouldn't care if their files were released to the general public. Regardless of your opinion, it's not a bad idea to use protection on the internet. It's not getting any safer out there, and people can take advantage of the smallest bits of information.
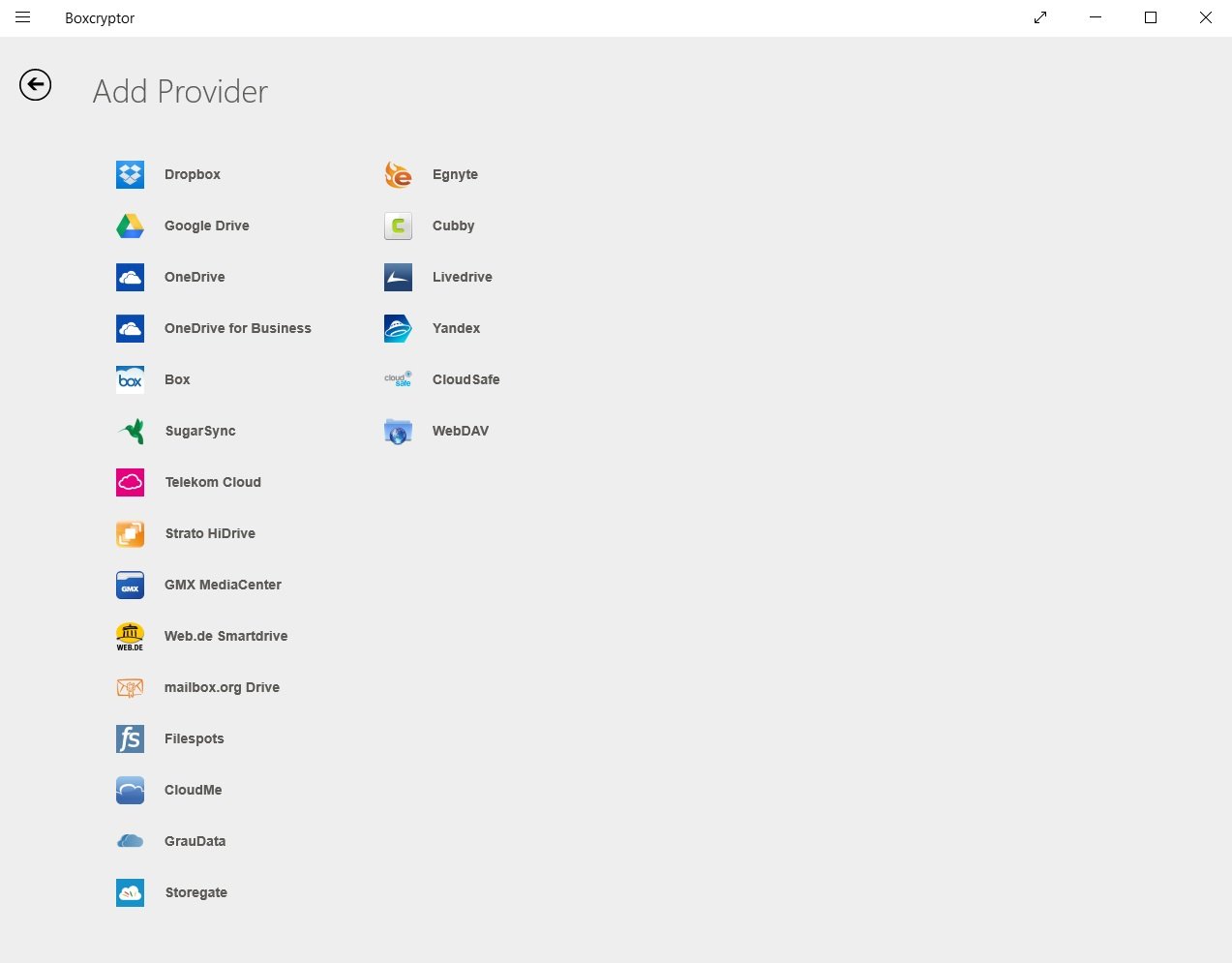
Yes, it's just another thing you have to worry about, but encrypting your data yourself before sending it to the cloud will help protect you. You don't have be a whiz to perform this extra step. Encryption software is generally easy to use, you can create a unique encryption key that only you hold, and most options work well with popular cloud-storage services. Even if you don't want to pay, there are plenty of free encryption tools out there.
Services such as AxCrypt and Folder Lock, both of which are PCMag editors' choices, have free, basic versions of their software, and they also offer paid subscriptions that come with plenty more features, including local disk encryption to help keep things safe on your end.
There are a ton of free alternatives that can encrypt one file at a time before sending them to the cloud. 7Zip and Boxcryptor are standouts in this arena.
More resources
For more information on creating strong passwords and avoiding phishing, check out our full guide on how to ensure your cloud data remains safe. And if you're interested in full cloud backups of your PC, have a look at our choice for the best online backup service.

Cale Hunt brings to Windows Central more than nine years of experience writing about PC gaming, Windows laptops, accessories, and beyond. If it runs Windows or in some way complements the hardware, there’s a good chance he knows about it, has written about it, or is already busy testing it.

 Windows Central Insider
Windows Central Insider